Understanding Digital Assets and Why They Require Advanced Protection
Digital assets encompass far more than traditional data files. They represent tangible business value stored in electronic format, including cryptocurrencies, digital tokens, customer databases, trade secrets, source code, and brand reputation across social platforms. Each category demands specialized protection strategies.
The value of digital assets continues to grow exponentially. Intellectual property alone accounts for over eighty percent of business valuation for technology companies. Meanwhile, cryptocurrency holdings represent trillions in global market capitalization. When these assets face compromise, the consequences extend beyond immediate financial loss to include regulatory penalties, customer trust erosion, and competitive disadvantage.
Traditional security approaches focused primarily on perimeter defense.Firewalls, antivirus software, and password protection formed the foundation of cybersecurity strategies. However, modern threats operate differently. Attackers now target human vulnerabilities through phishing campaigns, exploit cloud misconfigurations, and use sophisticated malware that evades signature-based detection systems.
The shift toward remote work and cloud infrastructure has exponentially expanded the attack surface. Digital assets no longer reside behind clearly defined network boundaries. They flow across multiple cloud platforms, mobile devices, and third-party systems. This distributed architecture requires fundamentally different security protocols that provide protection regardless of asset location.
Core Advanced Security Protocols for Digital Asset Protection
Advanced security protocols represent the evolution of cybersecurity practices designed to address contemporary threats. These protocols combine technical controls, administrative policies, and continuous monitoring to create comprehensive defense systems. Understanding each protocol’s purpose and implementation is crucial for effective digital asset protection.
Multi-Factor Authentication and Hardware Security Keys
Passwords alone provide insufficient protection in modern security environments. Multi-factor authentication adds critical verification layers that dramatically reduce unauthorized access risk. This security protocol requires users to provide multiple forms of identity verification before granting system access.
The most effective MFA implementations combine something you know (password), something you have (security token or mobile device), and something you are (biometric data). This approach ensures that even if attackers compromise one authentication factor, they cannot gain access without obtaining the remaining factors.
Hardware security keys represent the strongest form of multi-factor authentication available today. These physical devices generate cryptographic signatures that cannot be phished or remotely compromised. Organizations protecting high-value digital assets should mandate hardware security keys for all privileged accounts and sensitive system access.
Implementation requires careful planning. Businesses must balance security requirements with user experience considerations. The goal is creating friction for attackers while maintaining workflow efficiency for legitimate users. Modern authentication protocols support risk-based approaches that adjust security requirements based on access context.
End-to-End Encryption for Data Protection
Encryption transforms readable data into scrambled code that only authorized parties can decipher. End-to-end encryption ensures that data remains protected throughout its entire lifecycle, from creation through transmission to storage. This protocol prevents unauthorized parties from accessing sensitive information even if they intercept communications or breach storage systems.
Modern encryption standards utilize complex mathematical algorithms that would require centuries to break using current computing power. Advanced Encryption Standard with 256-bit keys provides military-grade protection suitable for the most sensitive digital assets. Organizations handling financial data, healthcare records, or intellectual property should implement encryption as a foundational security measure.
The challenge lies in encryption key management. Keys represent the digital equivalent of physical safe combinations. Organizations must implement robust key management systems that securely generate, store, rotate, and retire encryption keys throughout their lifecycle. Compromised keys can undermine entire encryption implementations regardless of algorithm strength.
Transport Layer Security protocols protect data during transmission across networks. These protocols create encrypted tunnels between communicating systems, preventing eavesdropping and man-in-the-middle attacks. Businesses must ensure all systems handling sensitive data implement current TLS versions and disable outdated protocols that contain known vulnerabilities.
Encryption Best Practices
- – Implement AES-256 encryption for data at rest across all storage systems
- – Use TLS 1.3 or higher for all network communications
- – Deploy hardware security modules for encryption key storage
- – Establish automated key rotation schedules every ninety days
- – Maintain secure offline backups of encryption keys
- – Implement certificate pinning for mobile applications
- – Use perfect forward secrecy to protect past communications
Zero-Trust Security Architecture
Traditional security models operated on the principle of trusted internal networks and untrusted external networks. Once users gained access inside the perimeter, they received broad system permissions. This approach fails catastrophically in modern environments where threats originate both externally and internally, and where network boundaries have dissolved.
Zero-trust security architecture operates on a fundamentally different principle. Never trust, always verify. This model assumes breach is inevitable and designs security controls accordingly. Every access request undergoes rigorous verification regardless of origin. Users receive minimum necessary permissions for specific tasks and time periods.
Implementation involves several key components. Identity verification occurs continuously rather than once at login. Network segmentation isolates critical assets and limits lateral movement. Systems log all access attempts for analysis. Anomaly detection identifies suspicious behavior patterns that might indicate compromise.
The benefits extend beyond security improvements. Zero-trust architectures provide better visibility into system access patterns, simplify compliance auditing, and reduce the blast radius when breaches occur. Organizations transitioning to cloud infrastructure find zero-trust models naturally align with distributed computing environments.
