
What is Ransomware: Defining the Digital Extortion Threat
Ransomware represents a specific category of malicious software designed to deny access to computer systems or data until victims pay a ransom. Unlike traditional malware that steals information quietly, ransomware announces its presence immediately, encrypting files and displaying demands that victims cannot ignore.
The attack mechanism combines technical sophistication with psychological pressure. Cybercriminals employ military-grade encryption algorithms that render data completely inaccessible without the correct decryption key. Victims face countdown timers threatening permanent data loss or increased payment demands, creating urgent decision-making pressure.
Core Components of Ransomware Operations
Modern ransomware attacks involve several distinct technical and operational elements that work together to maximize attacker success. Understanding these components helps organizations recognize threats and implement appropriate defenses.
Encryption Engine
The technical core that locks victim data using advanced cryptographic algorithms.
- Military-grade encryption standards like AES-256
- Asymmetric key systems preventing local decryption
- Selective targeting of valuable file types
- Fast encryption to minimize detection time
Payment Infrastructure
Systems designed to collect ransom payments while maintaining attacker anonymity.
- Cryptocurrency wallets for untraceable transactions
- Tor-based payment portals hidden on dark web
- Automated payment verification systems
- Customer support chat for payment assistance
Communication Mechanism
Methods ransomware uses to contact command servers and receive instructions.
- Command and control server connections
- Encrypted communication channels
- Domain generation algorithms for resilience
- Fallback communication pathways
Propagation System
Techniques enabling ransomware to spread across networks and multiply impact.
- Network scanning for vulnerable systems
- Lateral movement across connected devices
- Exploitation of shared resources
- Worm-like self-replication capabilities
Evolution from Nuisance to Business Threat
Early ransomware variants emerged in the late nineteen-eighties, remaining relatively unsophisticated for decades. The AIDS Trojan, distributed via floppy disk in nineteen-eighty-nine, demanded victims mail payments to a post office box in Panama. These primitive attacks caused minimal damage and attracted little attention.
The landscape transformed dramatically with cryptocurrency adoption. Bitcoin provided attackers with truly anonymous payment mechanisms, removing previous barriers to large-scale operations. Combined with advanced encryption and professional business models, ransomware evolved into a multi-billion-dollar criminal industry.
Today’s ransomware operations function like legitimate businesses, complete with customer service departments, affiliate programs, and service-level agreements. Some groups even offer decryption guarantees and technical support to ensure victims can successfully pay ransoms and recover data.
How Ransomware Works: The Attack Lifecycle Explained
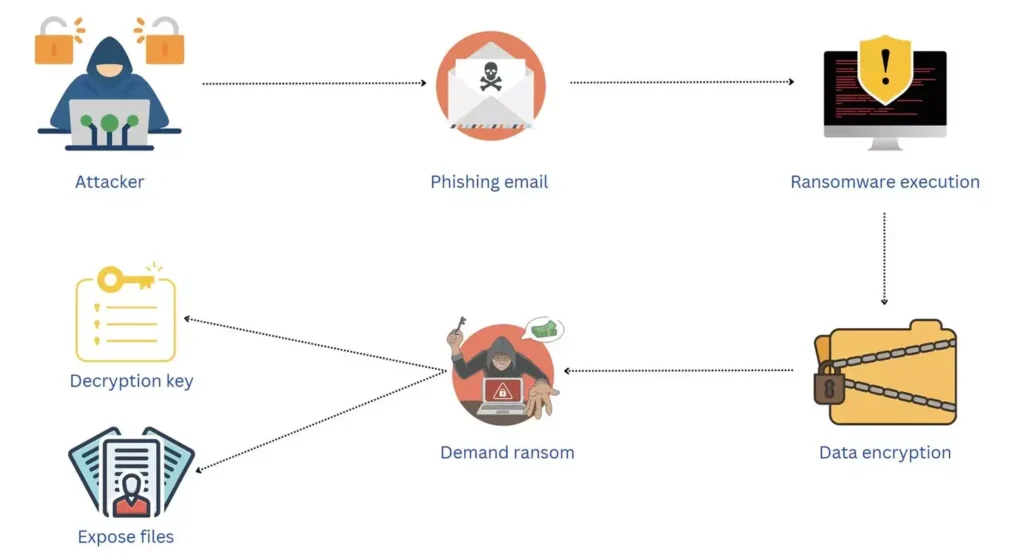
Ransomware attacks follow predictable patterns from initial infection through final extortion. Understanding this lifecycle enables organizations to implement defenses at multiple stages, significantly reducing attack success rates.
Stage One: Initial Compromise and Infection
The attack begins when ransomware enters an organization through various infection vectors. Phishing emails remain the most common entry point, with attackers crafting convincing messages that trick users into clicking malicious links or opening infected attachments. These emails often impersonate legitimate services, urgent business communications, or trusted contacts.
Drive-by downloads represent another frequent infection method. Victims visit compromised websites containing malicious code that exploits browser or plugin vulnerabilities. The infection occurs automatically without user action, making these attacks particularly dangerous. Legitimate websites can unknowingly host this malicious code after attackers compromise their web servers.
Remote Desktop Protocol vulnerabilities provide direct access to networks. Attackers scan the internet for exposed RDP connections, then use brute force attacks or stolen credentials to gain entry. Once inside, they manually deploy ransomware with precision timing to maximize damage.
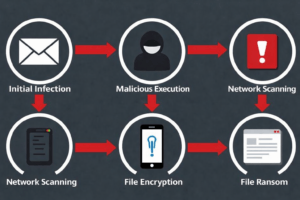
Stage Two: Execution and Establishment
After gaining access, ransomware establishes persistence to survive system reboots and maintain control. The malware modifies system registries, creates scheduled tasks, or installs itself as a service that launches automatically. These persistence mechanisms ensure attackers maintain access even if users attempt basic remediation.
Modern ransomware variants often remain dormant initially, avoiding immediate detection. During this reconnaissance phase, malware maps the network, identifies valuable targets, and locates backup systems. Attackers gather intelligence about organizational structure, data locations, and security controls before launching the encryption phase.
Privilege escalation occurs during this stage. Attackers exploit system vulnerabilities or misconfigurations to gain administrative access. Higher privileges enable ransomware to disable security software, delete backup files, and encrypt files across entire networks rather than single user accounts.
