Comprehensive Security Monitoring and Analytics Solutions
As a global leader in cyber security, we aim at providing the best-in-class security monitoring and analysis through anomaly detection & investigation and remediation of the broadest range of security threats across on-premises and cloud IT assets.
We have years together experience in monitoring global, regional and local threat feeds, analyze user and network behaviour both on a real-time and historical basis. Through threat intelligence, active defence measures and advanced big data analytics, our professionals can identify the root causes of threats from the recorded reports.
Our ability to detect and cluster these root causes from inside and outside the organization empowers us to generate actionable intelligence for denying, degrading and disrupting the full spectrum of advanced threats.
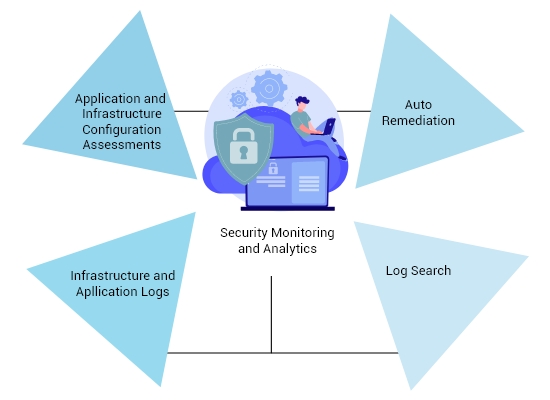
SERVICE OFFERINGS
Prevention is Better than Recovery
Commit your security operations to us and stay peacefully. We take of protecting your organization through identifying threats in real-time, responding to security threats instantly, security configurations, and monitoring drifts across your cloud environments.
As our security platform undergoes deep investigations, you can proactively act on security incidents and quickly drive to resolution when security incidents do occur.

Some of the Networking solutions we provide are:
Lorem Ipsum is simply dummy text of the printing and typesetting industry. Lorem Ipsum has been the industry’s standard dummy text ever since the 1500s, when an unknown printer took a galley of type and scrambled it to make a type specimen book.
- Design & Implementation of LAN/WAN (Structured/Semi-Structured/Normal)
- Network Auditing along with assessment of current setup
- Site Planning via operation research techniques & scheduled cable blueprinting
- Structured Cabling
- Optimization of network resources
- Network Management
- Network Security Planning & Implementation
- Networking Switches
- Switching Rack & Server Rack
- Firewall
 Read More
Read More