Zero-Trust Implementation Timeline: Most organizations require twelve to eighteen months for complete zero-trust architecture deployment. The process involves identity system modernization, network segmentation, policy development, and extensive testing. Phased rollouts minimize disruption while progressively improving security posture.
Emerging Advanced Security Protocols: Blockchain, Biometrics, and AI
Blockchain-Based Security and Decentralized Custody
Blockchain technology provides revolutionary approaches to digital asset protection through its fundamental characteristics of immutability, transparency, and decentralization. These properties create security advantages that traditional centralized systems cannot match. Understanding blockchain security protocols is essential for organizations managing cryptocurrency assets and exploring decentralized applications.
Decentralized custody solutions distribute private key management across multiple parties or systems. This approach eliminates single points of failure that plague centralized storage. Multi-signature wallets require multiple authorized parties to approve transactions, preventing unauthorized asset transfers even if individual keys become compromised.
Smart contracts enable automated security policies that execute without human intervention. These self-enforcing agreements can implement complex access controls, time-locked transfers, and conditional release mechanisms. Organizations can program asset protection rules directly into blockchain infrastructure, reducing reliance on trusted intermediaries.
The challenge involves balancing security with accessibility. Overly complex custody arrangements can lock organizations out of their own assets if key holders become unavailable. Proper implementation requires carefully designed recovery mechanisms, clear governance policies, and regular testing of access procedures.
Biometric Authentication Systems
Biometric authentication leverages unique physical characteristics to verify identity with unprecedented accuracy. Fingerprint scanning, facial recognition, iris detection, and voice analysis provide authentication factors that users cannot forget, lose, or easily share. These systems offer significant security advantages over traditional password-based approaches.
Modern biometric systems employ liveness detection to prevent spoofing attacks using photographs, masks, or recorded audio. Advanced sensors analyze microscopic skin patterns, detect blood flow, and identify three-dimensional facial structure. These anti-spoofing measures ensure that only live, present individuals can authenticate.
Organizations must address privacy concerns when implementing biometric systems. Biometric data represents personally identifiable information that requires careful protection. Best practices include storing only biometric templates rather than raw biometric data, implementing strong encryption for biometric databases, and providing clear user consent mechanisms.
The technology continues evolving rapidly. Behavioral biometrics analyze typing patterns, mouse movements, and device interaction behaviors to create continuous authentication systems. These passive verification methods operate transparently, identifying users throughout sessions without requiring explicit authentication actions.
Artificial Intelligence and Machine Learning for Threat Detection
Traditional security systems rely on known threat signatures and rule-based detection. This approach fails against novel attacks and sophisticated adversaries who continuously evolve their tactics. Artificial intelligence and machine learning protocols enable systems to identify previously unknown threats by recognizing anomalous patterns and behaviors.
Machine learning algorithms analyze vast amounts of security data to establish baseline normal behavior patterns. When systems detect deviations from these baselines, they generate alerts for security teams to investigate. This approach identifies insider threats, compromised accounts, and advanced persistent threats that evade signature-based detection.
Natural language processing enhances phishing detection by analyzing email content, sender patterns, and communication anomalies. These systems identify social engineering attempts with accuracy rates exceeding human capabilities. Organizations deploying AI-powered email security report dramatic reductions in successful phishing attacks.
The technology requires careful implementation. Machine learning models must train on representative data sets to avoid bias and false positives. Organizations need skilled personnel to tune algorithms, investigate alerts, and continuously refine detection models. The investment pays dividends through improved threat detection and reduced incident response times.
Implementation Strategies and Best Practices for Advanced Security Protocols
Understanding advanced security protocols provides limited value without proper implementation strategies. Organizations must translate theoretical knowledge into practical security measures that protect digital assets while maintaining operational efficiency. The following best practices guide successful security protocol deployment.
Conducting Comprehensive Security Assessments
Effective security begins with thorough understanding of current vulnerabilities and risks. Security assessments identify gaps between existing controls and necessary protections. Organizations should conduct assessments before implementing new protocols to ensure efforts focus on highest-priority risks.
Assessment methodologies vary based on asset types and threat landscape. Vulnerability scanning identifies technical weaknesses in systems and applications. Penetration testing simulates real-world attacks to evaluate defense effectiveness. Security audits examine policies, procedures, and compliance with regulatory requirements.
The assessment process should inventory all digital assets and classify them by sensitivity and business criticality. This classification drives appropriate security protocol selection. Assets containing personally identifiable information require different protections than public marketing materials. Understanding asset value and risk exposure enables rational security investment decisions.
Regular reassessment is crucial as threats evolve and business operations change. Organizations should schedule comprehensive security assessments annually at minimum, with targeted assessments following major infrastructure changes, security incidents, or new threat emergence. Continuous monitoring supplements periodic assessments by providing real-time visibility into security posture.
Assessment Phase
Identify and catalog all digital assets across the organization. Classify assets by sensitivity and business value. Document current security controls and policies.
- Asset inventory completion
- Risk classification
- Control documentation
- Compliance gap analysis
Planning Phase
Develop comprehensive security roadmap based on assessment findings. Prioritize implementations by risk reduction potential. Allocate budget and resources appropriately.