Stage Three: Reconnaissance and Lateral Movement
Sophisticated ransomware operations invest significant time in network exploration. Attackers identify critical systems, locate sensitive data repositories, and map network connections between systems. This reconnaissance ensures maximum impact when encryption begins.
Lateral movement techniques allow ransomware to spread beyond the initial infection point. Attackers exploit trust relationships between systems, steal credentials from memory, and abuse administrative tools like PowerShell. Each compromised system provides additional access points and increases the eventual encryption scope.
Backup destruction represents a critical preparation step. Attackers specifically target backup systems, shadow copies, and disaster recovery infrastructure. By eliminating recovery options before encryption, criminals ensure victims face genuine data loss threats, increasing ransom payment likelihood.
| Attack Stage | Attacker Actions | Detection Opportunities | Defense Strategies |
| Initial Access | Phishing emails, exploit kits, RDP brute force, software vulnerabilities | Email filters, unusual login patterns, network anomalies | Security awareness training, email security, patch management, MFA |
| Execution | Payload deployment, persistence establishment, security tool disabling | Process monitoring, registry changes, service creation | Endpoint protection, application whitelisting, behavior analysis |
| Reconnaissance | Network scanning, data discovery, backup identification, credential harvesting | Unusual network traffic, scanning activity, access pattern changes | Network segmentation, access controls, monitoring and alerting |
| Lateral Movement | Credential theft, privilege escalation, system-to-system propagation | Abnormal authentication, tool usage, cross-system connections | Least privilege policies, credential protection, network monitoring |
| Impact | Mass file encryption, backup deletion, ransom note deployment | File system changes, high disk activity, encryption patterns | Immutable backups, file integrity monitoring, rapid response |
Stage Four: Encryption and Impact
The encryption phase executes with devastating speed once attackers decide to strike. Modern ransomware can encrypt thousands of files per minute, quickly rendering entire systems useless. The malware targets specific file types most valuable to organizations including documents, databases, images, and archives.
Encryption occurs using asymmetric cryptography combining public and private keys. The ransomware generates a unique encryption key for the victim’s files, then encrypts that key using the attacker’s public key. Without the attacker’s private key, decryption becomes mathematically impossible even with unlimited computing power.
File extensions change visibly during encryption, often appending distinctive markers that identify the ransomware variant. Users notice documents becoming inaccessible and system performance degrading as encryption consumes computing resources. Some variants display fake system update screens to disguise the encryption process.
Stage Five: Extortion and Demands
Following successful encryption, ransomware displays ransom notes explaining the situation and providing payment instructions. These notes typically appear as text files in every encrypted directory, desktop wallpaper changes, or full-screen lock screens preventing system access.
Payment demands vary dramatically based on victim size and perceived ability to pay. Small businesses might face demands between five thousand to fifty thousand dollars, while large enterprises encounter million-dollar demands. Attackers research victims beforehand, tailoring demands to maximize payment probability while staying below insurance deductibles.
Countdown timers create artificial urgency, threatening to increase demands or permanently delete decryption keys if victims delay payment. Some variants implement progressive ransom increases, doubling demands after deadline passages. This psychological pressure pushes victims toward hasty decisions without proper evaluation.
Modern ransomware groups increasingly employ double extortion tactics. Beyond encrypting data, attackers exfiltrate sensitive information before encryption, threatening to publish stolen data if victims refuse payment. This approach works especially effectively against organizations with regulatory compliance obligations or reputational concerns.
Types of Ransomware: Understanding Attack Variants
Ransomware has diversified into numerous variants, each employing distinct techniques and targeting specific vulnerabilities. Recognizing these different types helps security teams implement appropriate defenses and prepare response strategies.
Crypto Ransomware: The File Encryption Threat
Crypto ransomware represents the most prevalent variant, focusing exclusively on encrypting victim files. These attacks leave systems operational but render data completely inaccessible. Users can log in, browse folders, and see file names, but cannot open or use encrypted content.
This ransomware type targets specific file extensions associated with valuable data. Documents, spreadsheets, databases, images, videos, and archives receive priority. System files typically remain untouched to maintain basic functionality, ensuring victims can access payment instructions and complete ransom transactions.
Crypto ransomware variants include some of the most damaging attacks in history. WannaCry infected over two hundred thousand computers across one hundred fifty countries in twenty-seventeen, exploiting a Windows vulnerability to spread automatically between systems. The attack paralyzed hospitals, disrupted manufacturing, and caused billions in damages globally.

Locker Ransomware: System Access Denial
Locker ransomware takes a different approach by blocking system access entirely rather than encrypting individual files. Victims encounter lock screens preventing login, effectively rendering computers completely unusable. The underlying files remain unencrypted, but inaccessibility creates equivalent disruption.
These attacks prove easier to remediate than crypto ransomware since files themselves remain intact. Security professionals can often remove locker ransomware through safe mode access, system restore functions, or bootable recovery tools. However, less technical users face significant challenges recovering access without paying ransoms.
Mobile devices represent primary locker ransomware targets. Android ransomware variants lock device screens using accessibility features or device administrator privileges. Victims cannot access apps, make calls, or use device functions until removing the malware or paying demanded ransoms.
Double Extortion: Data Theft and Encryption Combined
Double extortion represents the evolution of ransomware tactics beyond simple encryption. Attackers exfiltrate sensitive data before encrypting systems, then threaten to publish stolen information if victims refuse payment. This approach creates dual pressure points increasing payment likelihood.
Organizations with strong backup systems historically could recover from encryption without paying ransoms. Double extortion eliminates this advantage by threatening reputational damage, regulatory penalties, and competitive intelligence exposure. Even organizations capable of recovering data face compelling reasons to pay.
The Maze ransomware group pioneered this approach in twenty-nineteen, publishing stolen data from non-paying victims on dedicated leak sites. Other groups quickly adopted the tactic, with some establishing auction systems selling stolen data to highest bidders when victims refuse payment.
Single Extortion Model
Traditional ransomware approach focusing solely on encryption and access denial.
- Encrypts files or locks systems
- Demands payment for decryption key
- Backup restoration enables recovery
- Limited leverage against prepared victims
- Lower payment rates from sophisticated targets
Double Extortion Model
Advanced approach combining data theft with encryption for maximum pressure.
