What Is Wazuh and Why Security Teams Choose It
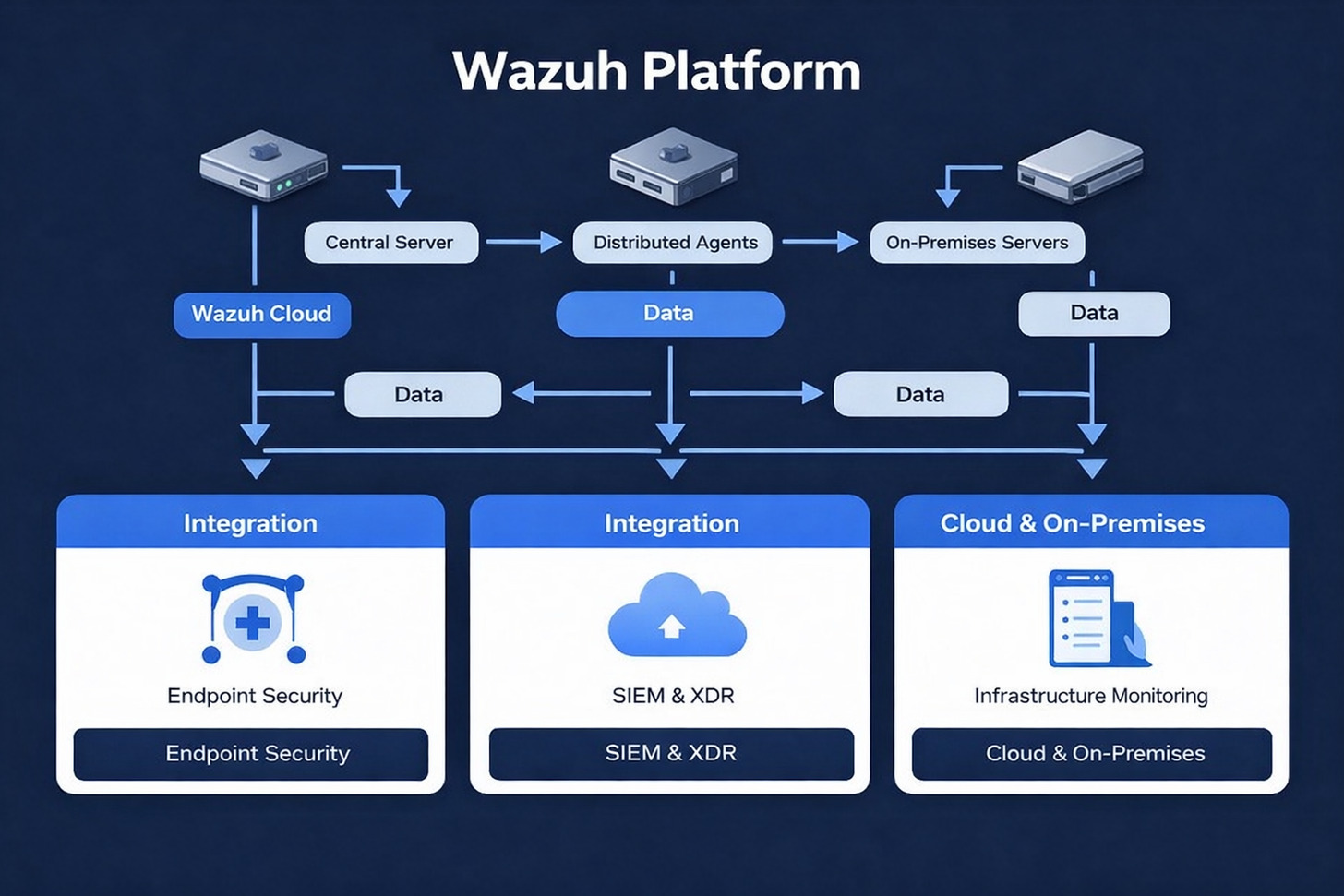
Wazuh represents a unified security platform that consolidates SIEM and XDR capabilities into a single open source solution. The platform monitors endpoints, analyzes security data from multiple sources, and responds to threats automatically. Organizations deploy Wazuh across Linux, Windows, macOS, and containerized environments to achieve comprehensive visibility.
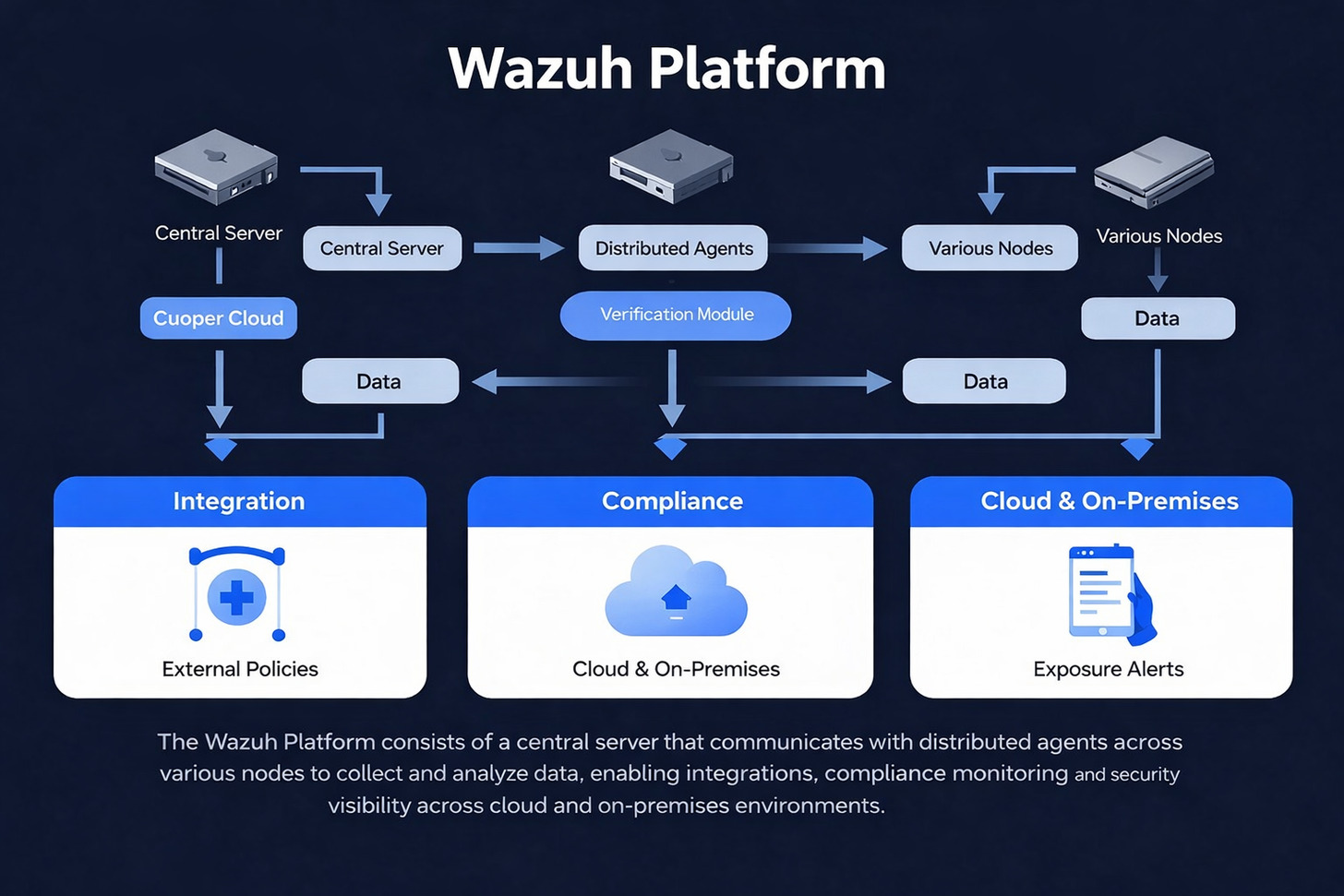
The platform architecture consists of three primary components working in harmony. Wazuh agents installed on monitored endpoints collect security data and execute response actions. The central Wazuh server processes collected data, applies detection rules, and generates security alerts. The web interface provides analysts with intuitive dashboards for investigation and response activities.
Security professionals appreciate Wazuh for its transparency and flexibility. The open source model allows teams to inspect every line of code, customize detection logic, and extend functionality to meet specific requirements. Organizations maintain complete control over their security infrastructure without vendor lock-in or licensing restrictions.
Core Platform Capabilities
- Real-time threat detection across all endpoints
- Comprehensive log data collection and analysis
- File integrity monitoring for critical systems
- Vulnerability detection and assessment
- Automated incident response actions
- Regulatory compliance monitoring and reporting
Deployment Flexibility
- On-premises server deployment option
- Cloud-native architecture for scalability
- Hybrid environment support across infrastructure
- Container and Kubernetes integration
- Multi-tenant configuration for service providers
- High availability cluster deployment
The platform integrates seamlessly with existing security tools and data sources. Wazuh connects to threat intelligence feeds, OSINT sources, and vulnerability databases to enrich detection capabilities. Security teams consolidate alerts from firewalls, intrusion detection systems, and cloud services into a unified view.
Advanced Threat Detection and Intelligence Integration
Wazuh employs multiple detection techniques to identify security threats across monitored infrastructure. The platform analyzes log data from diverse sources, correlates events to detect attack patterns, and applies behavioral analytics to spot anomalous activity. This multi-layered approach catches threats that single-method detection systems miss.
Threat intelligence integration enhances detection accuracy by providing context about emerging threats. Wazuh connects to multiple threat intelligence sources including commercial feeds and open source databases. The system automatically enriches security alerts with intelligence data, helping analysts understand threat actor tactics and prioritize response efforts.
Detection Methodologies and Techniques
The platform implements signature-based detection through an extensive rule set covering common attack patterns. Security researchers continuously update these rules to address new threats and vulnerabilities. Organizations customize detection rules to match their specific environment and risk profile.
Behavioral analysis capabilities identify suspicious activities that don’t match known attack signatures. The system establishes baseline behavior for users and systems, then flags deviations that may indicate compromise. This approach detects zero-day exploits and advanced persistent threats that evade signature-based detection.
Log Analysis and Correlation
Wazuh processes millions of log entries per second, applying correlation rules to identify attack sequences. The system recognizes patterns across multiple systems that indicate coordinated attacks or lateral movement.
Anomaly Detection Methods
Machine learning algorithms establish normal behavior patterns for monitored systems. Deviations trigger alerts for investigation, catching insider threats and compromised accounts exhibiting unusual behavior.
Threat Intelligence Enrichment
Integration with OSINT feeds and commercial threat data adds context to security alerts. Analysts instantly see if detected indicators match known threat campaigns or malicious infrastructure.
Intrusion Detection and Prevention
Wazuh provides comprehensive intrusion detection capabilities across network and host layers. The wazuh agent monitors system calls, file access patterns, and network connections to detect intrusion attempts. Integration with network intrusion detection systems provides additional visibility into network-level attacks.
