In today’s complex cybersecurity landscape, organizations face an ever-growing array of threats. Security Information and Event Management (SIEM) has emerged as a critical technology for detecting, analyzing, and responding to security incidents in real-time. This comprehensive guide explains what SIEM is, how it works, and why it’s essential for modern security operations—while addressing the challenges of implementation.
What is SIEM?

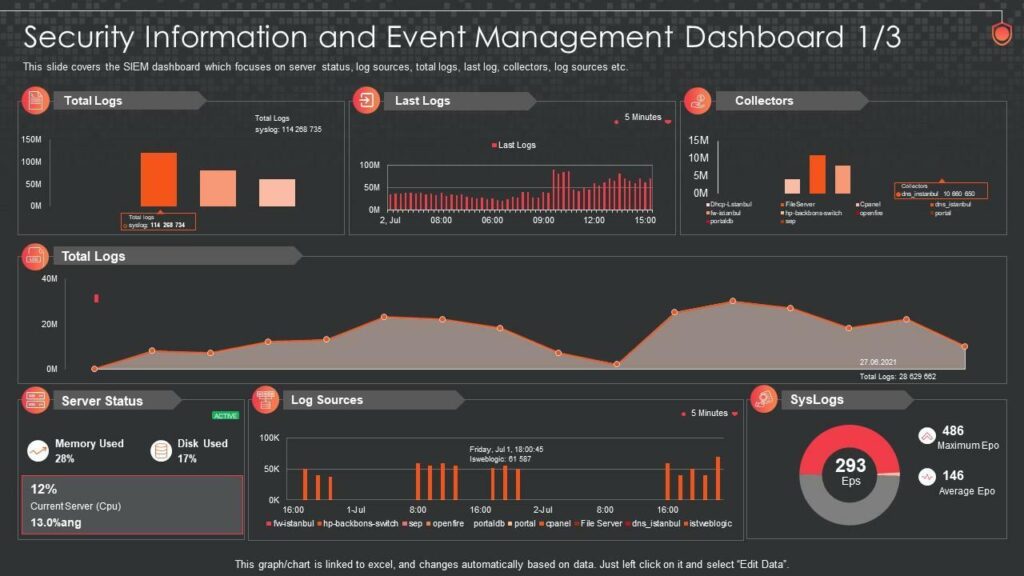
A modern SIEM dashboard provides visibility into security events across an organization’s infrastructure
Security Information and Event Management (SIEM) is a comprehensive cybersecurity solution that provides real-time analysis of security alerts generated by various hardware and software systems within an organization. Think of SIEM as the central nervous system of your security operations—it collects, normalizes, and analyzes data from multiple sources to identify potential security threats. SIEM also plays an important role in compliance and auditing, helping organizations meet regulatory requirements by storing and reporting security logs. Overall, SIEM improves visibility, reduces response time, and strengthens an organization’s security posture. By bringing these functions together, SIEM provides organizations with a holistic view of their security posture, enabling faster threat detection and more effective incident response.