- Steals data before encrypting systems
- Threatens to publish sensitive information
- Backups cannot prevent data exposure
- Regulatory and reputational consequences
- Higher payment rates even from prepared organizations
Ransomware-as-a-Service: Criminal Business Model
Ransomware-as-a-Service platforms operate like legitimate software businesses, providing attack tools to affiliates in exchange for profit-sharing arrangements. Developers create and maintain ransomware while affiliates handle victim identification and attack execution. This specialization dramatically lowers entry barriers for cybercriminals.
RaaS platforms provide comprehensive attack infrastructure including encryption tools, payment portals, victim communication systems, and technical support. Some platforms guarantee earnings, offer performance bonuses, and maintain sophisticated marketing programs recruiting new affiliates. The business model mirrors legitimate SaaS operations in organizational structure.
DarkSide ransomware exemplifies successful RaaS operations. The group maintained a professional reputation, avoided attacking hospitals and critical infrastructure initially, and provided reliable decryption after payment. Their attack on Colonial Pipeline in twenty-twenty-one caused widespread fuel shortages across the American East Coast, drawing unprecedented law enforcement attention.
Specialized Ransomware Variants
Beyond primary categories, numerous specialized ransomware variants target specific systems or employ unique techniques. Understanding these variants helps organizations assess their specific risk exposure and implement appropriate defenses.
Scareware
Fake security software displaying false virus warnings and demanding payment for removal. Less sophisticated than true ransomware but effective against non-technical users. Often spread through malicious advertisements and social engineering tactics.
Doxware
Threatens to publish personal or embarrassing information unless victims pay ransoms. Targets individuals rather than organizations. Often claims to have accessed webcams or browsing history, though many instances involve bluffing without actual data theft.
Industrial Ransomware
Specialized variants targeting industrial control systems and operational technology environments. Attacks manufacturing plants, utilities, and critical infrastructure. Can cause physical damage beyond data loss by disrupting industrial processes.
Notable Ransomware Attacks: Real-World Impact and Lessons
Examining high-profile ransomware attacks reveals how these threats materialize in practice and identifies patterns organizations can learn from. These case studies demonstrate the devastating real-world consequences of inadequate security.
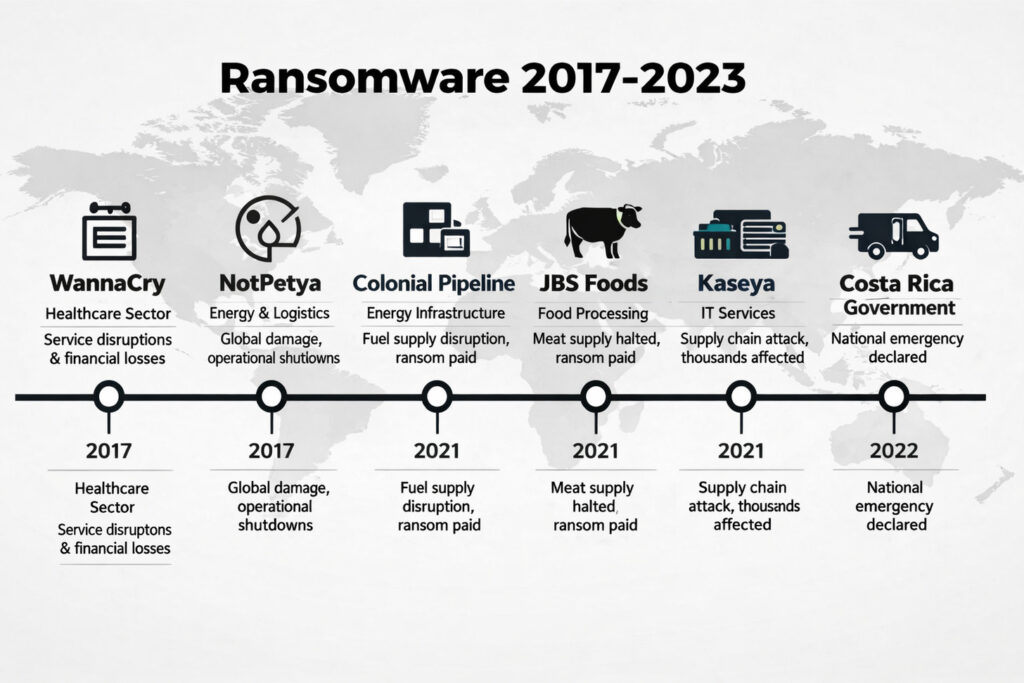
WannaCry: The Global Wake-Up Call
WannaCry emerged in May twenty-seventeen as a watershed moment for ransomware awareness. The attack exploited EternalBlue, a Windows vulnerability allegedly discovered by the National Security Agency and later leaked by hackers. Within hours, WannaCry infected over two hundred thousand computers across one hundred fifty countries.
The British National Health Service experienced particularly severe disruption. Hospitals canceled surgeries, emergency rooms diverted ambulances, and medical staff resorted to paper records. The attack cost the NHS approximately one hundred million pounds in remediation and disrupted services for over nineteen thousand appointments.
WannaCry incorporated worm-like propagation, automatically spreading between vulnerable systems without human intervention. This self-replicating capability enabled rapid global distribution but ultimately contributed to the attack’s containment. A security researcher discovered a kill switch domain in the malware code, registering it to halt further infections.
The attack highlighted critical vulnerabilities in organizational patch management. Microsoft had released security updates addressing EternalBlue two months before WannaCry appeared, yet countless organizations failed to deploy patches. This lesson emphasizes the importance of timely security updates across all systems.
NotPetya: The Most Destructive Cyberattack
NotPetya launched in June twenty-seventeen, initially appearing as another ransomware variant targeting Ukrainian organizations. Analysis quickly revealed something more sinister: NotPetya was destructive malware disguised as ransomware, designed to cause maximum damage rather than generate ransom payments.
The attack spread globally through corporate networks, causing over ten billion dollars in damages. Shipping giant Maersk experienced complete IT infrastructure paralysis, requiring reinstallation of forty-five thousand computers. Pharmaceutical company Merck suffered manufacturing disruptions lasting months. FedEx subsidiary TNT Express faced similar devastation.
NotPetya’s initial infection vector exploited compromised Ukrainian accounting software, demonstrating supply chain attack risks. The malware then leveraged EternalBlue and credential-stealing tools to spread rapidly. Unlike genuine ransomware, NotPetya rendered data permanently unrecoverable even if victims paid ransoms.