- Protocol selection
- Implementation timeline
- Resource allocation
- Success metrics definition
Execution Phase
Deploy security protocols using phased approach. Test thoroughly before production rollout. Train users on new security procedures and tools.
- Pilot deployment
- User training programs
- Production migration
- Continuous monitoring
Cryptocurrency and Digital Wallet Security
Cryptocurrency assets require specialized security protocols due to their irreversible nature and high value concentration. Unlike traditional financial systems where transactions can be reversed and accounts recovered, blockchain transactions achieve finality within minutes. Lost private keys result in permanent asset loss with no recovery mechanism.
Hardware wallets provide the strongest protection for cryptocurrency holdings. These dedicated devices store private keys in secure elements that never expose keys to internet-connected computers. Transaction signing occurs within the hardware device, preventing malware on host computers from stealing keys or manipulating transactions.
Organizations managing substantial cryptocurrency assets should implement multi-signature custody arrangements. These configurations require multiple authorized parties to approve transactions, preventing single individuals from unilaterally transferring assets. Threshold signature schemes enable flexible approval policies while maintaining security through key distribution.
Recovery procedures require careful design. Seed phrases that restore wallet access must be stored securely with appropriate redundancy. Best practices include metal seed phrase storage resistant to fire and water damage, geographic distribution of backup copies, and secure custody arrangements that balance accessibility with protection against theft.
Critical Warning: Never store cryptocurrency private keys or seed phrases in digital format on internet-connected devices. Digital storage creates vulnerability to malware, hacking, and unauthorized access. Always use offline storage methods such as hardware wallets or paper backups stored in secure physical locations.
Access Management and Identity Governance
Effective access management ensures that users receive appropriate permissions based on job responsibilities while preventing excessive access that creates security risks. Role-based access control provides the foundation for enterprise access management by defining permissions according to organizational roles rather than individual users.
Privileged access management systems provide additional controls for accounts with elevated permissions. These systems enforce approval workflows for privileged access requests, record all privileged sessions for audit purposes, and automatically rotate privileged credentials to limit exposure windows when credentials become compromised.
Identity governance programs establish processes for access certification, ensuring that users maintain only necessary permissions as responsibilities change. Regular access reviews identify and remediate permission creep where users accumulate excessive rights over time. Automated workflows remove access promptly when employees change roles or leave the organization.
The principle of least privilege should guide all access decisions. Users receive minimum permissions necessary to perform their duties, with temporary elevation available when additional access becomes necessary for specific tasks. This approach limits potential damage from compromised accounts while maintaining operational efficiency.
Incident Response Planning and Execution
Despite best prevention efforts, security incidents occur. Effective incident response minimizes damage through rapid detection, containment, and recovery. Organizations must develop comprehensive incident response plans before incidents occur, as crisis situations prevent clear thinking and coordinated action.
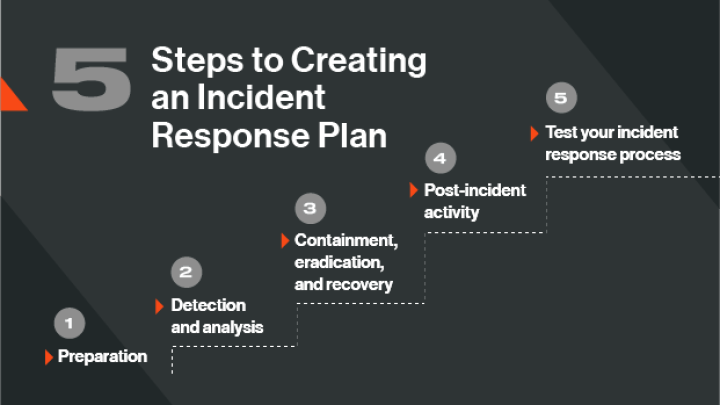
Incident response plans should define clear roles and responsibilities for response team members. Communication protocols ensure appropriate stakeholders receive timely notification without creating information overload. Escalation procedures address situations requiring executive involvement or external assistance from cybersecurity specialists.
Response procedures vary based on incident type. Data breaches require different actions than ransomware attacks or denial-of-service incidents. Plans should include specific playbooks for common scenarios, providing step-by-step guidance that enables rapid response even during high-stress situations.
Regular testing through tabletop exercises and simulated incidents validates response plans and builds team capabilities. These exercises identify gaps in procedures, communication breakdowns, and resource limitations before real incidents occur. Organizations should conduct incident response exercises at least quarterly, varying scenarios to build broad response capabilities.
