Do you have complete visibility into your IT environment? For many organizations, the honest answer is no. Today’s security teams are responsible for managing thousands of digital assets — including cloud workloads, applications, endpoints, user accounts, and network devices. Without full visibility, these assets can quickly become blind spots, leading to misconfigurations, compliance gaps, and exploitable vulnerabilities. In 2024, the ransomware attack on Change Healthcare highlighted the devastating consequences of weak asset oversight. The breach reportedly stemmed from a single compromised user account that lacked multi-factor authentication (MFA). The result? Disruption to healthcare services nationwide and the exposure of data affecting approximately 190 million individuals.This incident reinforces a critical reality: cybersecurity asset management is not just a technical best practice—it is a business necessity. Organizations must maintain continuous visibility, control, and accountability over every asset within their digital ecosystem.
In this article, we’ll explore why cybersecurity asset management is vital, how it functions, and practical steps your organization can take to strengthen its security posture.
What is Cybersecurity Asset Management?
Cybersecurity asset management (CSAM) is the continuous process of discovering, inventorying, monitoring, and securing all digital assets within your organization’s IT environment. It provides real-time visibility into your entire digital footprint, helping identify vulnerabilities, enforce security policies, and maintain compliance.
Unlike traditional IT asset management (ITAM), which focuses primarily on tracking what an organization owns for inventory and cost management purposes, cybersecurity asset management emphasizes protecting those assets from threats. It’s about understanding not just what exists on your network, but how those assets are secured and what risks they might pose.
Effective cybersecurity asset management answers critical questions:
- What devices, applications, and accounts exist in our environment?
- Are these assets properly configured and protected?
- Which assets contain sensitive data or provide access to critical systems?
- Are there unauthorized or unmanaged assets on our network?
- Do all assets comply with our security policies and regulatory requirements?
By maintaining a comprehensive inventory of all digital assets and continuously monitoring their security status, organizations can significantly reduce their attack surface and respond more effectively to threats.
What Does Cybersecurity Asset Management Protect?
Cybersecurity asset management secures everything in your IT environment—because any overlooked asset can become a target. A comprehensive approach covers:
- Hardware – Servers, laptops, mobile devices, routers, IoT devices
- Software – Applications, operating systems, databases
- Cloud resources – Virtual machines, containers, SaaS applications
- Network components – Firewalls, switches, load balancers
- Data assets – Customer records, intellectual property, documentation
- User identities – Employee credentials, privileged access accounts
Why is Cybersecurity Asset Management Critical for IT Businesses?
In today’s complex digital landscape, cybersecurity asset management isn’t just a technical necessity—it’s a business imperative. Here’s why it matters for your IT business:
1. Reduces Security Risks and Vulnerabilities
You can’t protect what you don’t know exists. Comprehensive asset visibility allows you to identify and remediate vulnerabilities before attackers can exploit them. By maintaining an accurate inventory of all assets, you can implement appropriate security controls, ensure proper configuration, and apply timely patches.
According to industry research, organizations with mature asset management programs experience 23% fewer security incidents than those without such capabilities. This directly translates to reduced business disruption and financial losses.
2. Ensures Regulatory Compliance
Many regulatory frameworks require asset management as a core component of compliance. Standards such as ISO 27001, the NIST Cybersecurity Framework, HIPAA, and GDPR emphasize the need for maintaining asset inventories and controls. Effective cybersecurity asset management enables organizations to:
- Maintain accurate records of all systems processing sensitive data
- Demonstrate appropriate security controls for auditors
- Quickly respond to compliance inquiries with accurate information
- Avoid costly penalties and reputational damage from non-compliance
3. Improves Operational Efficiency
Beyond security benefits, effective asset management streamlines IT operations. When you know exactly what’s in your environment, you can:
- Eliminate redundant systems and consolidate resources
- Optimize licensing and reduce software costs
- Automate routine security tasks like vulnerability scanning
- Accelerate incident response with accurate asset information
This operational efficiency translates directly to cost savings and improved productivity for your IT team.
4. Enhances Incident Response Capabilities
When security incidents occur, time is critical. Comprehensive asset management provides the context security teams need to quickly identify affected systems, contain threats, and remediate vulnerabilities. This significantly reduces mean time to detect (MTTD) and mean time to respond (MTTR), minimizing the impact of security breaches.