Government agencies attributed NotPetya to Russian military intelligence, marking one of the first major destructive cyberattacks attributed to a nation-state. The incident blurred lines between cybercrime and cyber warfare, raising questions about appropriate responses to state-sponsored attacks disguised as criminal operations.
Colonial Pipeline: Critical Infrastructure Under Attack
The May twenty-twenty-one Colonial Pipeline ransomware attack demonstrated critical infrastructure vulnerability. DarkSide ransomware group compromised Colonial’s IT network through a single compromised password, eventually forcing the company to shut down operations preemptively to prevent operational technology compromise.
The pipeline transports forty-five percent of fuel supplies to America’s East Coast. The shutdown triggered fuel shortages, panic buying, and significant price increases. Colonial paid a four-point-four million-dollar ransom in Bitcoin to obtain decryption tools, though recovery efforts continued for weeks regardless.
Federal investigators recovered approximately half the ransom payment by tracing Bitcoin transactions and seizing cryptocurrency wallets. This recovery provided rare success in ransomware payment recovery but highlighted investigative capabilities that might deter future attacks or encourage more sophisticated cryptocurrency laundering.
The incident prompted executive action on critical infrastructure cybersecurity, new federal regulations, and increased information sharing between government and private sector. Colonial Pipeline demonstrated how ransomware attacks transcend individual companies, creating broader economic and social consequences.
| Attack Name | Year | Variant Type | Primary Targets | Estimated Damage | Key Lessons |
| WannaCry | 2017 | Crypto ransomware with worm capabilities | Healthcare, government, businesses globally | $4 billion | Patch management critical, network segmentation essential |
| NotPetya | 2017 | Destructive wiper disguised as ransomware | Logistics, pharmaceuticals, manufacturing | $10 billion | Supply chain risks, backup immutability, state-sponsored threats |
| Colonial Pipeline | 2021 | DarkSide RaaS | Critical infrastructure, energy sector | $4.4 million ransom + operational costs | Credential security, OT/IT separation, infrastructure protection |
| JBS Foods | 2021 | REvil RaaS | Food supply chain, agriculture | $11 million ransom | Supply chain impacts, rapid response importance |
| Kaseya VSA | 2021 | REvil supply chain attack | MSPs and their clients (1,500+ companies) | $70 million ransom demand | Third-party risk management, vendor security assessment |
Ransomware Targeting Indian Organizations
Indian organizations face increasing ransomware threats across multiple sectors. Healthcare institutions experienced particularly aggressive targeting during the pandemic, with attackers exploiting overwhelmed IT resources and critical operational requirements that discourage extended downtime.
Manufacturing facilities encounter sophisticated attacks combining ransomware with industrial espionage. Attackers steal intellectual property and production data before encrypting systems, creating multi-layered extortion scenarios. Small and medium enterprises often lack resources to implement comprehensive defenses, making them attractive targets.
Financial services and banking sectors face double extortion attacks threatening to expose customer data and trigger regulatory penalties. The Reserve Bank of India has issued multiple advisories highlighting ransomware risks and mandating improved cybersecurity measures across financial institutions.
Ransomware Distribution Methods: How Attacks Begin
Understanding ransomware distribution vectors enables organizations to implement targeted defenses at attack entry points. Most successful attacks exploit human factors rather than purely technical vulnerabilities, emphasizing the importance of security awareness alongside technical controls.
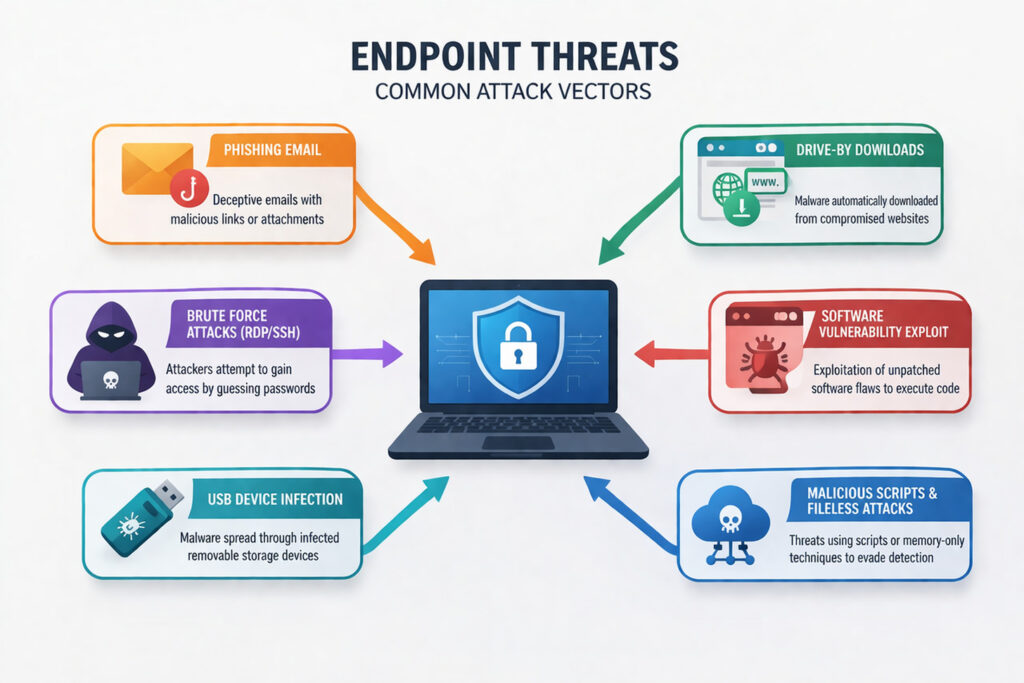
Phishing Emails: The Primary Attack Vector
Phishing remains the most common ransomware distribution method, accounting for over ninety percent of successful infections. Attackers craft convincing emails impersonating legitimate organizations, colleagues, or business partners. These messages manipulate recipients into clicking malicious links or opening infected attachments.
Modern phishing campaigns demonstrate remarkable sophistication. Attackers research targets extensively, referencing actual business relationships, recent transactions, or current events to build credibility. Emails might appear to come from company executives, trusted vendors, or government agencies, using spoofed addresses and authentic-looking formatting.
Attachment-based phishing typically delivers malicious Microsoft Office documents with embedded macros. When users enable macros, the malicious code executes, downloading and installing ransomware. Attackers disguise these documents as invoices, shipping notifications, tax documents, or urgent business communications that prompt immediate action.