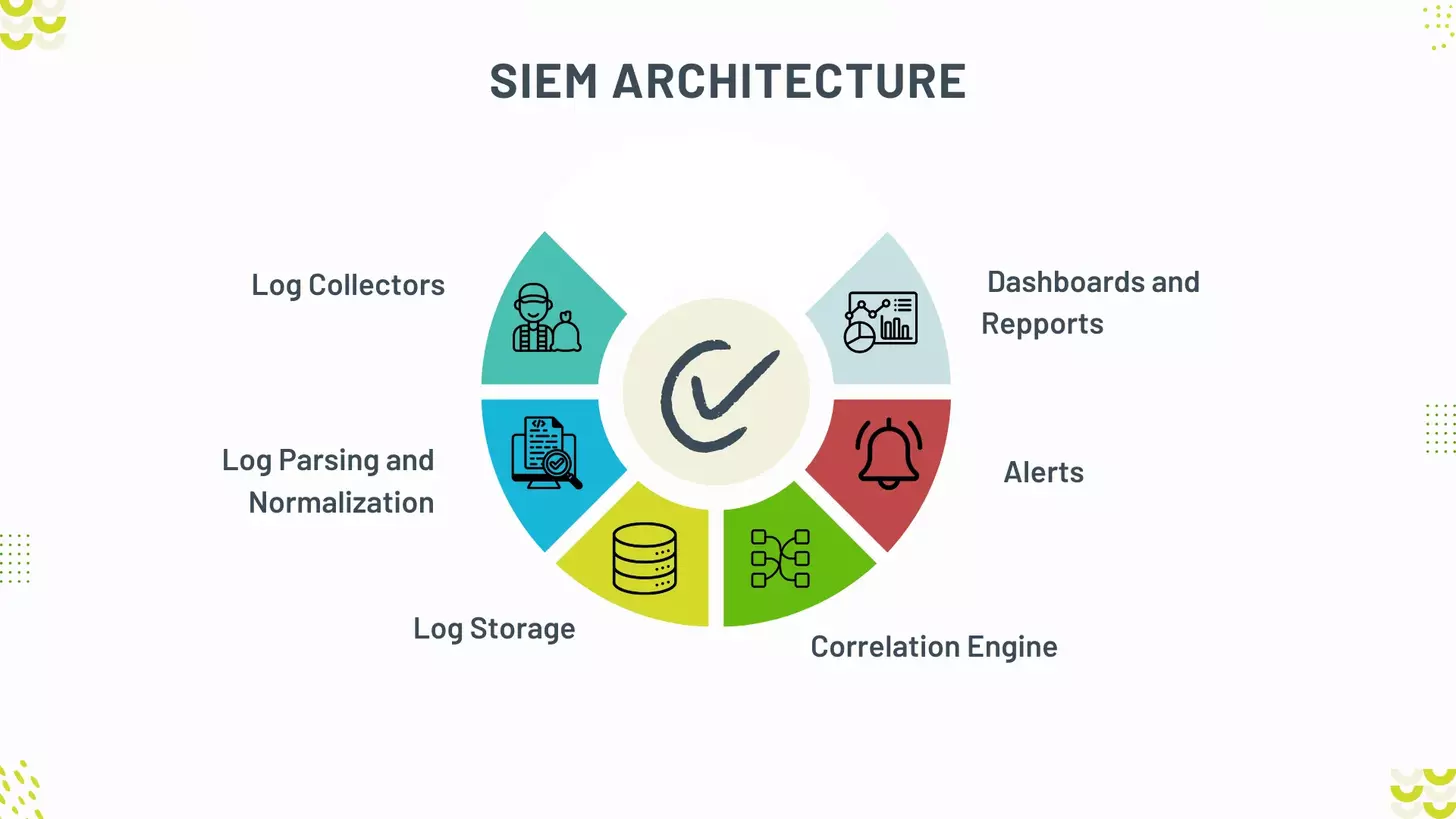
How SIEM Works: A Three-Step Process
1. Data Collection

SIEM systems collect data from across your entire IT infrastructure. This includes logs from servers, network devices, security devices (firewalls, antivirus, IDS/IPS), applications, and cloud services. The system aggregates this data in a central location for processing.
2. Normalization & Correlation
Once collected, SIEM normalizes the data into a consistent format. It then applies correlation rules and analytics to identify patterns, anomalies, and potential security incidents by connecting seemingly unrelated events across different systems.
3. Alerting & Reporting
Based on the analysis, SIEM generates alerts for security teams when suspicious activities are detected. It also provides reporting capabilities for compliance purposes and security posture assessment, offering both real-time monitoring and historical analysis.
Core Functions & Key Capabilities of SIEM
Log Management
SIEM systems collect, store, and manage log data from various sources, providing a centralized repository for security information. This enables both real-time analysis and historical investigation of security events.
Event Correlation
By analyzing data from multiple sources, SIEM can identify relationships between seemingly isolated events. This correlation helps detect complex attack patterns that might otherwise go unnoticed when looking at individual logs.
Alerting
When suspicious activities or policy violations are detected, SIEM systems generate alerts to notify security teams. These alerts can be customized based on specific rules and thresholds to reduce false positives and focus on genuine threats.