Protecting Digital Assets Across Cloud, Network, and Data Layers
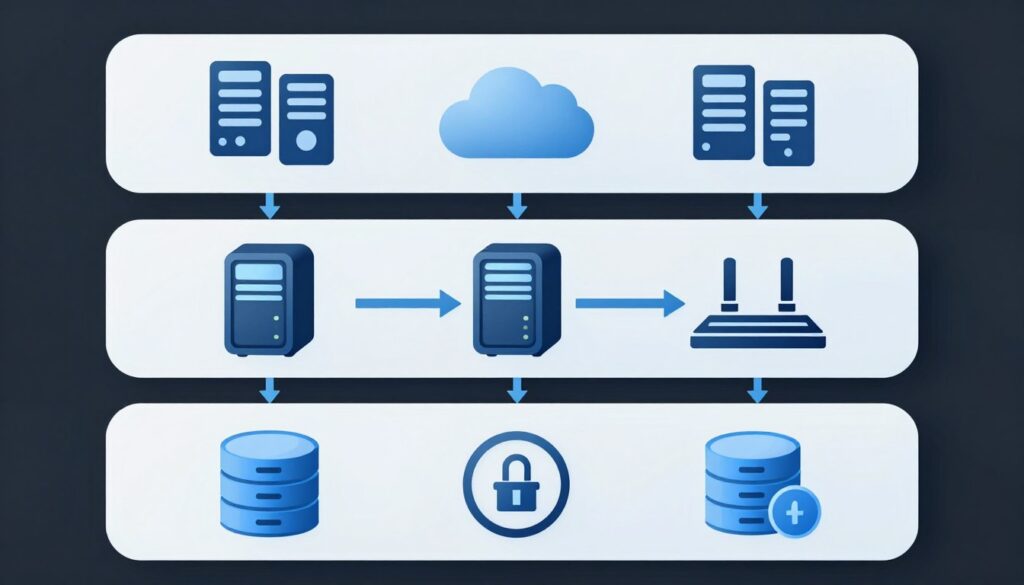
Cloud Security Architecture and Controls
Cloud computing fundamentally changes security requirements and approaches. Traditional perimeter-based security models fail in cloud environments where assets reside outside organizational boundaries. Organizations must implement cloud-specific security protocols that provide protection regardless of infrastructure location.
Cloud security posture management tools continuously assess cloud configurations against security best practices and compliance requirements. These systems identify misconfigurations such as publicly accessible storage buckets, overly permissive access policies, and unencrypted data storage. Automated remediation capabilities correct identified issues before attackers can exploit them.
Identity and access management becomes crucial in cloud environments where traditional network controls provide limited protection. Cloud platforms offer sophisticated identity services that enable fine-grained access controls, conditional access policies based on risk factors, and integration with enterprise identity systems through federation protocols.
Data protection in cloud environments requires encryption both at rest and in transit. Organizations should maintain control of encryption keys rather than relying solely on cloud provider key management. Customer-managed keys ensure that even cloud providers cannot access sensitive data, addressing concerns about government data requests and insider threats.
Network Security Measures and Segmentation
Network security provides critical defense layers that protect digital assets from unauthorized access and lateral movement following initial compromise. Modern network security extends beyond traditional firewalls to include sophisticated threat detection, microsegmentation, and encrypted communications across all network segments.
Next-generation firewalls combine traditional packet filtering with deep packet inspection, intrusion prevention, and application awareness. These systems identify and block malicious traffic based on behavior patterns rather than solely port and protocol information. Integration with threat intelligence feeds enables blocking of traffic from known malicious sources.
Network segmentation isolates critical assets and limits attacker movement following initial breach. Microsegmentation creates fine-grained isolation at individual workload levels, preventing lateral movement even within data centers. Software-defined networking enables dynamic segmentation policies that adapt to changing security requirements without physical infrastructure changes.
Virtual private networks protect data during transmission across untrusted networks. Organizations should implement VPN access for all remote workers accessing corporate resources. Modern VPN solutions include zero-trust network access capabilities that verify device security posture before granting network access, preventing compromised devices from connecting.
Perimeter Security
First line of defense protecting network boundaries from external threats and unauthorized access attempts.
- Next-generation firewalls with intrusion prevention
- DDoS protection and traffic filtering
- Web application firewalls for public services
- Email security gateways blocking threats
Internal Segmentation
Divides network into isolated zones preventing lateral movement and containing security incidents.
- Microsegmentation at workload level
- VLAN separation for departments
- DMZ for public-facing systems
- Air-gapped networks for critical assets
Access Control
Manages and restricts network access based on user identity, device security, and contextual factors.
- Network access control validation
- 802.1X authentication for devices
- VPN for remote access
- Zero-trust network access controls
Monitoring and Detection
Continuous visibility into network activity identifying suspicious patterns and potential threats.
- Network traffic analysis systems
- Intrusion detection and prevention
- Security information event management
- Network behavior anomaly detection
Data Loss Prevention and Information Protection
Data loss prevention systems protect sensitive information from unauthorized disclosure through technical controls that monitor, detect, and block sensitive data in motion, at rest, and in use. These systems prevent both malicious exfiltration and accidental disclosure that could result in breaches, compliance violations, and competitive disadvantage.
Content inspection engines analyze data flows to identify sensitive information based on patterns, keywords, and data classifications. Systems can detect credit card numbers, personally identifiable information, intellectual property markers, and custom-defined sensitive data patterns. Policies automatically block or encrypt transmissions containing sensitive data to unauthorized destinations.
Endpoint data loss prevention extends protection to user devices, monitoring clipboard operations, screen captures, file transfers, and removable media usage. These controls prevent users from accidentally or deliberately copying sensitive data to unauthorized locations. User education combined with technical controls provides the most effective data protection.