Link-based phishing redirects victims to compromised websites hosting exploit kits or malware downloads. These sites might mimic legitimate login pages to steal credentials, or automatically download ransomware through browser vulnerabilities. Some sophisticated campaigns create entire fake websites that appear legitimate for weeks before launching attacks.
Remote Desktop Protocol Exploitation
Exposed Remote Desktop Protocol connections provide direct network access to attackers. Organizations often configure RDP for remote employee access but fail to implement adequate security controls. Attackers scan the internet for exposed RDP ports, then attempt to gain access through various methods.
Brute force attacks systematically test common passwords and username combinations against RDP connections. Attackers use automated tools testing thousands of credentials daily until successful authentication occurs. Weak passwords, default credentials, or commonly used combinations enable rapid compromise.
Credential stuffing leverages username and password combinations leaked from previous data breaches. Since users frequently reuse passwords across services, credentials from unrelated breaches often work on RDP connections. Attackers purchase or download massive credential databases, automating testing against potential targets.
Once inside through RDP, attackers gain legitimate system access that security tools struggle to distinguish from authorized remote workers. This access enables manual ransomware deployment, allowing attackers to disable security software, delete backups, and encrypt systems during off-hours when detection likelihood decreases.
Software Vulnerabilities and Exploit Kits
Unpatched software vulnerabilities provide ransomware entry points that require no user interaction. Exploit kits are automated attack frameworks that scan for vulnerable systems and deploy appropriate exploits. These tools enable mass-scale attacks against organizations running outdated software.
Zero-day vulnerabilities represent particularly dangerous threats since no patches exist when attackers begin exploitation. Sophisticated ransomware groups sometimes purchase zero-day exploits on underground markets, gaining exclusive access to unknown vulnerabilities in popular software. Organizations have no defense until vendors discover the vulnerability and release patches.
Legacy systems and deprecated software create permanent vulnerability exposure. Organizations running unsupported operating systems or applications cannot receive security updates, leaving known vulnerabilities permanently exploitable. Industrial control systems and specialized equipment often run outdated software by necessity, creating significant risks.
Drive-By Downloads and Malvertising
Drive-by downloads infect systems when users visit compromised websites, requiring no conscious user action beyond browsing. Attackers compromise legitimate websites by exploiting content management system vulnerabilities, injecting malicious scripts into web pages. Visitors’ browsers automatically execute these scripts, downloading ransomware silently.
Malvertising distributes ransomware through online advertising networks. Attackers purchase legitimate ad space or compromise ad servers, inserting malicious code into advertisements. These infected ads appear on trusted websites, lending credibility that bypasses user suspicion. Simply viewing the advertisement can trigger infection through browser or plugin vulnerabilities.
Watering hole attacks target websites frequently visited by specific organizations or industries. Attackers research target browsing habits, then compromise relevant sites with malware. This targeted approach increases infection success rates compared to broad campaigns, since victims trust the compromised sites and visit them regularly.
Supply Chain and Third-Party Compromises
Supply chain attacks compromise trusted software or service providers to distribute ransomware to their customers. The Kaseya VSA attack in twenty-twenty-one exemplified this approach, compromising remote management software used by managed service providers. A single successful compromise infected over fifteen hundred organizations simultaneously.
Software update mechanisms provide particularly effective distribution channels. Attackers compromise vendor systems responsible for distributing software updates, inserting ransomware into otherwise legitimate updates. Organizations receive and install malicious updates through their normal update processes, bypassing security controls designed to prevent unauthorized software installation.
Trusted vendor relationships create security blind spots since organizations often provide privileged access to third-party service providers. Attackers compromise these vendors, then leverage existing access credentials to deploy ransomware across customer networks. The trust relationship eliminates many security barriers that would block direct attacks.
Ransomware Prevention Strategies: Building Comprehensive Defenses
Effective ransomware prevention requires layered defenses addressing technical vulnerabilities, process weaknesses, and human factors. No single solution provides complete protection, but comprehensive strategies significantly reduce infection risks and limit potential damages.

Employee Training and Security Awareness
Human factors contribute to most successful ransomware infections, making security awareness training essential. Employees must understand phishing tactics, recognize suspicious communications, and follow proper reporting procedures when encountering potential threats. Regular training reinforces good security habits and keeps awareness high.
Simulated phishing exercises provide practical experience recognizing threats in safe environments. Organizations send fake phishing emails to employees, tracking who clicks links or opens attachments. Results identify individuals requiring additional training and measure overall organizational susceptibility to social engineering attacks.
Security awareness programs should cover current threat tactics, real-world examples relevant to the organization, and clear reporting procedures. Training works best when delivered regularly in short sessions rather than annual marathon presentations. Micro-learning modules, security newsletters, and timely alerts about active campaigns maintain engagement.
Creating security-conscious culture requires leadership support and positive reinforcement. Organizations should celebrate employees who report suspicious emails rather than criticizing those who occasionally fall for sophisticated phishing. Fear of punishment discourages reporting, leaving threats unaddressed and compromising remaining hidden longer.
Technical Security Controls
Email security solutions provide critical frontline defenses against phishing-based ransomware distribution. Advanced filters analyze email content, attachments, and sender information to identify threats before reaching user inboxes. Sandboxing executes suspicious attachments in isolated environments, detecting malicious behavior before users interact with files.
Endpoint protection platforms offer next-generation antivirus capabilities that detect ransomware through behavioral analysis rather than relying solely on known malware signatures. These solutions monitor file system activity, process execution, and network communications to identify suspicious patterns consistent with ransomware behavior.
Application whitelisting prevents unauthorized software execution by allowing only approved programs to run. This approach proves particularly effective against ransomware since the malware cannot execute without appearing on the whitelist. Implementation requires careful planning to identify legitimate applications, but provides robust protection once deployed.
Network segmentation limits ransomware spread by dividing networks into isolated zones with controlled communication pathways. Successful infection of one segment cannot automatically spread throughout the entire network. Critical systems receive additional isolation, ensuring ransomware cannot reach most valuable assets even during successful intrusions.