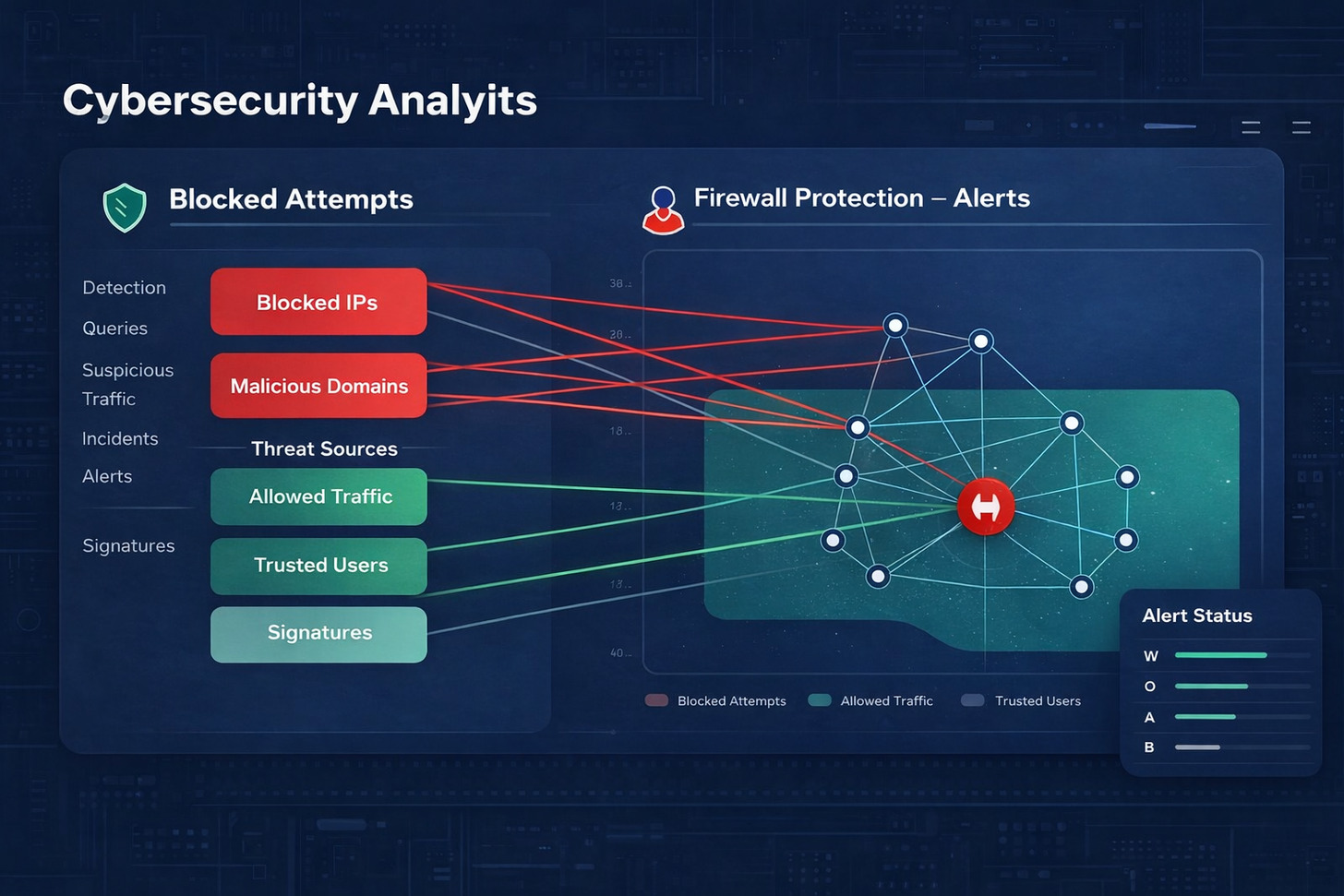
Active response mechanisms allow Wazuh to automatically block detected threats. The platform can isolate compromised systems, block malicious IP addresses at the firewall, and terminate suspicious processes. Security teams configure response actions based on alert severity and organizational policies.
File Integrity Monitoring
Track changes to critical system files and configuration in real time. Detect unauthorized modifications that may indicate system compromise or insider threats.
- Real-time change detection alerts
- Detailed change tracking with who, what, when data
- Compliance reporting for audit requirements
- Configurable monitoring scope per system
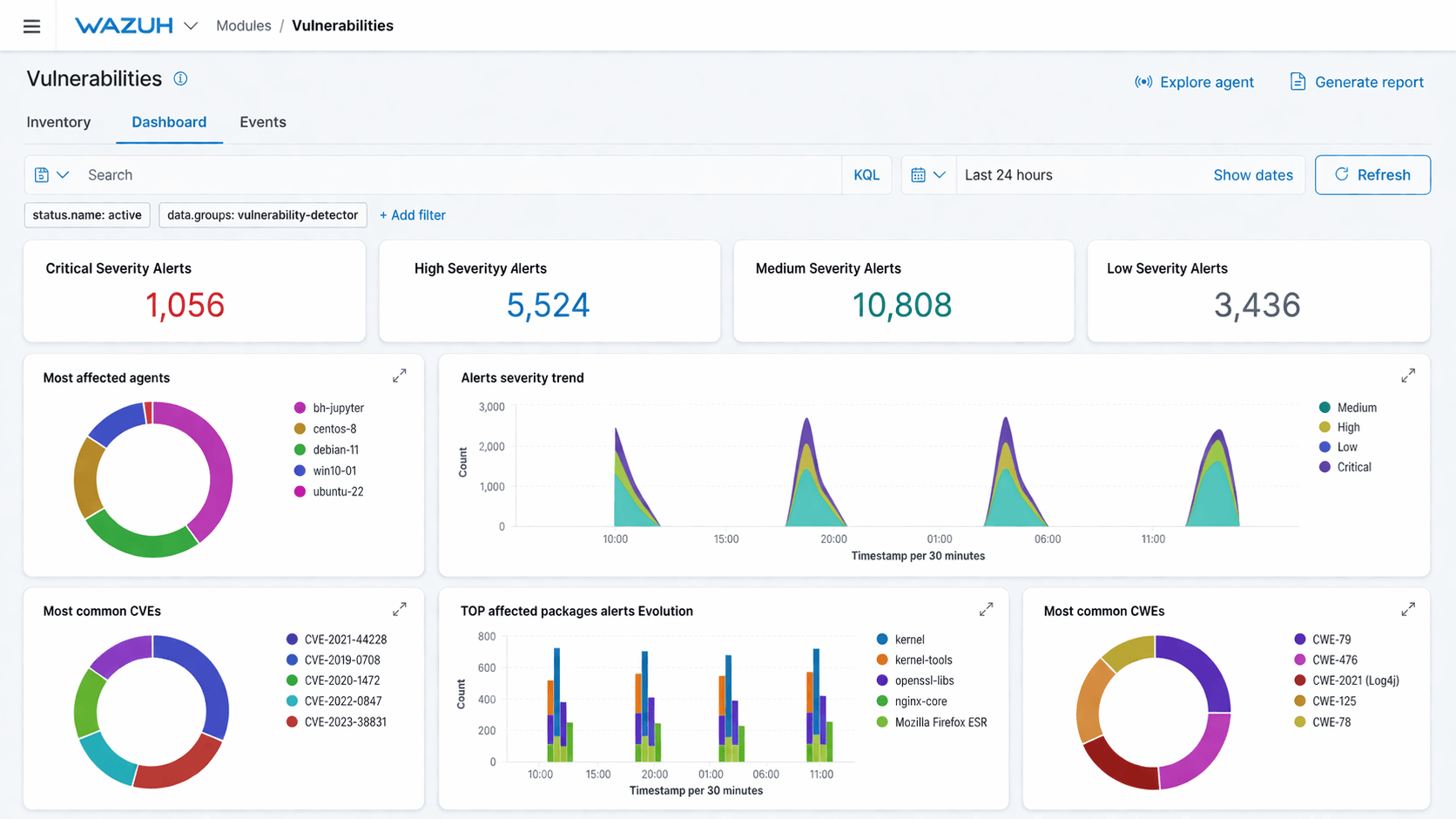
Vulnerability Detection
Continuously scan endpoints for known vulnerabilities and security weaknesses. Prioritize patching efforts based on exploitability and business impact.
- Automated vulnerability scanning schedule
- CVE database integration for up-to-date intel
- Risk scoring and prioritization logic
- Patch management workflow integration
Configuration Assessment
Audit system configurations against security benchmarks and compliance standards. Identify misconfigurations that create security vulnerabilities.
- CIS benchmark compliance checks
- Custom policy configuration support
- Automated remediation recommendations
- Configuration drift detection alerts
Regulatory Compliance and Security Standards
Organizations face increasing regulatory compliance requirements across industries and geographies. Wazuh simplifies compliance management through automated monitoring, evidence collection, and reporting capabilities. The platform supports major regulatory frameworks including PCI DSS, GDPR, HIPAA, and NIST standards.
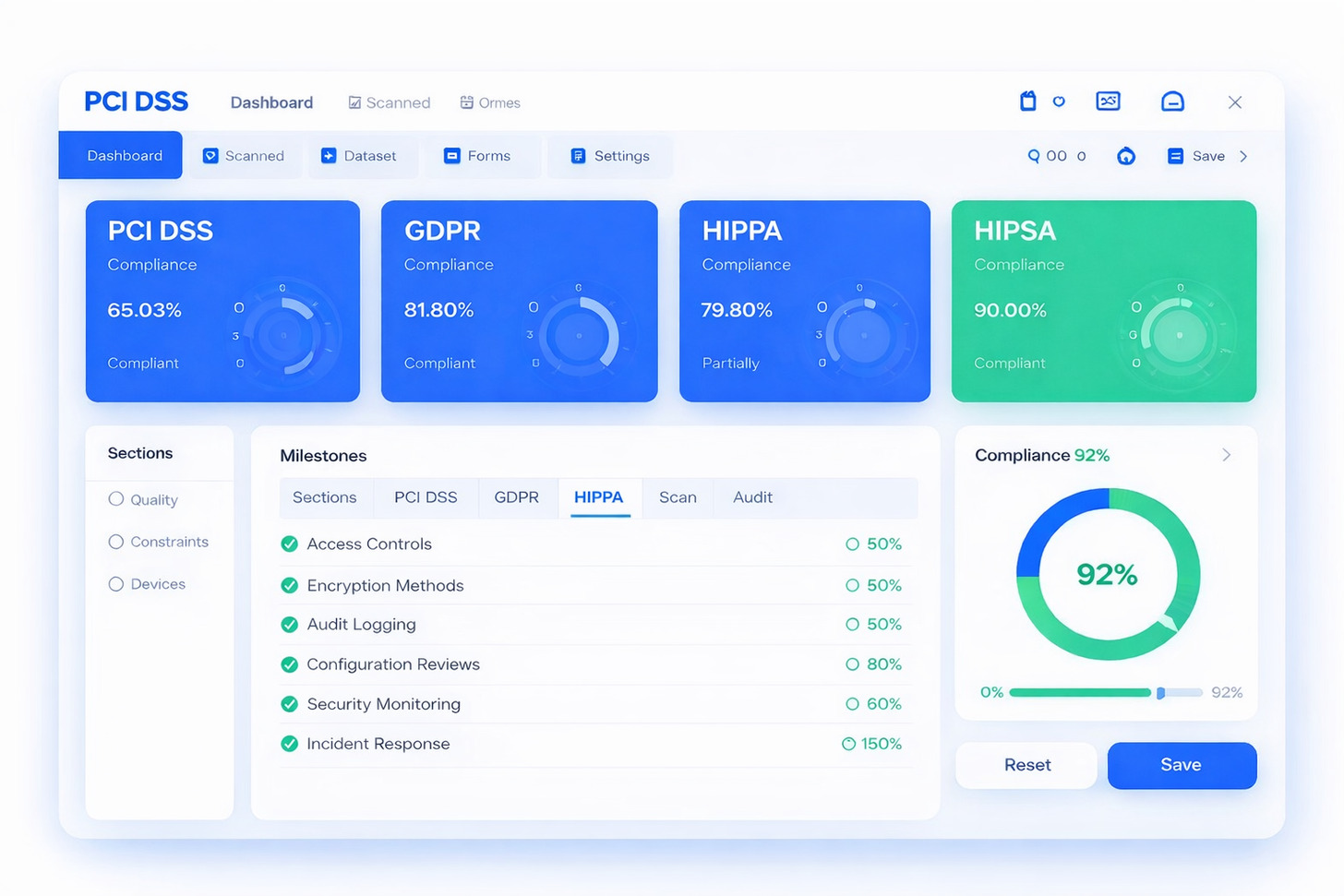
Compliance reporting features generate audit-ready documentation automatically. Security teams access detailed reports showing compliance status across monitored systems. Reports include evidence of control implementation, detected violations, and remediation tracking. This automation reduces audit preparation time significantly.