Rights management technologies enforce persistent data protection that travels with files regardless of location. Protected documents require authentication to open and restrict operations such as copying, printing, or forwarding. Organizations can revoke access to previously distributed documents, enabling information control even after data leaves organizational boundaries.
Compliance and Regulatory Frameworks for Digital Asset Protection
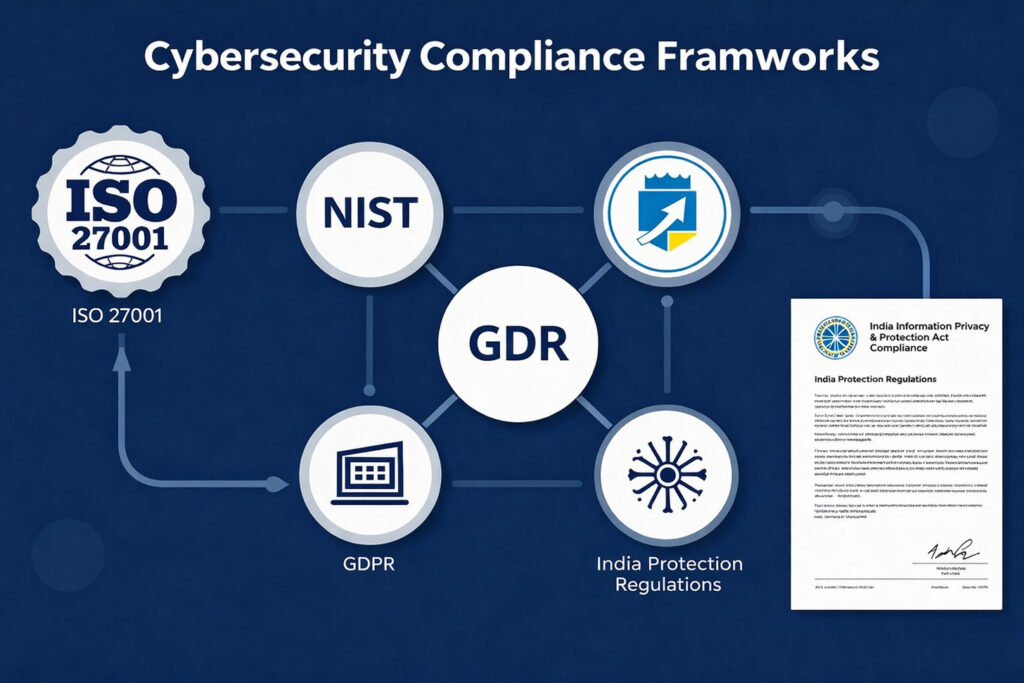
Regulatory compliance drives security protocol implementation for many organizations. Understanding applicable regulations and standards helps prioritize security investments and demonstrate due diligence. Compliance requirements vary by industry, geography, and data types, requiring careful analysis of organizational obligations.
Global and Indian Regulatory Requirements
Indian organizations face increasing regulatory scrutiny regarding data protection and cybersecurity practices. The Information Technology Act establishes baseline security requirements for handling sensitive personal data. Organizations failing to implement reasonable security practices face liability for data breaches and potential compensation obligations to affected individuals.
The Personal Data Protection Bill introduces comprehensive privacy requirements similar to European GDPR regulations. Organizations must implement data protection by design principles, conduct privacy impact assessments, and demonstrate accountability through documented security measures. Cross-border data transfers require adequate protections ensuring continued data security.
Sector-specific regulations impose additional requirements. Reserve Bank of India guidelines mandate specific cybersecurity controls for financial institutions, including board oversight, incident reporting, and third-party risk management. Healthcare organizations must protect patient data under various regulations establishing security and confidentiality requirements.
Global businesses operating in India must navigate multiple regulatory frameworks simultaneously. GDPR applies to organizations processing European resident data regardless of business location. Organizations must implement controls satisfying the most stringent applicable requirements while maintaining operational efficiency across regulatory jurisdictions.
Security Frameworks and Standards
Security frameworks provide structured approaches to implementing comprehensive security programs. These frameworks offer tested methodologies that guide organizations through identifying risks, selecting controls, and measuring security effectiveness. Adoption demonstrates commitment to security best practices and facilitates compliance with multiple regulatory requirements.
ISO 27001 represents the international standard for information security management systems. This framework establishes requirements for systematic management of information security risks through appropriate controls selection and implementation. Organizations achieving ISO 27001 certification demonstrate mature security programs to customers and regulators.
NIST Cybersecurity Framework provides flexible guidance suitable for organizations of all sizes. The framework organizes security activities into five core functions: identify, protect, detect, respond, and recover. Organizations use the framework to assess current capabilities, identify gaps, and prioritize improvements aligned with business risk tolerance.