5. Supports Strategic Decision-Making
With complete visibility into your IT environment, you can make more informed decisions about technology investments, security priorities, and resource allocation. Asset management data helps you:
- Identify security gaps requiring additional controls
- Prioritize investments based on asset criticality and risk
- Plan technology refreshes and migrations more effectively
- Demonstrate security ROI to executive leadership
Key Components of an Effective Cybersecurity Asset Management Strategy
Building a robust cybersecurity asset management program requires several essential components working together:
1. Comprehensive Discovery
Continuous, automated discovery of all assets across your environment, including on-premises, cloud, and remote endpoints. This should identify both managed and unmanaged (shadow IT) assets.
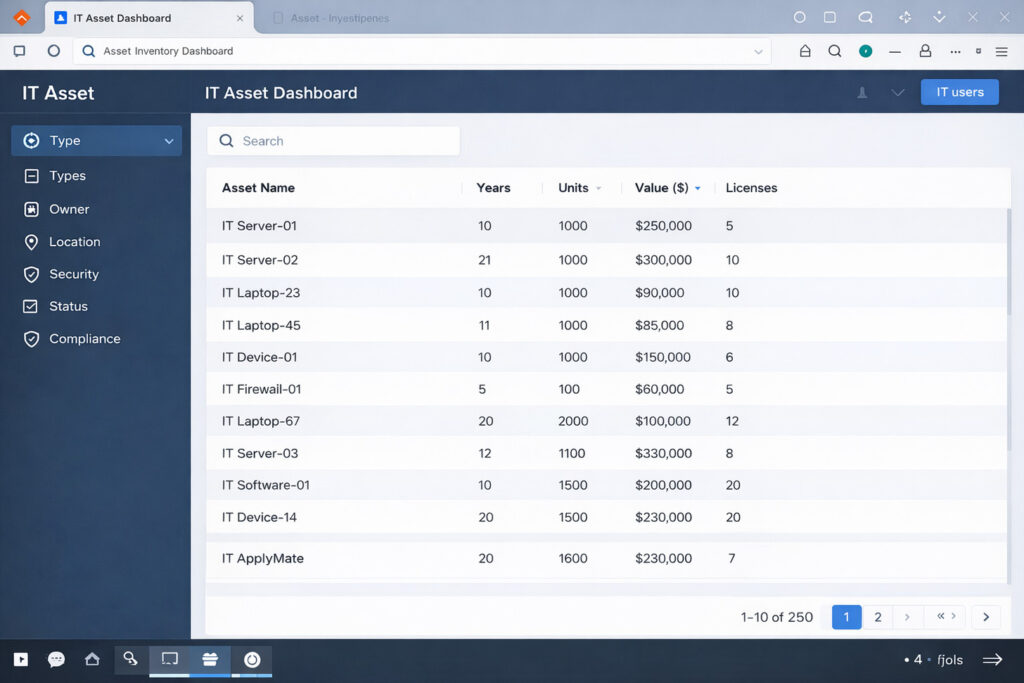
2. Detailed Inventory
A centralized repository of asset information, including hardware specifications, installed software, configurations, ownership, and security status. This inventory should be automatically updated as assets change.
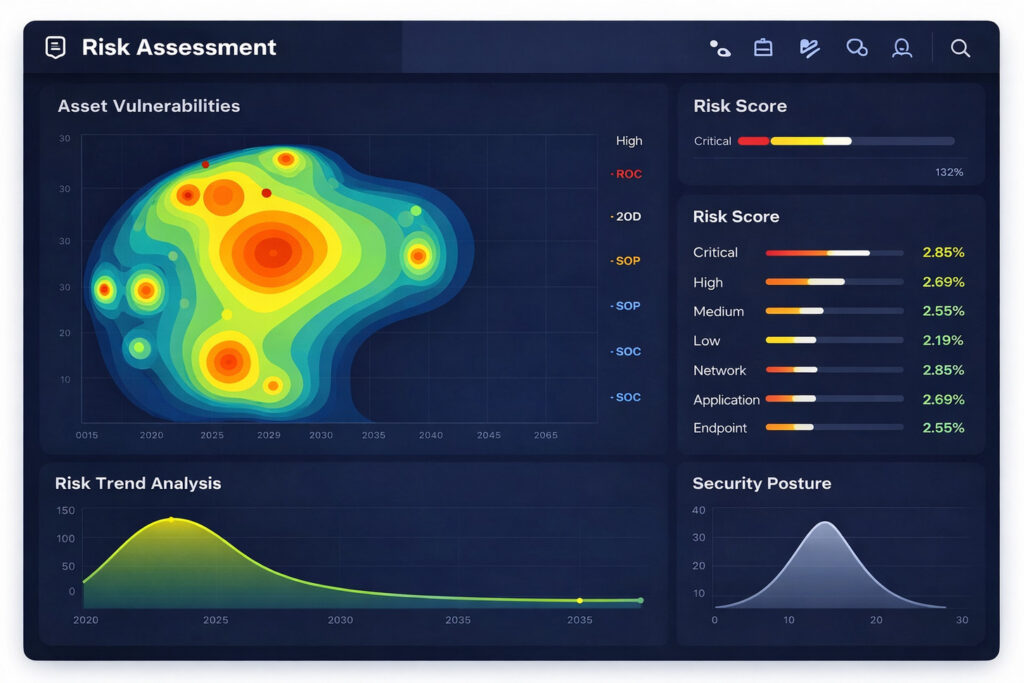
3. Risk Assessment
Continuous evaluation of assets for vulnerabilities, misconfigurations, and compliance issues. This includes prioritizing risks based on asset criticality and potential impact to the business.