Supported Compliance Frameworks
The platform includes pre-configured rule sets for common compliance requirements. These rules monitor specific security controls mandated by each framework. Organizations customize rule sets to address their specific compliance scope and interpretation.
Continuous compliance monitoring identifies violations immediately rather than during periodic audits. Wazuh generates alerts when systems drift from compliant configurations or when security events violate policy requirements. This real-time visibility enables rapid remediation before compliance issues escalate.
Audit Trail and Evidence Collection
Comprehensive logging capabilities create detailed audit trails for all security-relevant activities. The platform captures user actions, system changes, access attempts, and security events with timestamps and attribution. This data provides the evidence auditors require to verify control effectiveness.
Log retention policies ensure compliance with regulatory requirements for data preservation. Organizations configure retention periods based on specific regulatory mandates. Wazuh archives historical data securely while maintaining quick access for audit requests and forensic investigations.
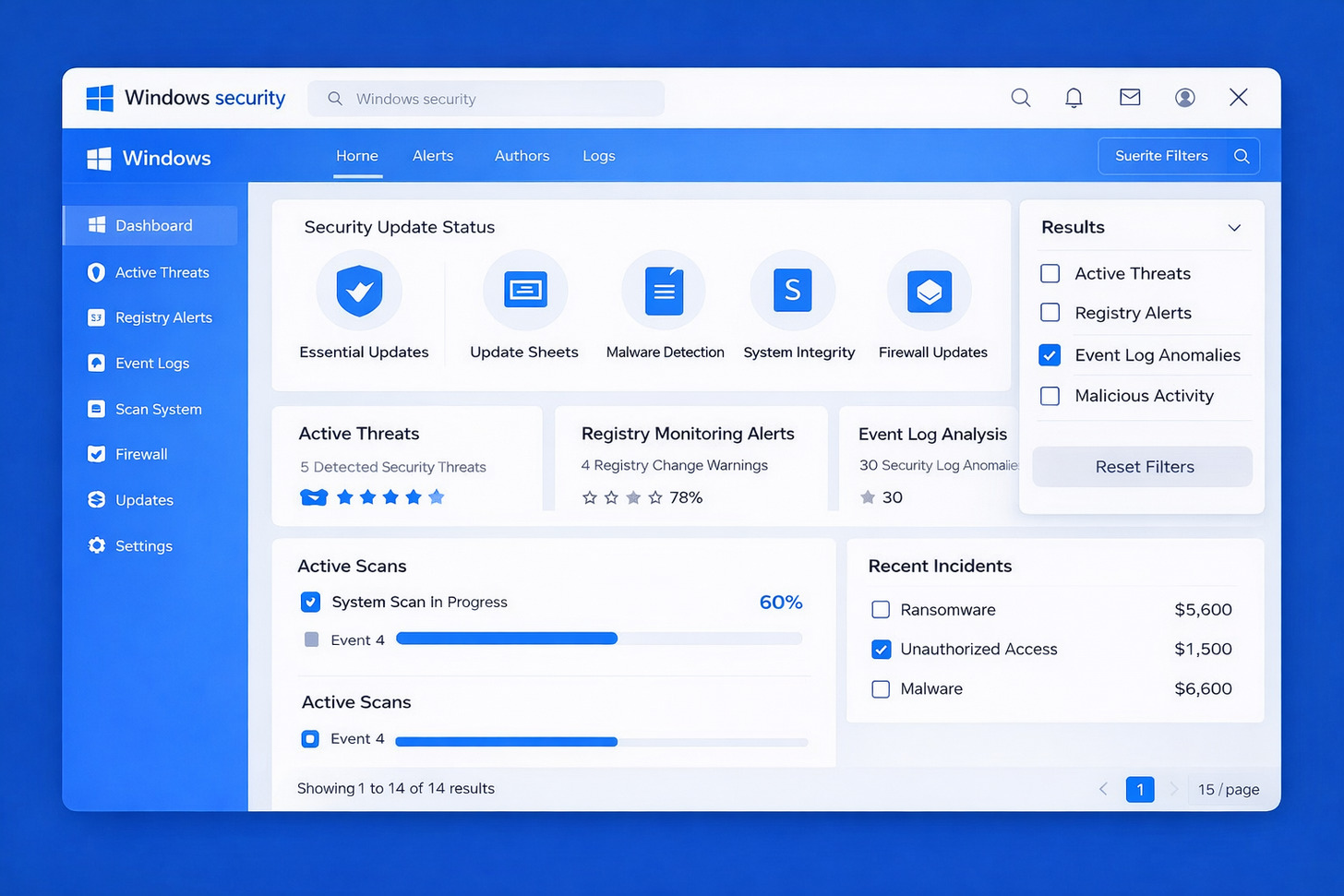
Comprehensive Endpoint Security and Monitoring
Endpoints represent the primary attack surface for modern organizations. Wazuh provides deep visibility into endpoint security through lightweight agents deployed across diverse operating systems. The wazuh agent collects security data, enforces policies, and executes response actions without impacting system performance.

Agent deployment scales from small environments to enterprise infrastructure with thousands of endpoints. Organizations manage agent configuration centrally, pushing policy updates and detection rules to all monitored systems simultaneously. This centralized management reduces operational overhead while maintaining consistent security postures.
Cross-Platform Endpoint Protection
The Wazuh agent supports all major operating systems including Windows, Linux distributions, macOS, Solaris, and AIX. Container environments running Docker and Kubernetes receive the same comprehensive monitoring as traditional servers. This universal coverage eliminates blind spots in heterogeneous environments.
Windows Endpoint Capabilities
Wazuh provides specialized monitoring for Windows environments. The agent integrates with Windows event logs, monitors registry changes, and tracks application installations. PowerShell execution monitoring detects fileless malware and living-off-the-land attacks.
Integration with Windows Defender and other native security tools provides unified visibility. Security teams see endpoint protection status, malware detections, and security updates across all Windows systems from a single interface.
Cloud and Container Security
Cloud environments introduce unique security challenges that Wazuh addresses through specialized integrations. The platform monitors cloud infrastructure changes, analyzes cloud service logs, and detects misconfigurations across AWS, Azure, and Google Cloud Platform.
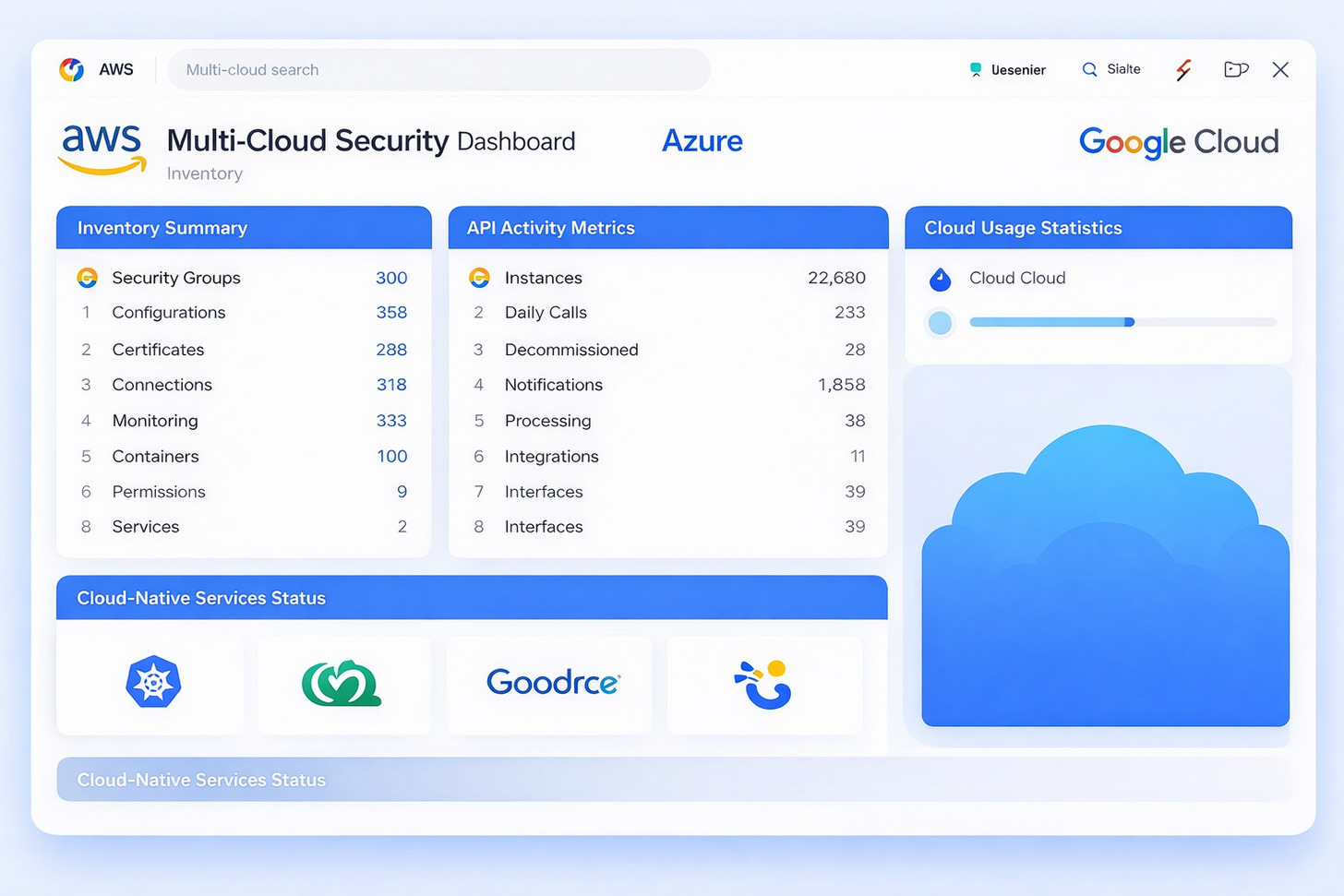
Container security features monitor containerized applications throughout their lifecycle. Wazuh detects vulnerabilities in container images, monitors runtime behavior for anomalies, and enforces security policies in orchestrated environments. Integration with Kubernetes provides visibility into cluster security and workload protection.