Industry-specific standards address unique security requirements for particular sectors. Payment Card Industry Data Security Standard mandates controls for organizations handling payment card data. Healthcare organizations reference HIPAA Security Rule requirements. Financial services firms implement controls specified in various banking and securities regulations.
| Framework | Focus Area | Best Suited For | Certification Available |
| ISO 27001 | Information security management systems and risk-based controls | Organizations seeking international certification and comprehensive security programs | Yes |
| NIST Cybersecurity Framework | Five core security functions and flexible implementation guidance | Organizations of all sizes needing adaptable security framework | No |
| CIS Controls | Prioritized implementation of essential security safeguards | Organizations seeking practical, prioritized security improvements | No |
| PCI DSS | Payment card data security requirements and validation | Organizations processing, storing, or transmitting payment card information | Compliance validation |
| SOC 2 | Service organization controls for security, availability, and confidentiality | Technology service providers demonstrating security to customers | Audit report |
Audit Readiness and Documentation
Regulatory compliance requires comprehensive documentation demonstrating security control implementation and effectiveness. Organizations must maintain evidence of security policies, procedures, risk assessments, and control testing results. Audit readiness ensures organizations can efficiently respond to regulatory examinations and customer security inquiries.
Security policies establish organizational requirements and expectations regarding information protection. Policies should address all aspects of security program including access control, encryption, incident response, and vendor management. Regular policy reviews ensure continued relevance as threats and business operations evolve.
Procedure documentation provides detailed instructions for implementing policy requirements. Procedures guide staff through specific security tasks such as granting access, responding to incidents, or performing security assessments. Clear procedures enable consistent security control implementation across the organization.
Control testing validates that implemented security measures operate effectively. Organizations should conduct regular security assessments including vulnerability scans, penetration tests, and control audits. Documentation of testing results and remediation activities demonstrates ongoing security program effectiveness to auditors and regulators.
Human Factors: Employee Training and Security Awareness

Technology controls provide essential protection for digital assets, but human behavior ultimately determines security effectiveness. Employees represent both the greatest security vulnerability and most powerful defense asset. Comprehensive security awareness training transforms users from security liability into security champions who actively protect organizational assets.
Security Awareness Training Programs
Effective security training extends beyond annual compliance courses that employees click through without retention. Modern training programs use engaging content, realistic scenarios, and continuous reinforcement to build lasting security awareness. Training should cover specific threats relevant to organizational operations and user roles.
Phishing remains the most common attack vector targeting organizations. Training programs must educate users on identifying suspicious emails, verifying sender authenticity, and reporting potential phishing attempts. Simulated phishing campaigns provide practical experience identifying threats while measuring program effectiveness and identifying users requiring additional training.
Social engineering awareness prepares employees for manipulation attempts that exploit human psychology rather than technical vulnerabilities. Training should cover phone-based attacks, pretexting scenarios, and physical security breaches. Real-world examples help users understand how attackers leverage authority, urgency, and trust to bypass security controls.
Role-based training addresses specific security responsibilities for different user populations. Developers require secure coding training. System administrators need privileged access security guidance. Executives face targeted threats requiring specialized awareness. Tailored training ensures all users receive relevant security knowledge for their responsibilities.
Building Security-Conscious Culture
Security awareness training provides necessary knowledge, but organizational culture determines whether users apply that knowledge in daily activities. Security-conscious cultures treat information protection as shared responsibility rather than solely IT department obligation. Leadership commitment and consistent reinforcement establish security as core organizational value.
Recognition programs reward security-positive behaviors and encourage continued vigilance. Organizations should celebrate employees who identify and report security threats, implement creative security improvements, or complete advanced security training. Public recognition creates positive associations with security activities and motivates broader participation.
Transparent communication about security incidents, provided it doesn’t compromise sensitive details, builds trust and reinforces training lessons. Sharing how specific attacks occurred and what indicators users could have recognized transforms abstract threats into concrete learning opportunities. Post-incident communications should focus on improvement rather than blame.
Security champions embedded within business units extend security team reach and provide local expertise. These designated individuals receive advanced training and serve as first contacts for security questions. Champion programs distribute security knowledge throughout organizations while building collaborative relationships between security and business functions.
Future-Proofing Security: Emerging Threats and Next-Generation Protocols

The cybersecurity landscape continues evolving at accelerating pace. Understanding emerging threats and next-generation security protocols enables organizations to prepare for future challenges rather than perpetually reacting to new attack methods. Proactive security investment provides competitive advantage and resilience against sophisticated adversaries.
Artificial Intelligence in Cyber Attacks
Attackers increasingly leverage artificial intelligence to enhance attack effectiveness and scale. AI-powered attacks can adapt to defensive measures, identify vulnerabilities more efficiently, and generate convincing social engineering content. Defenders must understand these threats and deploy AI-powered defensive capabilities to maintain security effectiveness.
Deepfake technology creates realistic audio and video impersonating real individuals. Attackers use deepfakes for social engineering, business email compromise, and disinformation campaigns. Organizations must implement verification procedures for high-risk requests and educate employees about deepfake threats.
Automated vulnerability discovery tools powered by machine learning identify security weaknesses faster than human researchers. While security teams use these tools for defense, attackers leverage similar capabilities to find and exploit vulnerabilities before patches become available. Rapid patch deployment becomes increasingly critical as attack windows compress.
AI-generated phishing attacks create personalized messages more convincing than traditional mass phishing campaigns. These attacks analyze public information about targets to craft contextually relevant messages that bypass traditional detection methods. Behavioral analysis and anomaly detection provide better defense against AI-enhanced social engineering.