4. Security Controls
Implementation of appropriate security measures for each asset type, including access controls, encryption, endpoint protection, and network segmentation. These controls should be continuously monitored for effectiveness.
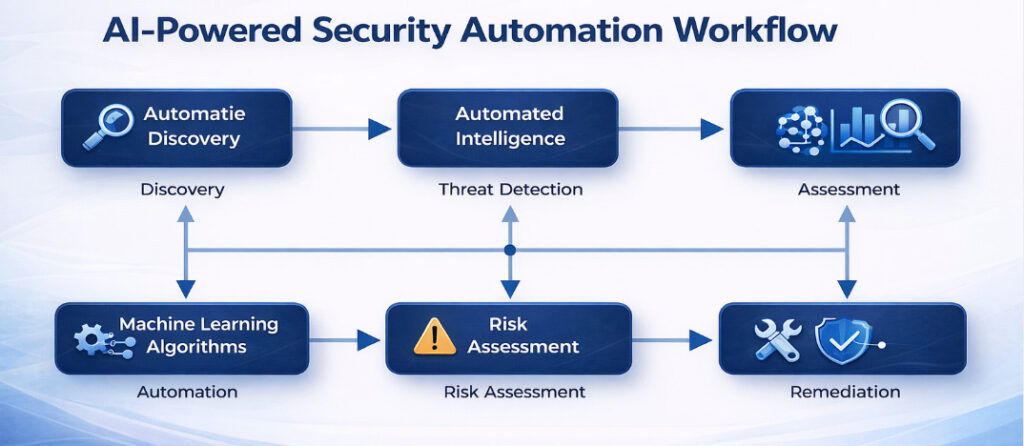
5. Automation & Integration
Integration with existing security tools like vulnerability scanners, SIEM systems, and endpoint protection platforms. Automation of routine tasks like patch management and compliance checking reduces manual effort and improves accuracy.
6. Reporting & Analytics
Comprehensive reporting capabilities that provide actionable insights into your security posture, compliance status, and risk trends. These reports should be tailored for different stakeholders, from technical teams to executive leadership.
Common Challenges in Implementing Cybersecurity Asset Management
While the benefits of cybersecurity asset management are clear, implementation can present several challenges:
Technical Challenges
- Environment complexity – Modern IT environments span on-premises, cloud, and hybrid infrastructures, making comprehensive discovery difficult
- Shadow IT – Unauthorized assets and applications that bypass normal procurement processes
- Ephemeral assets – Short-lived cloud instances and containers that appear and disappear rapidly
- Integration issues – Connecting disparate security tools and data sources into a unified view
Organizational Challenges
- Resource constraints – Limited budget and staffing for security initiatives
- Skill gaps – Lack of expertise in modern asset management approaches
- Organizational silos – Separation between IT, security, and compliance teams
- Change resistance – to adopt new processes and technologies
Overcoming these challenges requires a strategic approach that combines the right technology, processes, and people. Many organizations find that partnering with cybersecurity experts can accelerate implementation and maximize the value of their asset management program.
Best Practices for Effective Cybersecurity Asset Management
To maximize the value of your cybersecurity asset management program, consider these proven best practices:
1. Start with Clear Objectives
Define specific goals for your asset management program, such as improving visibility, reducing vulnerabilities, or enhancing compliance. These objectives will guide your implementation strategy and help measure success.
2. Implement Continuous Discovery
Deploy automated discovery tools that continuously scan your environment for new assets. This should include network scanning, agent-based discovery, and integration with cloud platforms to ensure complete coverage.