Essential Technical Controls
- Email security with advanced threat detection and sandboxing
- Next-generation endpoint protection with behavioral analysis
- Application whitelisting preventing unauthorized software execution
- Network segmentation isolating critical systems and data
- Web filtering blocking access to malicious websites
- Multi-factor authentication on all remote access and privileged accounts
- Automated patch management ensuring timely security updates
- Firewall and intrusion prevention systems monitoring network traffic
- Data loss prevention detecting unauthorized data exfiltration
- Privileged access management controlling administrative credentials

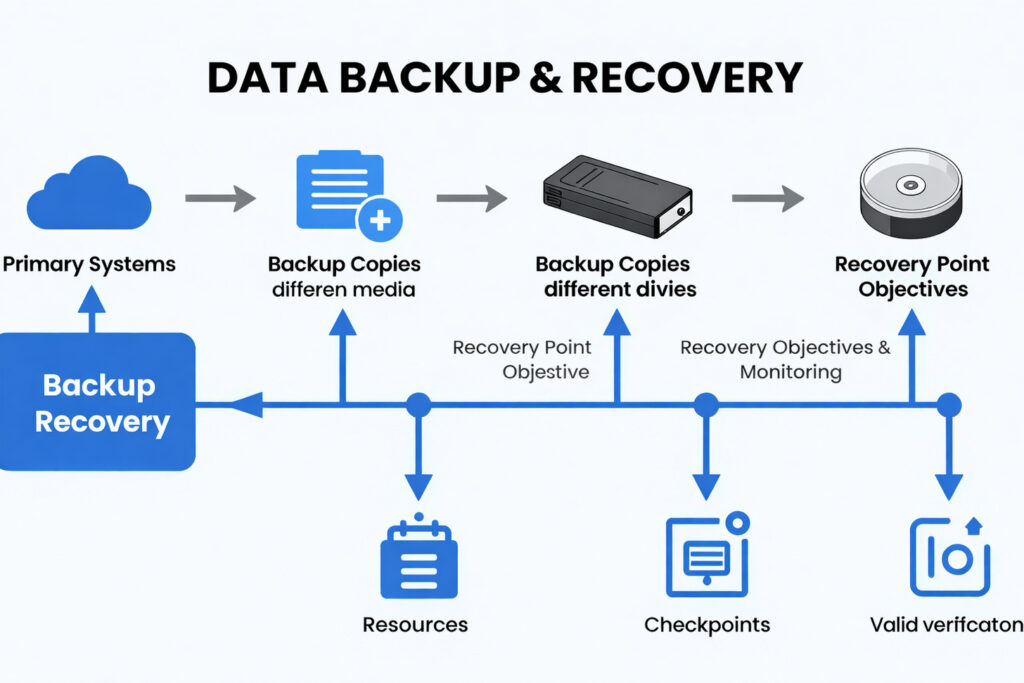
Backup and Recovery Planning
Comprehensive backup strategies enable organizations to recover from ransomware attacks without paying ransoms. The three-two-one backup rule provides a proven framework: maintain three copies of data on two different media types with one copy stored offsite. This approach ensures data availability even when primary systems and local backups face encryption.
Backup immutability prevents ransomware from encrypting or deleting backup files. Immutable backups cannot be modified or deleted for a specified retention period, ensuring recovery options remain available even if attackers gain administrative access. Cloud storage with object locking, write-once-read-many storage systems, and air-gapped backups all provide immutability.
Regular backup testing verifies that recovery procedures work correctly before emergencies occur. Organizations should periodically restore systems from backups, measuring recovery time and identifying potential issues. Testing reveals corrupted backups, missing data, or procedural gaps that would prevent successful recovery during actual ransomware incidents.
Recovery time objectives and recovery point objectives guide backup frequency and retention. Organizations must determine maximum acceptable downtime and data loss, then configure backup systems accordingly. Critical systems might require hourly backups with minutes-long recovery objectives, while less critical data accepts daily backups and longer restoration times.
Access Control and Privilege Management
Least privilege principles limit user permissions to minimum requirements for job functions. When ransomware compromises user accounts, the infection scope matches that user’s permissions. Strictly limited privileges prevent ransomware from accessing sensitive data, encrypting network shares, or spreading between systems.
Multi-factor authentication provides crucial protection for remote access, administrative accounts, and sensitive systems. Even if attackers obtain passwords through phishing or credential theft, MFA prevents unauthorized access. Time-based one-time passwords, biometric authentication, or hardware security keys all provide second-factor protection.
Privileged access management systems control and monitor administrative credentials. These solutions rotate passwords automatically, provide session recording for auditing, and require approval workflows for sensitive actions. PAM prevents credential theft from providing permanent administrative access and creates accountability for privileged activities.
Just-in-time access provides elevated privileges only when needed for specific tasks, automatically revoking access after completion. This approach minimizes the window during which compromised accounts possess dangerous permissions. Even if ransomware infects an account, it cannot leverage administrative privileges unless specifically granted for active legitimate tasks.
Patch Management
Implement automated systems deploying security updates within seventy-two hours of release. Prioritize critical patches for internet-facing systems and known exploited vulnerabilities. Maintain asset inventories ensuring all systems receive updates.
Disable Macros
Configure Microsoft Office to disable macros by default, requiring explicit user approval for execution. Implement policies preventing macro execution from internet-sourced documents. Consider alternatives eliminating macro requirements entirely.
Secure RDP
Never expose RDP directly to the internet. Require VPN access before RDP connections, implement multi-factor authentication, enforce strong password policies, and monitor for brute force attempts. Consider replacing RDP with zero-trust access solutions.
Incident Response Preparation
Incident response plans document procedures for detecting, containing, and recovering from ransomware attacks. Plans should identify response team members, define communication protocols, establish decision-making authority, and outline technical recovery steps. Regular drills test plan effectiveness and familiarize team members with their responsibilities.
Ransomware playbooks provide detailed technical procedures for common scenarios. These documents guide responders through initial triage, evidence preservation, system isolation, malware analysis, and recovery execution. Playbooks reduce response time by eliminating uncertainty about proper procedures during high-pressure incidents.
Legal and regulatory considerations require early planning. Organizations should identify notification requirements, evidence preservation obligations, and reporting deadlines before incidents occur. Relationships with law enforcement, legal counsel, cybersecurity insurers, and incident response firms enable rapid engagement when needed.
Cyber insurance provides financial protection against ransomware costs including ransom payments, recovery expenses, legal fees, and business interruption losses. Policies vary significantly in coverage limits, exclusions, and requirements. Organizations should carefully review policies, understand coverage gaps, and maintain compliance with policy requirements to ensure coverage remains valid.