AWS Security Monitoring
- CloudTrail log analysis for API activity
- S3 bucket configuration monitoring
- IAM policy change detection
- EC2 instance security assessment
- VPC network security monitoring
Azure Security Integration
- Azure Active Directory monitoring
- Resource group change tracking
- Storage account security checks
- Virtual machine vulnerability scanning
- Network security group auditing
Container Protection
- Docker runtime security monitoring
- Kubernetes cluster auditing
- Container image vulnerability scanning
- Orchestration platform integration
- Service mesh security visibility
Automated Incident Response and Security Orchestration
Speed matters in incident response. Wazuh reduces response time through automated actions triggered by security alerts. The platform executes predefined responses ranging from simple notifications to complex remediation workflows. Security teams focus on strategic decisions while automation handles routine response tasks.
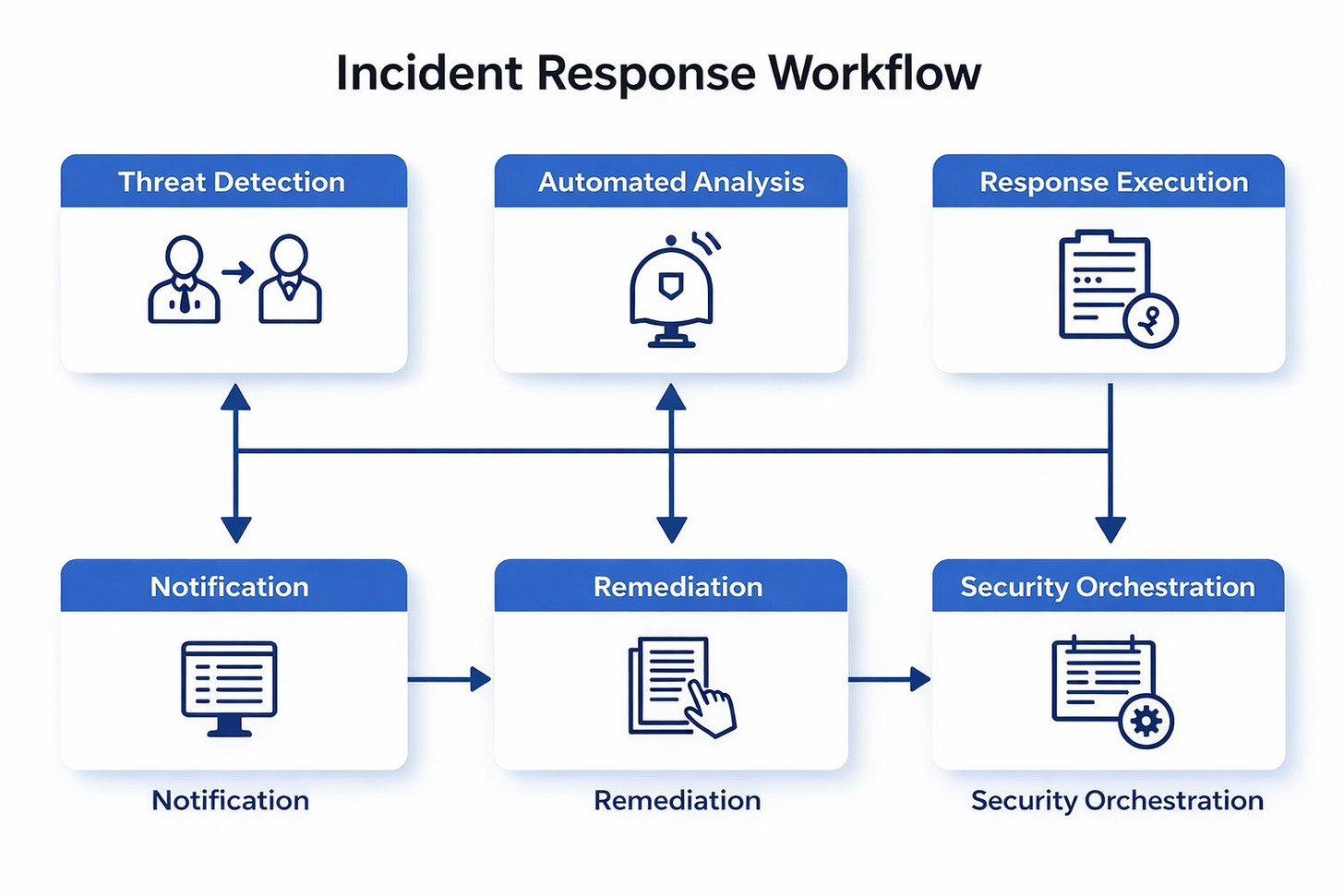
Active response capabilities allow Wazuh to interact directly with monitored systems. The platform blocks malicious IP addresses at firewall level, terminates suspicious processes, and isolates compromised endpoints from the network. These automated actions contain threats before they spread across infrastructure.
Response Action Configuration
Organizations customize response actions based on alert severity and business requirements. High-severity threats trigger immediate blocking actions while lower-priority alerts generate notifications for analyst review. This flexible configuration balances security automation with operational continuity.
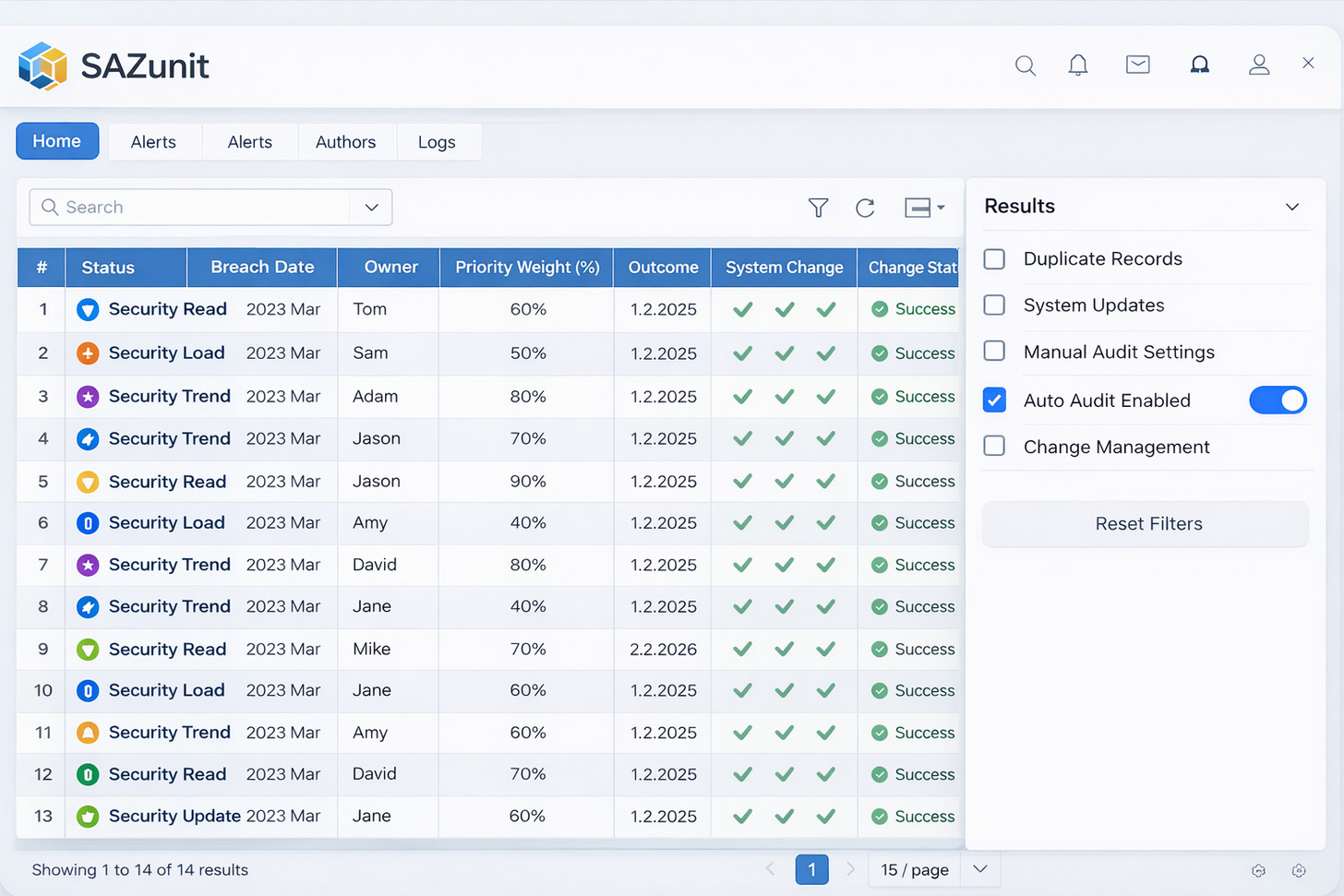
| Response Action | Trigger Conditions | Execution Scope | Business Impact |
| Firewall IP Block | Multiple failed authentication attempts detected | Network perimeter and host firewalls | Low – blocks malicious traffic only |
| Process Termination | Malware process execution identified | Affected endpoint only | Medium – may interrupt user activity |
| Account Lockout | Suspicious account activity detected | Authentication systems | Medium – requires user support intervention |
| System Isolation | Active malware infection confirmed | Compromised system network access | High – system becomes unavailable |
| Alert Notification | Any security event requiring review | Security team communication channels | None – informational only |
Integration with Security Tools
Wazuh integrates with external security tools to extend automation capabilities. The platform sends alerts to SOAR platforms, ticketing systems, and communication tools. These integrations connect Wazuh with existing security workflows and operational processes.