Third-Party Risk Management and Vendor Security
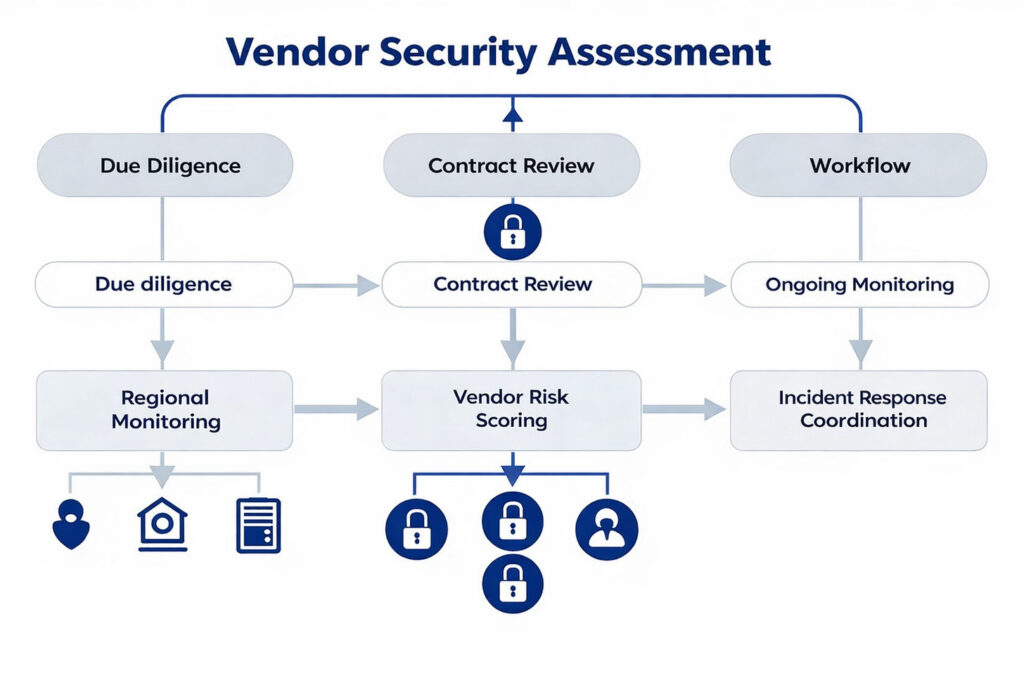
Organizations increasingly rely on third-party vendors, cloud service providers, and business partners to deliver services and process data. This interconnected ecosystem creates security dependencies where vendor vulnerabilities directly impact organizational security. Comprehensive third-party risk management programs protect digital assets from supply chain attacks and vendor-related breaches.
Vendor Security Assessment Processes
Vendor security assessment begins before contract execution during the procurement process. Organizations should evaluate vendor security capabilities, certifications, and track records before entrusting them with access to systems or sensitive data. Assessment rigor should match vendor risk level based on data sensitivity and access privileges.
Security questionnaires gather information about vendor security practices including access controls, encryption, incident response, and compliance certifications. Standardized questionnaires enable efficient assessment while ensuring consistent evaluation criteria across vendors. Organizations should verify questionnaire responses through documentation review and testing rather than accepting self-assessments uncritically.
Third-party audits and certifications provide independent validation of vendor security controls. SOC 2 reports assess service organization controls for security, availability, and confidentiality. ISO 27001 certification demonstrates implementation of information security management systems. Organizations should review audit reports carefully, focusing on identified deficiencies and remediation plans.
Contractual security requirements establish vendor obligations regarding data protection, security controls, incident notification, and audit rights. Contracts should specify security standards vendors must maintain, breach notification timelines, and liability for security failures. Clear contractual terms provide enforcement mechanisms when vendors fail to meet security obligations.
Continuous Vendor Monitoring
Initial vendor assessment provides snapshot of security posture at specific point in time. Vendor security capabilities change over time due to business growth, personnel turnover, or financial stress. Continuous monitoring identifies security degradation before it results in incidents affecting organizational assets.
Vendor risk management platforms automate ongoing monitoring through news monitoring, financial health tracking, and security rating services. These systems alert organizations to vendor bankruptcies, data breaches, regulatory actions, or other events indicating increased risk. Automated monitoring enables efficient oversight of large vendor populations.
Regular reassessments verify continued vendor security compliance. Organizations should reassess critical vendors annually at minimum, with more frequent reviews for highest-risk relationships. Reassessment schedules should consider vendor criticality, data sensitivity, and previous assessment results.
Vendor security incidents require coordinated response between organizations and vendors. Contracts should establish clear incident communication protocols, evidence preservation requirements, and remediation expectations. Organizations must maintain incident response capabilities that address vendor-originated security events affecting internal assets.