Ransomware Detection and Response: Minimizing Damage
Early ransomware detection significantly limits attack impact by enabling rapid response before widespread encryption occurs. Organizations implementing effective detection capabilities can interrupt attacks during initial stages, preventing catastrophic data loss and operational disruption.

Behavioral Detection Techniques
Modern detection systems analyze system behavior rather than relying exclusively on known malware signatures. Ransomware exhibits characteristic behavioral patterns during execution that differentiate it from legitimate software. Monitoring these behaviors enables detection of new ransomware variants that signature-based antivirus cannot recognize.
File system monitoring tracks abnormal patterns in file operations. Ransomware typically reads, encrypts, and rewrites numerous files rapidly. Detection systems establish baselines for normal file activity, then alert when unusual mass file modifications occur. Sudden spikes in file writes, especially affecting many different file types simultaneously, indicate potential ransomware activity.
Process behavior analysis examines how applications interact with systems. Ransomware often deletes shadow copies, modifies registry settings, creates persistence mechanisms, and communicates with external servers. Security tools monitoring for these specific behaviors can identify ransomware during early execution stages before encryption begins.
Network traffic analysis detects ransomware communication with command and control servers. Unusual outbound connections, especially to known malicious IP addresses or newly registered domains, warrant investigation. Some ransomware variants beacon regularly to attackers, creating traffic patterns that network monitoring tools can identify.
Deception Technology
Honeypot files and decoy systems function as early warning sensors distributed throughout networks. These attractive fake targets appear valuable to attackers but serve no legitimate business purpose. Any access attempts automatically trigger alerts, detecting threats before they reach actual production data.
Canary files are documents placed strategically in file shares and folders that normal users never access. Ransomware scanning for files to encrypt will attempt to modify these canaries, immediately revealing its presence. Organizations can quarantine affected systems before ransomware progresses to encrypting legitimate data.
Deception credentials are fake usernames and passwords stored where malware might discover them. When ransomware attempts authentication using these credentials, security teams receive immediate notification. The technique not only detects ransomware but also identifies how attackers move through networks.
| Detection Method | What It Monitors | Detection Speed | False Positive Risk | Implementation Complexity |
| Signature-Based AV | Known malware patterns and hashes | Immediate | Low | Simple |
| Behavioral Analysis | Process actions and file operations | Minutes | Medium | Moderate |
| File System Monitoring | Mass file modifications and encryption | Seconds to minutes | Low to medium | Moderate |
| Network Traffic Analysis | Unusual connections and data transfers | Minutes to hours | Medium | Complex |
| Deception Technology | Access to honeypot files and systems | Immediate upon access | Very low | Moderate |
| User Behavior Analytics | Abnormal user account activities | Minutes to hours | Medium to high | Complex |
Immediate Response Actions
The initial minutes following ransomware detection determine ultimate attack impact. Rapid, decisive action can prevent isolated infections from spreading network-wide. Response teams must execute well-rehearsed procedures immediately upon threat identification.
System isolation represents the most critical immediate action. Infected devices must disconnect from networks to prevent ransomware propagation. Physical network cable removal provides the most reliable isolation method. Disabling wireless connections and VPN links follows. Aggressive isolation accepts short-term productivity loss to prevent organization-wide encryption.
Evidence preservation begins immediately for potential forensic analysis and insurance claims. Response teams should image affected systems before remediation, capture network traffic logs, and preserve ransom notes. This evidence helps identify ransomware variants, understand attack vectors, and support law enforcement investigations.
Communication protocols activate to notify stakeholders appropriately. IT leadership, executive management, legal counsel, and cybersecurity insurance providers require prompt notification. External communications must coordinate carefully to prevent premature disclosure creating additional business harm while meeting legal notification obligations.
Containment and Eradication
Containment focuses on preventing attack expansion beyond initially infected systems. Network segmentation proves crucial during this phase, as properly segmented networks naturally contain ransomware spread. Response teams identify all compromised systems through forensic analysis and log review, ensuring complete threat elimination.
Credential rotation becomes essential since ransomware often spreads using stolen credentials. Organizations should force password resets for affected users, revoke compromised service account credentials, and rotate privileged access credentials organization-wide. This action prevents attackers from maintaining access through credential theft.
Malware removal requires thorough cleaning to ensure complete eradication. Simply deleting ransomware executables proves insufficient as persistence mechanisms may reinstall malware. Best practice involves wiping and rebuilding affected systems from clean backups or fresh installations rather than attempting in-place cleaning.
Vulnerability remediation addresses the weaknesses attackers exploited initially. Patching exposed vulnerabilities, closing security gaps, and implementing additional controls prevent reinfection through identical attack vectors. This phase transforms reactive response into proactive security improvement.
Critical Response Timeline
First 15 minutes: Isolate infected systems, preserve evidence, activate incident response team
First hour: Identify ransomware variant, assess scope, notify stakeholders, prevent spread
First 24 hours: Complete containment, begin recovery planning, coordinate with external resources
First week: System restoration, security improvements, root cause analysis
Ongoing: Monitoring for reinfection, long-term remediation, lessons learned implementation
Ransomware Recovery Options: Restoring Operations
Organizations facing ransomware encryption must evaluate recovery options carefully, weighing costs, timeframes, and success probabilities. The decision matrix involves technical feasibility, business impact, legal considerations, and ethical questions about funding criminal enterprises.
Recovery from Backups
Backup restoration represents the preferred recovery method, enabling data recovery without funding criminals. Organizations with comprehensive backup strategies can restore encrypted files from clean copies, resuming operations without paying ransoms. This approach requires significant time investment but eliminates ransom payment costs and ethical concerns.
Recovery success depends on backup quality, currency, and accessibility. Backups must be recent enough that data loss remains acceptable, complete enough to restore all critical systems, and secure enough that ransomware did not encrypt or delete them. Organizations discovering corrupted, outdated, or encrypted backups face difficult recovery challenges.
Testing restored systems before production deployment prevents reinfection. Attackers sometimes maintain persistent access even after apparent ransomware removal. Thoroughly scanning restored systems, rotating all credentials, and implementing additional monitoring ensures clean recovery without immediate reinfection.