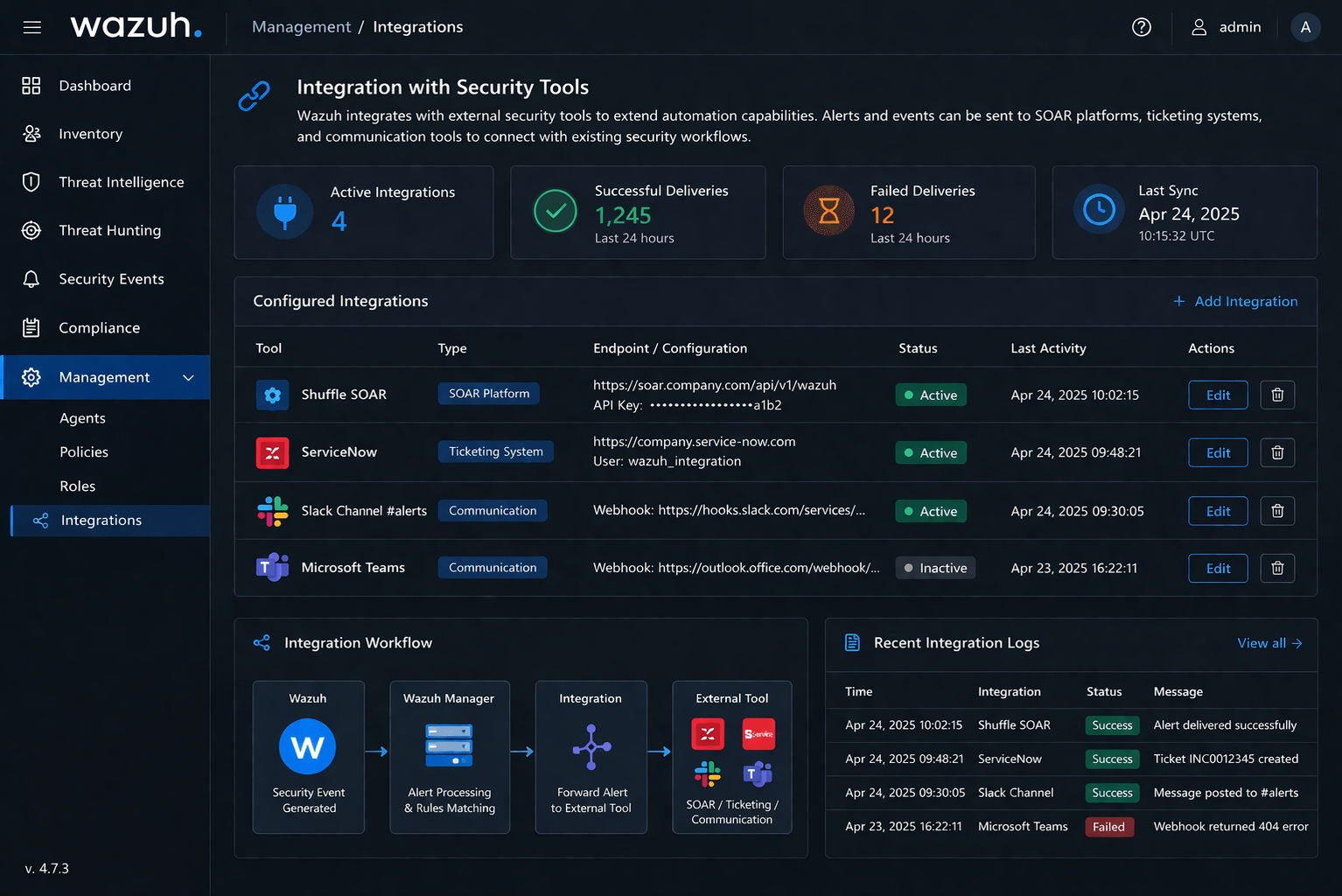
API capabilities enable custom integrations with proprietary tools and internal systems. Organizations develop automated workflows that span multiple security products. Data from Wazuh enriches security operations while actions from other tools feed back into Wazuh for correlation.
Communication Integration
Connect Wazuh alerts to team collaboration platforms for immediate awareness. Security teams receive real-time notifications through their preferred channels.
- Slack channel alert posting
- Microsoft Teams notifications
- PagerDuty incident creation
- Email alert distribution
Ticketing System Integration
Automatically create tickets for security incidents requiring investigation. Maintain audit trail of response activities within existing workflows.
- Jira ticket generation
- ServiceNow incident creation
- Custom ticketing API integration
- Bidirectional status updates
SOAR Platform Connection
Feed Wazuh alerts into security orchestration platforms for complex automated workflows. Combine Wazuh data with other security telemetry sources.
- Shuffle workflow integration
- Splunk SOAR connection
- TheHive case management
- Custom playbook execution
Threat Intelligence Platforms
Enrich Wazuh detections with threat intelligence context. Share indicators of compromise back to intelligence platforms for community benefit.
- MISP threat sharing integration
- Commercial intel feed consumption
- VirusTotal API queries
- Custom intel source integration
Centralized Log Management and Security Analytics
Log data contains critical security information buried within massive volumes of routine events. Wazuh provides centralized log collection, normalization, and analysis across entire infrastructure. The platform processes millions of events per second, extracting security insights from log data sources.
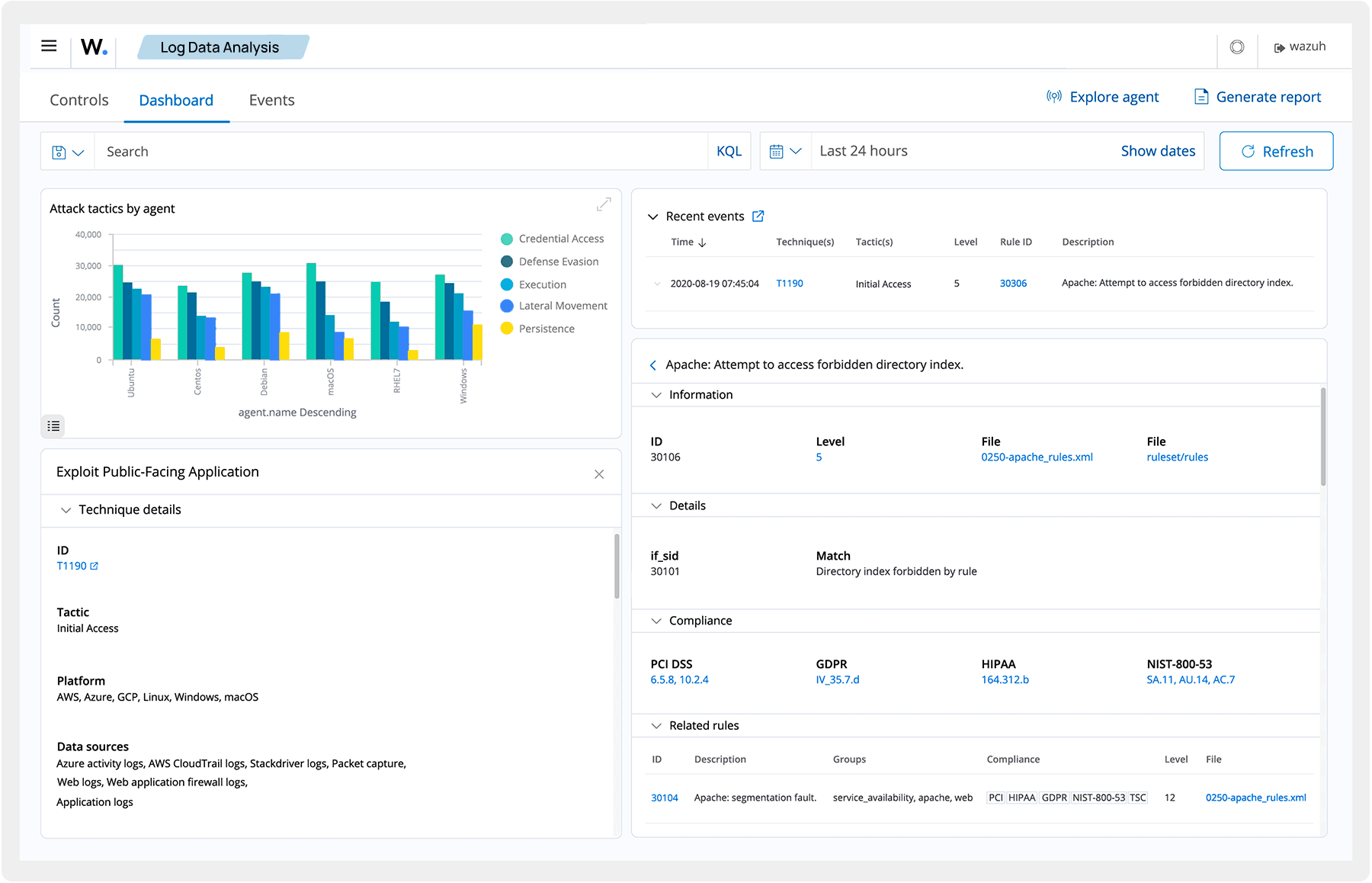
Organizations collect logs from diverse sources including operating systems, applications, network devices, and cloud services. Wazuh normalizes these varied log formats into a consistent structure for analysis. This normalization enables correlation across different log sources to detect complex attack patterns.
Log Collection Architecture
The Wazuh agent collects local logs from monitored endpoints and forwards them to the central server. Network devices and applications without agent support send logs directly via syslog protocol. Cloud services stream logs through native integrations or API connections.
Log data flows through the processing pipeline where parsing rules extract relevant fields. Custom decoders handle proprietary log formats from specialized applications. Organizations extend the platform with custom parsers to support any log source in their environment.
Operating System Logs
Collect authentication events, system changes, and application activities from all operating systems.
- Windows event logs (Security, System, Application)
- Linux syslog and systemd journal entries
- macOS unified logging system
- Unix audit daemon logs
Network Device Logs
Monitor network infrastructure for security events and configuration changes across devices.
- Firewall access and deny logs
- Router and switch syslog messages
- VPN connection and authentication logs
- Load balancer access logs
Application Security Logs
Track application behavior and security events from web applications and databases.
- Web server access and error logs
- Database audit trails
- Application authentication logs
- API gateway request logs
Security Analytics and Correlation
Wazuh applies correlation rules to detect attack sequences spanning multiple systems and log sources. The platform recognizes patterns indicating reconnaissance, lateral movement, and data exfiltration. These correlated alerts provide analysts with complete attack timelines rather than isolated events.
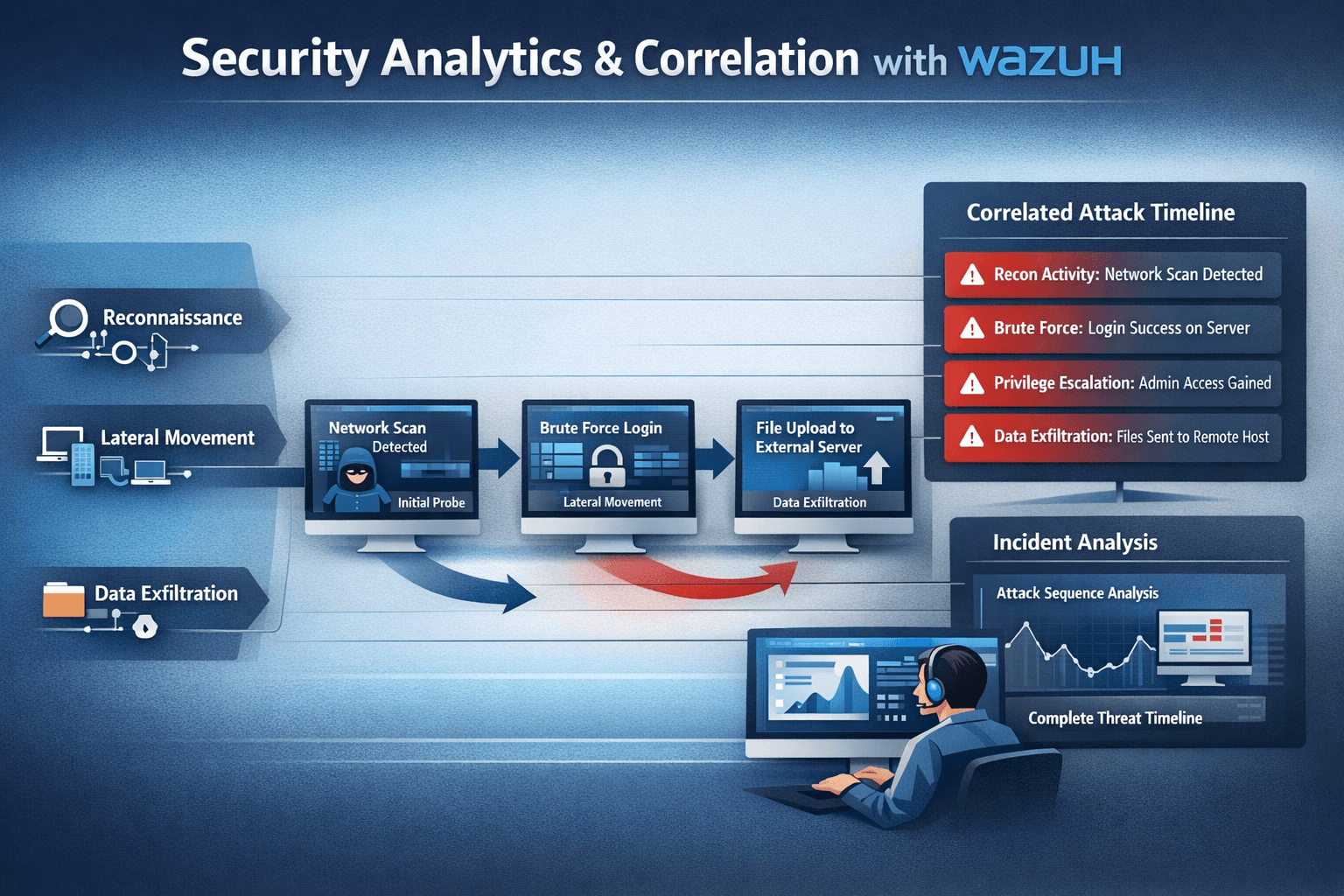
Search capabilities enable rapid investigation of security incidents. Analysts query historical log data to identify scope of compromise, trace attacker activities, and gather forensic evidence. The platform indexes log data for fast retrieval even across months of historical events.