Dashboards
SIEM solutions provide visual dashboards that offer a real-time overview of an organization’s security posture. These intuitive interfaces help security analysts quickly identify and respond to potential threats.
Reporting
Comprehensive reporting capabilities allow organizations to document security incidents, track trends, and measure the effectiveness of security controls over time.
Compliance
SIEM helps organizations meet regulatory requirements by providing audit trails and compliance reports. This is particularly valuable for industries subject to regulations like HIPAA, PCI DSS, GDPR, and SOX.
Benefits of Implementing SIEM

Enhanced Threat Detection
SIEM provides real-time monitoring and analysis of security events across your entire IT infrastructure. By correlating data from multiple sources, it can detect sophisticated threats that might otherwise go unnoticed, including advanced persistent threats (APTs) and insider threats.
Improved Incident Response
With centralized visibility into security events, SIEM enables faster and more effective incident response. Security teams can quickly investigate alerts, understand the scope of an incident, and take appropriate remediation actions before significant damage occurs.
Streamlined Compliance
SIEM solutions simplify compliance with various regulatory requirements by providing automated log collection, retention, and reporting capabilities. This helps organizations demonstrate compliance during audits and reduces the manual effort required for compliance reporting.
Evolution of Modern SIEM Solutions
SIEM technology has evolved significantly since its introduction in 2005. Today’s modern SIEM solutions incorporate advanced capabilities that go beyond traditional log management and correlation:
User and Entity Behavior Analytics (UEBA)
Modern SIEM solutions leverage machine learning to establish baselines of normal user and entity behavior. This enables the detection of anomalous activities that might indicate compromised accounts or insider threats, even when traditional rule-based detection would fail.
Security Orchestration, Automation and Response (SOAR)
Many SIEM platforms now include SOAR capabilities that automate routine security tasks and orchestrate response actions across multiple security tools. This helps security teams respond more quickly and consistently to incidents while reducing manual workload.
Threat Intelligence Integration
Today’s SIEM solutions can incorporate threat intelligence feeds to provide context about known threats and indicators of compromise. This helps security teams prioritize alerts and respond more effectively to emerging threats.
Cloud and Hybrid Deployment
Modern SIEM solutions support cloud and hybrid environments, enabling organizations to monitor security across on-premises infrastructure, cloud services, and SaaS applications from a single platform.
Top Challenges in Implementing SIEM Solutions
While SIEM offers significant security benefits, organizations often face challenges during implementation. Understanding these challenges is crucial for planning a successful SIEM deployment:
1. Configuration Complexity
Configuring a SIEM system to meet specific organizational needs can be highly complex. Determining which data sources to integrate, setting up correlation rules, and fine-tuning alert thresholds require meticulous attention to detail. Configuration errors can lead to false positives or missed threats, emphasizing the importance of skilled personnel during this crucial phase.
2. Integration Hurdles
SIEM tools must integrate seamlessly with existing security tools and systems. The lack of compatibility can hinder the SIEM’s ability to provide a holistic view of security events. This integration process involves assessing the organization’s existing infrastructure, ensuring data flows smoothly between systems, and establishing necessary protocols for data sharing.
3. Resource Constraints
Implementing SIEM solutions is resource-intensive, demanding significant investment in time, money, and skilled personnel. Smaller organizations with limited budgets may struggle to allocate the necessary resources for a successful SIEM deployment, requiring careful prioritization of cybersecurity needs.
4. Hidden Costs
While SIEM promises enhanced security, hidden costs can surface when the volume of data exceeds expectations. As organizations grow, the expense of processing and storing vast amounts of SIEM log data can catch them off guard, straining budgets and disrupting the implementation process.
5. Data Onboarding Challenges
Ensuring all relevant data sources are properly onboarded into the SIEM system can be a significant implementation burden. Different systems and applications may have varying log formats and data structures, making the process of data normalization and standardization critical for effective threat detection.