Decryption Tools and Free Decryptors
Security researchers occasionally develop free decryption tools for specific ransomware variants. These tools exploit implementation flaws in ransomware encryption, leverage leaked decryption keys, or utilize weaknesses in cryptographic implementations. Organizations should investigate decryptor availability before considering ransom payment.
The No More Ransom Project, a collaboration between law enforcement and cybersecurity companies, provides free decryption tools for numerous ransomware families. The initiative aims to help victims recover data without paying ransoms while undermining ransomware profitability. Before paying any ransom, organizations should check whether applicable decryptors exist.
Decryptor effectiveness varies based on ransomware variant and attack specifics. Some tools decrypt files completely and reliably, while others only partially recover data or work under specific conditions. Organizations should test decryptors on sample encrypted files before attempting full recovery to verify compatibility and effectiveness.
Ransom Payment Considerations
Paying ransoms remains controversial with valid arguments on multiple sides. Law enforcement agencies generally advise against payment, citing that funding encourages additional attacks and provides no guarantee of data recovery. However, organizations facing business-threatening data loss sometimes view payment as their only viable option.
Payment success rates vary by ransomware group. Some operations maintain professional reputations, reliably providing working decryption keys after payment. Others provide non-functional decryptors, demand additional payments, or simply disappear after initial payment. Research suggests approximately eighty percent of paying victims receive decryption tools, though functionality varies.
Legal and regulatory considerations affect ransom payment decisions. Some jurisdictions prohibit payments to sanctioned entities or terrorist organizations. Compliance obligations may require reporting incidents before payment, and insurance policies often include specific notification requirements. Organizations must navigate these legal complexities carefully.
Financial considerations extend beyond the ransom amount itself. Organizations must acquire cryptocurrency, often requiring account creation at exchanges and navigating unfamiliar payment processes. Additional costs include incident response, system recovery, business interruption, regulatory fines, and reputational damage regardless of payment decisions.
Arguments Against Paying Ransom
- Funds criminal operations and encourages future attacks
- No guarantee attackers will provide working decryption keys
- May violate sanctions or legal prohibitions
- Marks organization as willing to pay, inviting repeat targeting
- Decryption tools often work slowly or incompletely
- Does not address root vulnerabilities that enabled attack
- Reputational damage from publicly disclosed payments
Factors Favoring Payment
- May be faster than backup restoration for critical systems
- Prevents data publication in double extortion scenarios
- Could cost less than extended business interruption
- Some ransomware groups have reliable track records
- No viable alternative when backups are unavailable or inadequate
- May satisfy insurance policy requirements
- Can prevent complete business failure in extreme cases
Business Continuity and Disaster Recovery
Comprehensive business continuity plans enable organizations to maintain critical operations during ransomware recovery. These plans identify essential business functions, document alternative procedures for manual operations, and establish priorities for system restoration. Well-prepared organizations can continue serving customers even with major systems offline.
Disaster recovery procedures provide detailed technical instructions for rebuilding infrastructure after catastrophic failures. Documentation should cover system architecture, configuration details, installation procedures, and validation testing. Current documentation proves invaluable during recovery when normal reference materials might be inaccessible.
Recovery time objectives guide restoration prioritization. Organizations must restore the most critical systems first, accepting that complete recovery might require days or weeks. Clear priorities prevent wasted effort rebuilding non-essential systems while critical operations remain offline.
Communication strategies maintain stakeholder confidence during recovery. Customers, partners, and employees require regular updates about restoration progress and expected timelines. Transparent communication manages expectations and demonstrates organizational competence despite the security incident.
Future Ransomware Trends and Emerging Threats
The ransomware threat landscape continues evolving as attackers develop new techniques and organizations improve defenses. Understanding emerging trends enables proactive security improvements rather than reactive responses to realized threats.
Artificial Intelligence in Ransomware Attacks

Cloud and SaaS Targeting

Internet of Things and Operational Technology

Triple Extortion
Attackers add distributed denial of service attacks to existing encryption and data theft threats. Victims face operational disruption even before deciding about ransom payment, creating additional pressure for rapid payment to restore services.
Supply Chain Focus
Targeting managed service providers and software vendors enables simultaneous compromise of numerous organizations. Single successful attacks cascade across entire customer bases, multiplying impact and ransom potential exponentially.
Ransomware Cartels
Criminal groups form alliances sharing tools, infrastructure, and intelligence. These collaborations increase operational sophistication while distributing risk. Cartel structures make attribution difficult and prosecution challenging.
Regulatory and Insurance Evolution
Governments worldwide implement new regulations addressing ransomware threats. Mandatory incident reporting, ransom payment disclosure requirements, and cybersecurity standards aim to improve organizational defenses while providing authorities better threat visibility. Organizations must navigate evolving compliance landscapes alongside technical security challenges.
Cyber insurance markets adapt to sustained ransomware losses. Insurers tighten underwriting requirements, mandate specific security controls, and increase premiums significantly. Some insurers exclude ransomware coverage entirely or cap payouts substantially. Organizations can no longer rely on insurance as primary ransomware protection.
Law enforcement capabilities improve through international cooperation and specialized units. Recent operations successfully disrupted major ransomware groups, seized criminal infrastructure, and recovered ransom payments. However, the fundamental economics favoring attackers ensure ransomware remains profitable despite enforcement improvements.
Conclusion: Building Resilience Against Ransomware
Ransomware continues to be one of the most critical cybersecurity challenges for modern organizations, demanding a proactive and strategic defense approach. At Atrity Info Solutions, we recognize that combating ransomware is not just about deploying security tools, but about building a resilient security ecosystem that integrates technology, processes, and people.
Our approach focuses on delivering layered security solutions, including advanced threat detection, endpoint protection, firewall management, and secure backup strategies. By combining these with continuous monitoring and rapid incident response capabilities, we help organizations minimize risk exposure and ensure operational continuity even in the face of evolving cyber threats.
We also emphasize the importance of cybersecurity awareness and training, enabling employees to act as the first line of defense against ransomware attacks. Through regular assessments, vulnerability management, and security best practices, Atrity ensures that clients stay ahead of emerging attack techniques.
In an ever-changing threat landscape, static defenses are no longer sufficient. Atrity is committed to continuous innovation and adaptive security strategies that evolve alongside cyber risks. While eliminating ransomware threats entirely may not be feasible, our goal is to significantly reduce risk, enhance preparedness, and empower organizations to operate with confidence and resilience.
 Read More
Read More