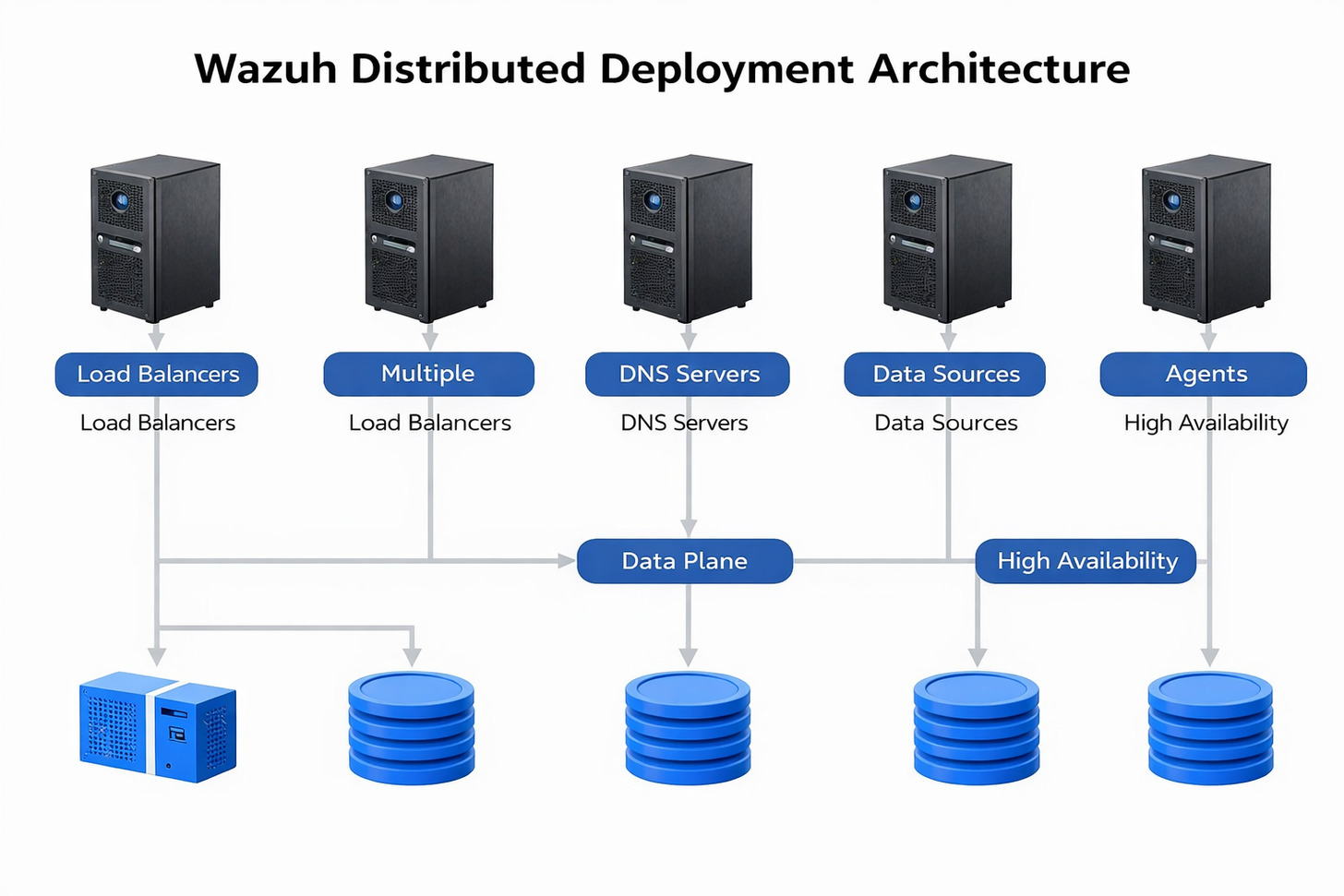
Flexible Deployment Architecture and Scalability
Organizations deploy Wazuh across various architectural patterns based on scale and requirements. Small environments run single-server deployments handling thousands of agents. Enterprise deployments scale to distributed architectures managing hundreds of thousands of endpoints across global infrastructure.
Deployment Models
The platform supports on-premises deployment for organizations requiring data sovereignty and complete control. Virtual machine images simplify deployment in VMware and Hyper-V environments. Container images enable Kubernetes deployments for cloud-native architectures.
On-Premises Deployment
Deploy Wazuh on organization-owned infrastructure for complete control over security data and system configuration.
- Full data sovereignty and control
- Integration with existing infrastructure
- Customizable network architecture
- No external data transfer requirements
- Hardware capacity planning flexibility
Cloud Deployment
Run Wazuh in cloud environments for elastic scalability and simplified infrastructure management.
- Rapid deployment and scaling
- Managed infrastructure benefits
- Multi-region deployment options
- Pay-as-you-grow cost model
- Cloud-native service integration
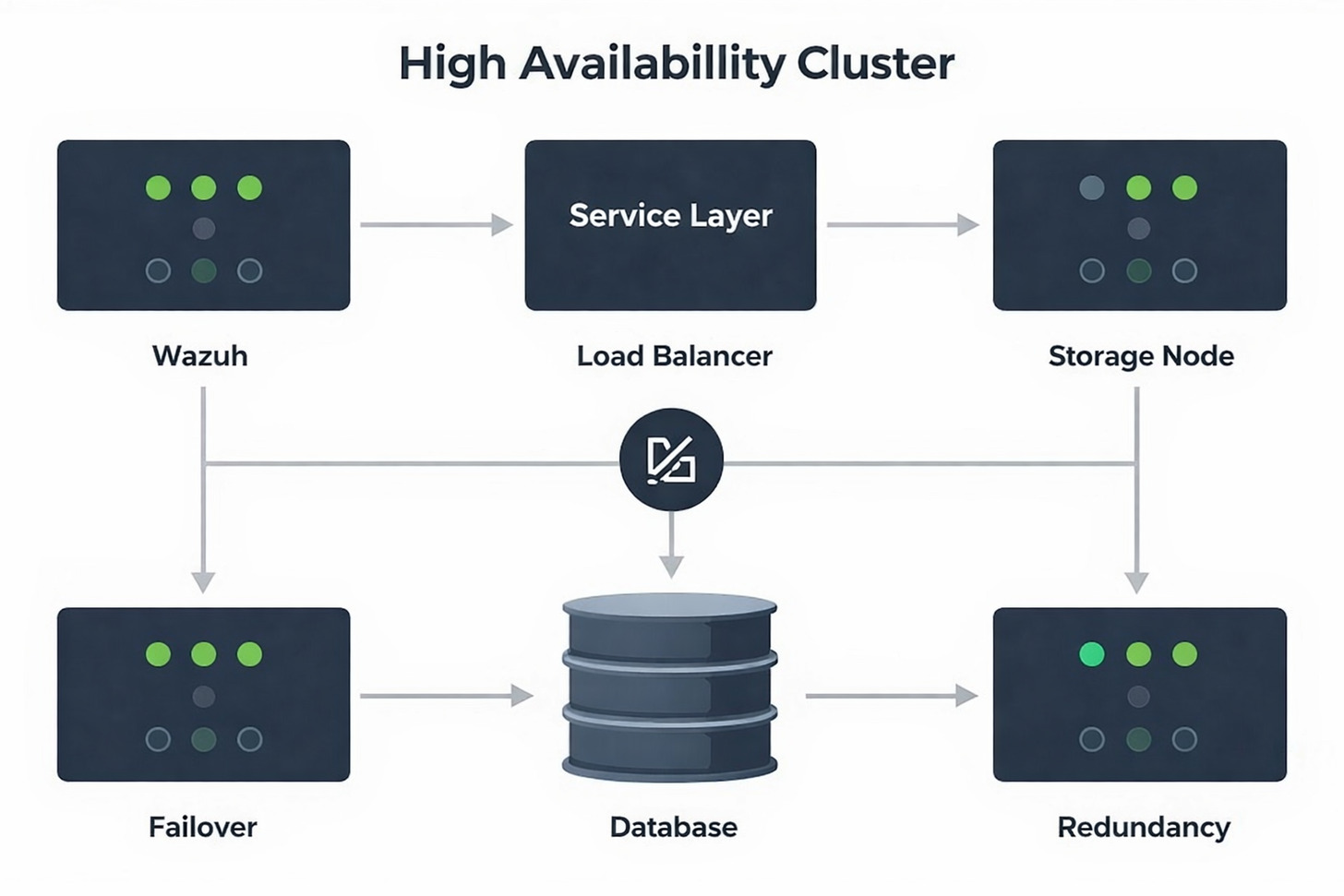
High Availability Configuration
Mission-critical environments require high availability to ensure continuous security monitoring. Wazuh supports cluster configurations where multiple server nodes share load and provide failover capability. Organizations deploy active-active clusters for maximum availability.
Database clustering ensures security data remains accessible during component failures. Elasticsearch clusters distribute indexed data across multiple nodes. This distribution provides both performance benefits and data redundancy.
Scaling Considerations
Organizations plan capacity based on agent count, event rate, and retention requirements. The platform scales vertically through more powerful servers or horizontally by adding cluster nodes. Performance monitoring helps identify scaling needs before capacity limits impact operations.
| Deployment Size | Agent Count | Events Per Second | Server Configuration | Storage Requirements |
| Small Environment | Up to 100 agents | 1,000 EPS | 4 CPU cores, 8 GB RAM | 100 GB for 90-day retention |
| Medium Environment | 100-1,000 agents | 10,000 EPS | 8 CPU cores, 16 GB RAM | 1 TB for 90-day retention |
| Large Environment | 1,000-10,000 agents | 100,000 EPS | 16 CPU cores, 32 GB RAM | 10 TB for 90-day retention |
| Enterprise Environment | 10,000+ agents | 1,000,000+ EPS | Clustered deployment | Calculated based on requirements |
Thriving Open Source Community and Ecosystem
Wazuh benefits from an active global community of security professionals, developers, and organizations. Community members contribute code improvements, share detection rules, and help other users through forums and documentation. This collaborative approach accelerates platform development and knowledge sharing.

The GitHub repository serves as the hub for platform development and community collaboration. Security researchers report vulnerabilities through responsible disclosure processes. Feature requests drive roadmap priorities based on community needs. Transparency in development builds trust and ensures alignment with user requirements.