6. Scalability Limitations
Organizations, especially those experiencing rapid growth, need SIEM solutions that can scale with them. Ensuring the SIEM system can handle increasing volumes of log data and events is crucial for long-term success, as performance issues and incomplete event capture can compromise security effectiveness.

Define Clear Objectives
Begin by establishing clear and specific objectives for your SIEM deployment. What security gaps are you trying to address? Which compliance requirements must you meet? Having well-defined goals helps maintain focus and avoid scope creep during implementation.
Start Small and Scale
Rather than attempting to implement all SIEM capabilities at once, start with a focused approach. Begin with critical systems and high-priority use cases, then gradually expand as your team gains experience and confidence with the solution.
Invest in Training
SIEM tools are powerful but complex. Invest in comprehensive training for your security team to ensure they can effectively configure, operate, and maintain the SIEM system. This includes understanding how to interpret alerts, investigate incidents, and tune the system to reduce false positives.
Plan for Data Management
Develop a clear strategy for data collection, normalization, storage, and retention. Determine which data sources are most valuable for security monitoring and compliance, and establish appropriate retention periods based on both security needs and regulatory requirements.
Establish Clear Processes
Define clear processes for alert triage, incident investigation, and response. Document these procedures and ensure all team members understand their roles and responsibilities when security incidents occur.
Regular Review and Optimization
SIEM is not a “set and forget” solution. Schedule regular reviews to assess the effectiveness of your SIEM implementation, tune correlation rules, adjust alert thresholds, and incorporate new data sources as your environment evolves.
Common SIEM Use Cases
Threat Detection and Response
SIEM enables real-time detection of security threats by correlating events across multiple systems. Security teams can quickly identify potential incidents, investigate their scope and impact, and take appropriate remediation actions.
Compliance Management
Organizations can use SIEM to demonstrate compliance with various regulatory requirements, such as HIPAA, PCI DSS, GDPR, and SOX. SIEM provides the necessary log collection, retention, and reporting capabilities to satisfy auditors and regulators.
Insider Threat Detection
By monitoring user activities and establishing behavioral baselines, SIEM can help identify suspicious actions that might indicate insider threats, such as unauthorized access to sensitive data or unusual data transfers.
Forensic Investigation
When security incidents occur, SIEM provides valuable forensic data for investigation. Security teams can reconstruct the timeline of events, understand the attack vector, and determine the extent of the compromise.
Security Posture Assessment
SIEM offers visibility into an organization’s overall security posture by monitoring security controls, identifying vulnerabilities, and tracking remediation efforts. This helps security leaders make informed decisions about security investments and priorities.
Operational Monitoring
Beyond security, SIEM can provide insights into IT operations by monitoring system performance, availability, and capacity. This helps organizations identify and address operational issues before they impact business services.
Future Trends in SIEM Technology

AI and Machine Learning
Artificial intelligence and machine learning are becoming increasingly central to SIEM solutions. These technologies enable more accurate threat detection, reduce false positives, and automate routine security tasks, allowing security teams to focus on more complex challenges.
Cloud-Native SIEM
As organizations continue to migrate to the cloud, SIEM solutions are evolving to become cloud-native. This approach offers greater scalability, flexibility, and cost-effectiveness, while also providing better visibility into cloud environments.
Extended Detection and Response (XDR)
The integration of SIEM with extended detection and response (XDR) capabilities is a growing trend. XDR extends the visibility and analytics of SIEM across endpoints, networks, and cloud environments, providing more comprehensive threat detection and response.
Conclusion: The Value of SIEM in Modern Cybersecurity
Security Information and Event Management (SIEM) is a critical foundation for modern cybersecurity, enabling organizations to gain real-time visibility, detect threats faster, and meet compliance requirements. When implemented effectively, SIEM turns complex security data into clear, actionable intelligence.
With Atrity, organizations can simplify SIEM adoption and maximize its value. Atrity delivers tailored SIEM solutions backed by deep cybersecurity expertise, helping businesses strengthen their security posture, respond confidently to threats, and stay resilient in an ever-evolving threat landscape. By partnering with Atrity, organizations are better prepared to secure today’s environments and tomorrow’s challenges.
 Read More
Read More