Security Program Maturity and Continuous Improvement
A mature security program exhibits:
Clear governance and ownership
Defined security policies and standards
Effective risk management and compliance controls
Regular security awareness and training
Incident detection, response, and recovery capabilities
Metrics and continuous measurement of security outcomes
Effective security programs require continuous improvement rather than one-time implementation. Organizations must measure security effectiveness, identify improvement opportunities, and systematically enhance capabilities over time. Maturity models provide frameworks for assessing current state and planning progression toward advanced security capabilities.
Regular Security Assessments and Updates
Continuous improvement requires regular assessment of security effectiveness and identification of enhancement opportunities. Organizations should establish cadences for different assessment types balancing thoroughness with resource efficiency. Assessment findings drive improvement initiatives and security roadmap updates.
Annual comprehensive security program reviews evaluate all aspects of security including governance, risk management, technical controls, and operational processes. These strategic assessments identify major gaps requiring multi-year initiatives and validate overall program direction alignment with business strategy.
Quarterly control testing validates specific security control effectiveness through technical testing and process reviews. Focused assessments provide regular feedback on control performance without requiring comprehensive program evaluation. Results inform tactical improvements and resource allocation decisions.
Continuous vulnerability management identifies and remediates technical weaknesses through automated scanning, manual testing, and threat intelligence integration. Organizations should implement continuous assessment capabilities that provide real-time visibility into security posture rather than periodic snapshots.
Implementing Advanced Security Protocols: Your Action Plan
Safeguarding digital assets through advanced security protocols represents ongoing commitment rather than one-time project. The threat landscape continues evolving, requiring organizations to maintain vigilance, adapt defenses, and continuously enhance security capabilities. Success requires strategic planning, sustained investment, and organizational commitment from leadership through frontline staff.
Begin with comprehensive assessment of current security posture and digital asset inventory. Understanding what requires protection and existing vulnerabilities enables rational prioritization of security investments. Assessment findings should drive development of multi-year security roadmap aligned with business objectives and risk tolerance.
Implement foundational security protocols first before pursuing advanced capabilities. Multi-factor authentication, encryption, and basic access controls provide essential protection that enables safe adoption of advanced technologies. Organizations attempting to implement sophisticated protocols without foundational controls often create security gaps despite advanced capabilities in specific areas.
Security effectiveness depends on people as much as technology. Invest in comprehensive training programs that build security awareness throughout organizations. Foster security-conscious culture where all employees understand their role in protecting digital assets and feel empowered to question suspicious activities.
Regular reassessment ensures security programs keep pace with evolving threats and business changes. Establish rhythms for security reviews, control testing, and program updates. Monitor emerging threats and evaluate new security protocols for applicability to organizational needs.
Partner with experienced security professionals who can provide expertise, implement advanced protocols, and augment internal capabilities. External specialists offer perspective from working across multiple organizations and industries while providing access to advanced tools and methodologies.
“The question is no longer whether your organization will face cyber threats, but when and how effectively you will respond. Advanced security protocols provide the foundation for resilience in an increasingly hostile digital environment. Organizations that invest proactively in comprehensive protection gain competitive advantage through operational continuity, customer trust, and regulatory compliance.”
Key Takeaways for Digital Asset Protection
The journey toward comprehensive digital asset protection begins with single step. Whether conducting initial security assessment, implementing first advanced protocol, or optimizing mature security program, continuous progress toward improved protection pays dividends through reduced risk, enhanced resilience, and competitive advantage in digital economy.
Start Small, Think Big: Every security journey begins with an initial step—whether it’s a simple assessment or deploying a key control.
Continuous Improvement is Crucial: Digital threats evolve rapidly; ongoing optimization of security protocols ensures sustained protection.
Layered Defense Reduces Risk: Combining people, processes, and technology creates resilient barriers against cyber threats.
Asset Prioritization Matters: Identify and protect your most valuable digital assets based on their sensitivity and business impact.
Compliance Supports Trust: Meeting regulatory requirements not only avoids penalties but builds customer and partner confidence.
Resilience Enables Recovery: Beyond prevention, prepare for incidents with robust response and recovery plans.
Security Drives Competitive Advantage: Strong digital asset protection strengthens brand reputation and supports growth in the digital economy.
Organizations that treat security as strategic investment rather than cost center position themselves for success in increasingly digital and threat-filled business environment. The time to act is now, before the next breach, before regulatory penalties, before customer trust erodes. Protect your digital assets today to secure your business tomorrow.
At Atrity Info Solutions, protecting digital assets isn’t just a technical requirement—it’s a strategic priority that drives long-term business success. In today’s interconnected digital landscape, organizations must move beyond reactive security measures and adopt a proactive, structured approach to risk management and compliance.
Whether clients are initiating their cybersecurity journey or enhancing a mature security program, Atrity Info Solutions delivers tailored, scalable solutions that support consistent and measurable progress. By integrating security into organizational culture, governance frameworks, and operational processes, we help businesses reduce risk exposure, safeguard sensitive information, and strengthen overall resilience.
Through continuous improvement, regulatory alignment, vendor risk management, and comprehensive cybersecurity frameworks, Atrity transforms security from a cost center into a strategic enabler of innovation, trust, and competitive advantage. In the evolving digital economy, Atrity Info Solutions empowers organizations to protect what matters most—while confidently embracing growth and digital transformation.
 Read More
Read More