Community Resources and Support
Extensive documentation covers installation, configuration, and use cases. Tutorial content helps new users get started quickly. Advanced guides address complex deployment scenarios and integrations. Community-contributed documentation fills gaps and shares real-world implementation experiences.
Learning Resources
- Comprehensive official documentation
- Video tutorials and webinars
- Blog articles on security topics
- Use case implementation guides
- Best practices documentation
Community Engagement
- Active user forums and discussions
- GitHub issue tracking and support
- Slack community channels
- Mailing lists for announcements
- Social media security community
Professional Services
- Commercial support subscriptions
- Professional consulting services
- Training and certification programs
- Managed security service providers
- Implementation partner network
Partner Ecosystem
Organizations leverage partner expertise for deployment, integration, and ongoing management. Certified partners provide implementation services, custom development, and managed security operations. The partner network spans consulting firms, managed service providers, and technology integrators.
Recent partnerships expand Wazuh availability and support in key markets. Collaborations with cybersecurity consultancies bring specialized expertise to complex deployments. Service providers build managed security offerings around the platform, making enterprise-grade security accessible to organizations lacking internal resources.
Real-World Use Cases and Implementation Scenarios
Organizations across industries deploy Wazuh to address specific security challenges. Financial institutions use the platform for fraud detection and regulatory compliance monitoring. Healthcare providers protect patient data while meeting HIPAA requirements. Technology companies secure development infrastructure and detect supply chain threats.
Financial Services Security
Banks and financial institutions face sophisticated threats targeting customer funds and sensitive data. Wazuh monitors transaction systems, detects fraud patterns, and ensures PCI DSS compliance for payment processing. Real-time alerting enables rapid response to suspicious activities before financial losses occur.
The platform tracks privileged user activities in financial systems. Audit trails document access to customer data and transaction processing systems. This visibility supports both security investigations and regulatory audit requirements.
Healthcare Data Protection
Healthcare organizations protect electronic health records and comply with HIPAA security requirements. Wazuh monitors access to patient data, detects unauthorized disclosure attempts, and documents security controls. File integrity monitoring ensures medical records remain unaltered and trustworthy.
Medical device security receives increased attention as connected devices proliferate. Wazuh monitors medical device network traffic, detects anomalous behavior, and alerts on potential device compromises. This visibility helps healthcare providers manage risks from legacy medical equipment.
Cloud Infrastructure Security
Organizations migrating to cloud environments need visibility across hybrid infrastructure. Wazuh monitors cloud resources, detects misconfigurations, and ensures consistent security policies across on-premises and cloud systems. Integration with cloud-native services provides comprehensive protection.
DevSecOps Integration
Development teams integrate Wazuh into CI/CD pipelines for security testing. The platform scans container images for vulnerabilities before deployment. Runtime monitoring detects security issues in production applications. This shift-left approach catches vulnerabilities early in development.
Infrastructure as code security becomes critical as teams automate deployments. Wazuh audits Terraform and CloudFormation templates for security misconfigurations. Policy enforcement prevents insecure infrastructure deployment.
Retail and E-Commerce Protection
Retail organizations protect customer payment information and defend against e-commerce fraud. Wazuh monitors point-of-sale systems, tracks payment card data access, and ensures PCI DSS compliance. Web application monitoring detects attacks targeting online shopping platforms.
Supply chain security extends monitoring to vendor systems and third-party integrations. The platform tracks access from external partners, detects suspicious activities, and documents vendor compliance with security requirements.
Getting Started with Wazuh Implementation
Organizations begin Wazuh deployment by planning their architecture and identifying initial use cases. Starting with a limited scope allows teams to gain experience before expanding to full production deployment. Pilot projects demonstrate value and identify configuration requirements.

Planning Your Deployment
Successful implementations start with clear objectives and scope definition. Organizations identify critical systems requiring immediate monitoring, compliance requirements driving deployment, and integration points with existing security tools. This planning phase prevents scope creep and ensures focused implementation.
Installation and Configuration
Multiple installation methods accommodate different deployment scenarios. Package managers provide simple installation on Linux systems. Docker containers enable rapid testing and development environments. Automated deployment scripts support large-scale enterprise rollouts.
The installation guide provides step-by-step instructions for all supported platforms. Organizations follow documented procedures to deploy servers, configure agents, and establish communication. Configuration management tools automate agent deployment across large endpoint populations.
Quick Start Guide
Get Wazuh running in your environment within hours using the quick start installation process.
- Single command installation option
- Pre-configured default settings
- Automatic service startup
- Basic agent enrollment process
Production Deployment
Follow comprehensive guides for enterprise-grade production deployments with high availability and scalability.
- Cluster configuration instructions
- Load balancing setup guidance
- Backup and recovery procedures
- Performance tuning recommendations
Integration Configuration
Connect Wazuh with existing security tools and workflows to maximize value and operational efficiency.
- SIEM integration setup guides
- Ticketing system connections
- Communication platform webhooks
- Custom integration examples
Optimization and Tuning
Initial deployments generate alerts requiring tuning to match organizational environment and risk tolerance. Security teams adjust detection rule thresholds, create custom rules for unique applications, and configure alert prioritization. This tuning process reduces false positives while maintaining high detection rates.
Performance monitoring identifies bottlenecks and capacity constraints. Organizations adjust resource allocation, optimize rule evaluation, and tune indexing settings for optimal performance. Regular performance reviews ensure the platform scales with growing monitoring requirements.
Advanced Security Features and Capabilities
Beyond core SIEM functionality, Wazuh provides advanced capabilities addressing sophisticated security requirements. Machine learning enhances anomaly detection accuracy. Security configuration assessment automates compliance checking. Container security features protect cloud-native applications throughout their lifecycle.
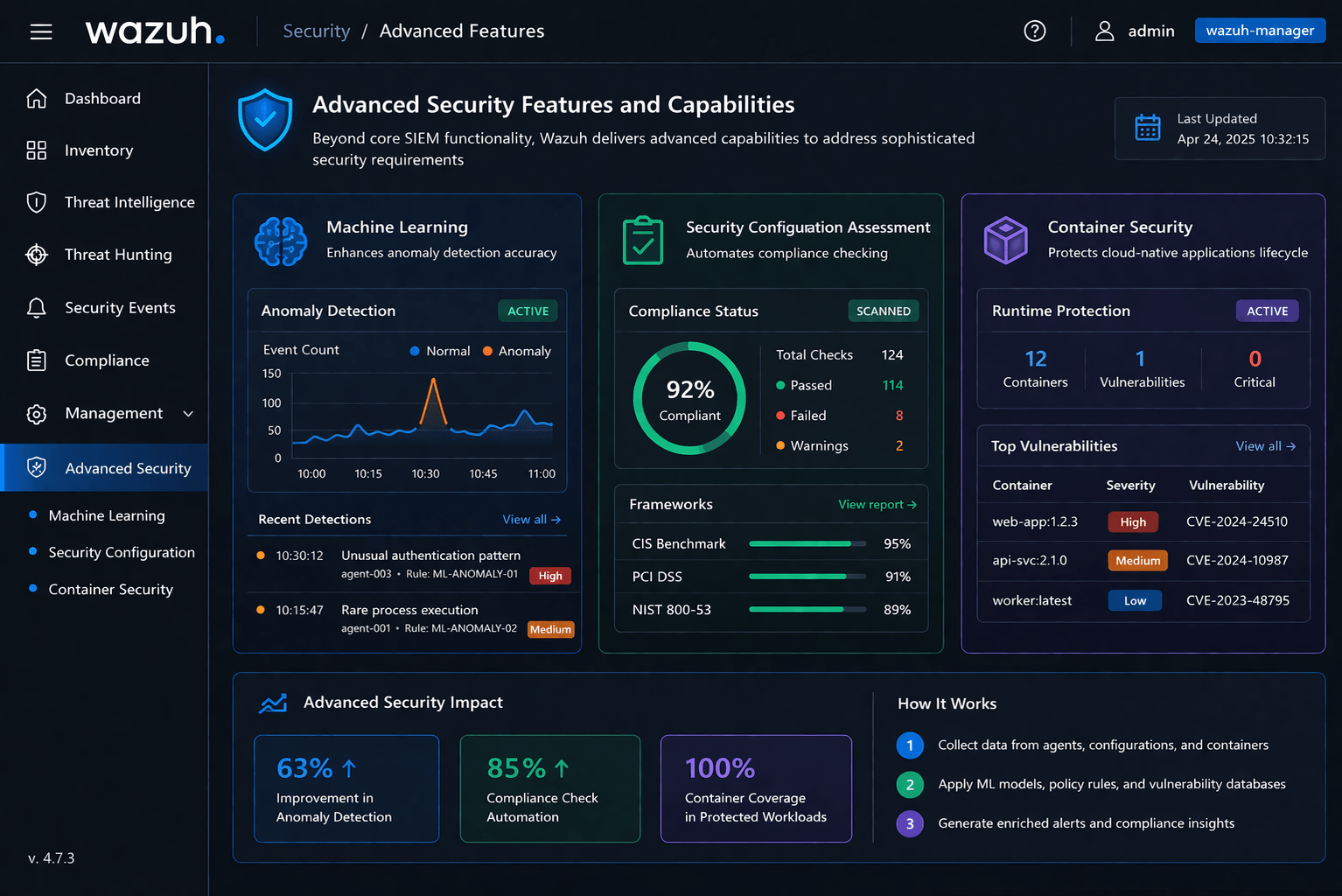
Machine Learning and Behavioral Analysis
Behavioral analysis capabilities detect threats that evade signature-based detection. The system establishes baseline behavior for users, systems, and applications. Deviations from established patterns trigger alerts for investigation. This approach identifies insider threats, compromised accounts, and zero-day exploits.
Machine learning models improve detection accuracy over time by learning from analyst feedback. The system adapts to environment-specific patterns and reduces false positive rates. Organizations deploy custom models trained on their unique security data for maximum relevance.
Threat Hunting and Investigation
Security analysts use Wazuh for proactive threat hunting activities. The platform provides flexible query capabilities for exploring security data and testing hypotheses. Threat hunters search for indicators of compromise, analyze attacker tactics, and uncover hidden threats.
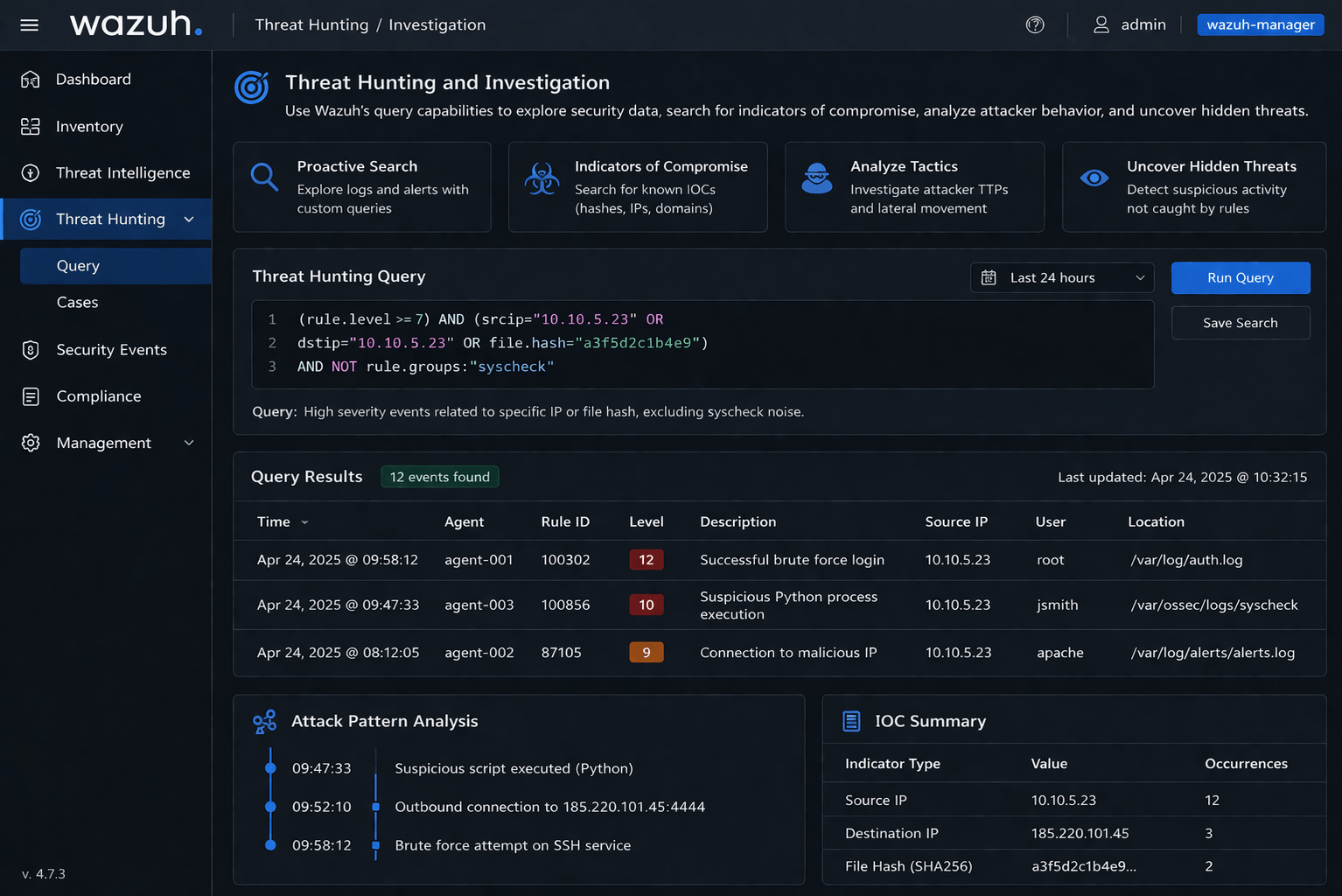
Investigation workflows help analysts follow security incidents from detection through resolution. The platform correlates related events, highlights suspicious patterns, and presents relevant context. These capabilities accelerate investigation and reduce mean time to respond.
Security Orchestration Capabilities
Advanced automation capabilities enable sophisticated security orchestration workflows. Organizations chain multiple response actions together, coordinate responses across security tools, and implement complex decision logic. These orchestration capabilities transform Wazuh into the central coordination point for security operations.
Custom scripts and integrations extend automation beyond built-in capabilities. Security teams develop playbooks addressing organization-specific scenarios. API access enables programmatic control of all platform functions for maximum flexibility.
Wazuh Positioning in the Security Tools Landscape
The security tools market offers numerous options ranging from open source platforms to commercial enterprise solutions. Wazuh distinguishes itself through comprehensive capabilities, open source transparency, and deployment flexibility. Organizations compare Wazuh against commercial SIEM products and alternative open source options.

Open Source vs Commercial Solutions
Commercial security products offer vendor support and pre-packaged integrations but require significant licensing costs. Wazuh provides comparable capabilities without licensing fees while maintaining complete transparency. Organizations access enterprise features without vendor lock-in or recurring subscription cos
Feature Comparison with Leading Platforms
Wazuh delivers core SIEM and XDR capabilities comparable to leading commercial platforms. Threat detection, log management, compliance monitoring, and incident response features match or exceed proprietary alternatives. Integration ecosystems continue expanding through community contributions and official development.
| Capability | Wazuh | Commercial SIEM Average | Alternative Open Source |
| Log Management | Comprehensive | Comprehensive | Moderate |
| Threat Detection | Advanced | Advanced | Basic |
| Compliance Reporting | Built-in | Built-in | Limited |
| Cloud Integration | Native | Native | Partial |
| Total Cost of Ownership | Very Low | Very High | Low |
Future Developments and Platform Roadmap
Wazuh development continues advancing the platform with new capabilities and improvements. The roadmap reflects community priorities and emerging security challenges. Recent updates demonstrate commitment to innovation while maintaining stability and backward compatibility.
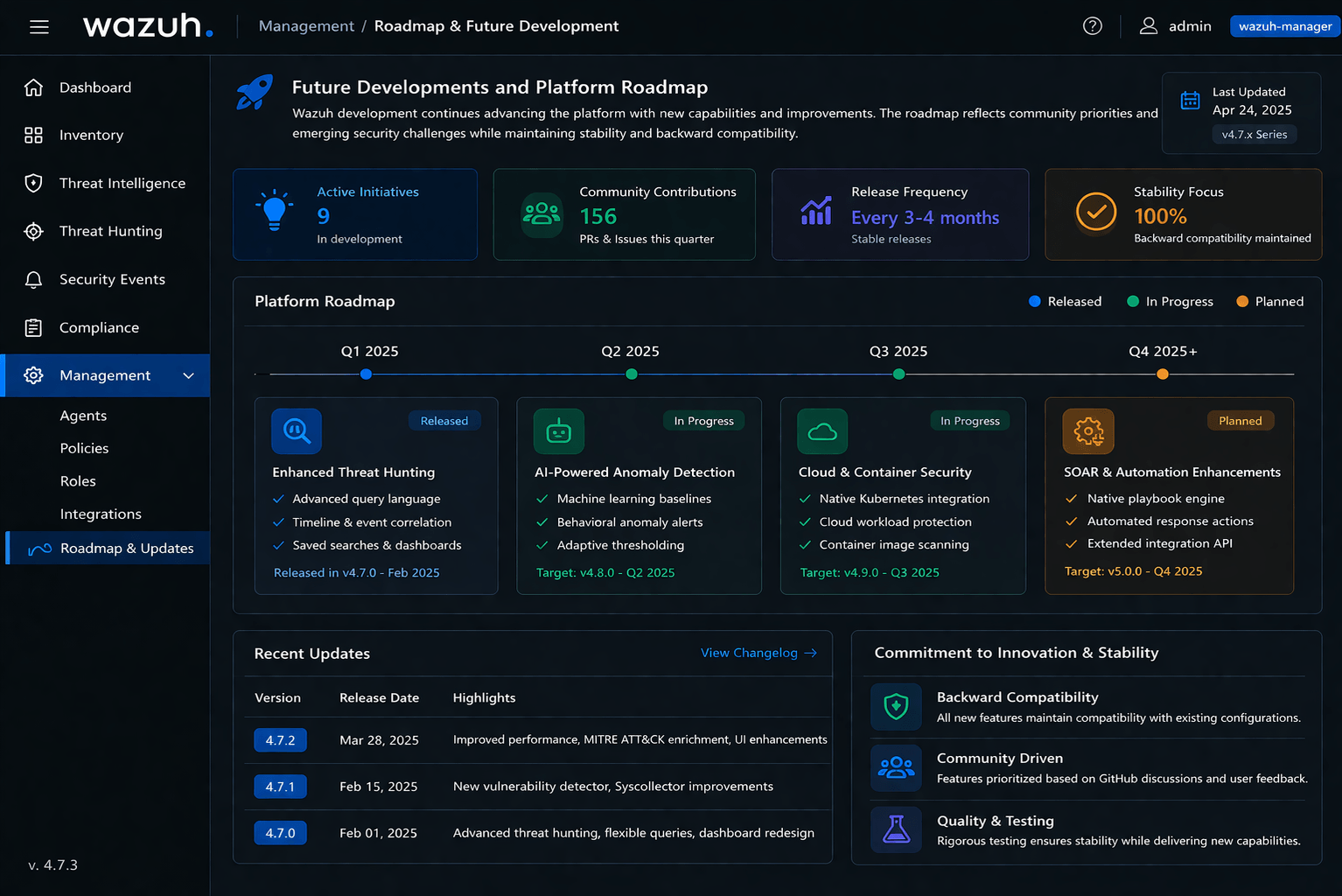
Recent Platform Enhancements
Recent Wazuh releases introduced significant improvements across multiple areas. Enhanced cloud security monitoring provides deeper visibility into AWS, Azure, and Google Cloud environments. Container security features expanded to cover complete container lifecycle management. Performance optimizations enable higher event processing rates with reduced resource consumption.
Agentic AI integration represents a major platform evolution. Early demonstrations show AI agents interacting with Wazuh through APIs to automate complex workflows. These capabilities promise to reduce operational overhead while accelerating response to sophisticated threats.
Emerging Threat Protection
The platform continuously adds detection capabilities for emerging threats. Recent blog content demonstrates Wazuh detecting and responding to new ransomware variants, credential stealers, and critical vulnerabilities. Security researchers contribute detection rules addressing zero-day exploits and advanced persistent threat campaigns.
Integration Expansion
New partnerships and integrations expand Wazuh ecosystem reach. Managed security service providers offer Wazuh-based monitoring services to organizations lacking internal security teams. Technology partnerships bring specialized capabilities through integrated solutions. These collaborations make enterprise security accessible to organizations of all sizes.
Taking the Next Steps with Wazuh
Organizations seeking comprehensive security monitoring capabilities find Wazuh delivers enterprise functionality without proprietary constraints. The platform protects infrastructure spanning traditional data centers, cloud environments, and hybrid architectures. Open source transparency ensures organizations maintain complete control over their security posture.

Starting with Wazuh requires minimal investment beyond infrastructure and team time. Organizations download the software, deploy it across pilot systems, and begin monitoring within hours. Community resources provide guidance through common deployment scenarios and configuration challenges. Success with initial deployments builds confidence for expansion to full production coverage.
Security teams gain multiple benefits from Wazuh adoption. Comprehensive visibility eliminates blind spots across monitored infrastructure. Automated detection and response capabilities accelerate threat containment. Compliance monitoring reduces audit preparation burden. Organizations protect their assets while controlling security costs through open source adoption.
The open source security community continues growing as organizations recognize the value of transparent, collaborative security tools. Wazuh exemplifies this movement, delivering capabilities that match proprietary alternatives while maintaining the freedom and flexibility that drive innovation. Organizations joining this community contribute to the future of security monitoring while protecting their own infrastructure today.
Conclusion
At Atrity, we understand that modern organizations require robust, scalable, and cost-effective security solutions to protect their evolving IT infrastructure. Wazuh stands out as a powerful platform that delivers comprehensive visibility, advanced threat detection, and automated incident response without the limitations of proprietary tools.
By leveraging Wazuh, organizations can strengthen their security posture across cloud, on-premises, and hybrid environments while ensuring compliance with industry standards. Its flexibility, open-source nature, and enterprise-grade capabilities make it an ideal choice for businesses looking to modernize their security operations.
At Atrity, we are committed to helping organizations implement and optimize security solutions like Wazuh to achieve proactive threat management and operational excellence. As cyber threats continue to evolve, adopting intelligent and unified platforms such as Wazuh is no longer optional—it is essential for building a resilient and secure digital future.
 Read More
Read More