Continuous discovery is essential to maintaining an accurate and up-to-date asset inventory. In modern environments—where cloud resources, remote devices, and virtual systems are constantly changing—periodic scans are no longer sufficient. Organizations must adopt automated discovery mechanisms that provide real-time visibility into all assets.
Key Components of Continuous Discovery
1. Network-Based Scanning
Deploy automated network scans to detect devices, open ports, services, and unauthorized systems connected to the environment.
2. Agent-Based Discovery
Install lightweight agents on endpoints and servers to collect detailed system information, configuration data, and security posture metrics.
3. Cloud Platform Integration
Integrate directly with cloud providers to identify virtual machines, containers, storage resources, and serverless workloads as they are created or modified.
4. API Integrations with Security Tools
Connect with vulnerability scanners, endpoint security platforms, and identity systems to enrich asset records and eliminate visibility gaps.
5. Real-Time Alerts for New or Rogue Assets
Configure alerts for newly discovered or unmanaged assets to ensure rapid validation and onboarding into security controls.
Benefits of Continuous Discovery
Eliminates shadow IT and unmanaged devices
Maintains a real-time, accurate asset inventory
Reduces exposure from unknown systems
Strengthens overall security visibility
By implementing continuous discovery, organizations ensure that every asset—on-premises, remote, or cloud-based—is accounted for, monitored, and protected within their cybersecurity asset management program.
3. Prioritize Based on Risk
Not all assets pose the same level of risk. Develop a risk-based approach that prioritizes critical assets—those that contain sensitive data, support essential business functions, or have direct internet exposure.
Prioritize Based on Risk in Cybersecurity Asset Management
A risk-based approach to cybersecurity asset management ensures that security efforts focus first on the systems that matter most to the organization.
Identify and prioritize critical assets—those that:
Store or process sensitive data (e.g., customer, financial, or intellectual property)
Support essential business operations
Have direct internet exposure or external access
Serve as authentication, identity, or infrastructure control points
Connect to high-value systems or segmented networks
How to Implement a Risk-Based Approach
1. Classify Assets by Criticality
Assign risk tiers based on business impact, data sensitivity, and operational importance.
2. Incorporate Vulnerability Context
Combine asset value with vulnerability severity to determine true risk—not just CVSS scores.
3. Consider Exposure and Threat Likelihood
Prioritize externally facing systems and assets frequently targeted by threat actors.
4. Align with Business Impact Analysis (BIA)
Work with business stakeholders to understand which systems are essential for continuity.
5. Continuously Reassess Risk
Risk levels change as new vulnerabilities emerge, systems are modified, or business priorities shift.
Benefits of Risk-Based Prioritization
Faster remediation of high-impact threats
More efficient allocation of security resources
Reduced likelihood of business disruption
Stronger overall security posture
By prioritizing assets based on real business and security risk, organizations can focus remediation efforts where they will have the greatest impact—protecting what matters most.
4. Automate Where Possible
Leverage automation to reduce manual effort and improve accuracy. This includes automated discovery, vulnerability scanning, compliance checking, and remediation workflows.
Key Areas to Automate
1. Automated Asset Discovery
Continuously scan networks, cloud environments, and remote endpoints to detect new, unmanaged, or rogue assets as soon as they appear.
2. Vulnerability Assessment Integration
Automatically correlate assets with vulnerability data to identify exposed systems and prioritize remediation based on asset criticality.
3. Compliance Monitoring
Implement automated compliance checks to verify configuration standards, patch levels, and policy adherence across all assets.
4. Remediation Workflows
Trigger automated patch deployment, configuration updates, or ticket creation when vulnerabilities or policy violations are detected.
5. Asset Lifecycle Management
Automate onboarding, classification, tagging, and decommissioning processes to maintain a clean and up-to-date inventory.
Benefits of Automation
Improved Accuracy – Reduce human error and outdated records
Real-Time Visibility – Maintain a live view of your environment
Faster Risk Reduction – Shorten detection and remediation timelines
Operational Efficiency – Free security teams to focus on strategic tasks
5. Integrate with Existing Security Tools
Connect your asset management solution with other security technologies like vulnerability scanners, endpoint protection platforms, and SIEM systems. This integration provides context for security events and enables more effective response.
Why Integration Matters
Connecting asset management with your broader security stack creates a centralized, contextual view of your environment. Instead of isolated alerts, security teams gain visibility into:
Asset ownership and business criticality
Operating systems and software versions
Exposure level and network location
Known vulnerabilities and patch status
This context allows teams to prioritize risks accurately and respond based on real business impact.
Clear Related Blogs
Explore these informative resources to deepen your understanding of cybersecurity asset management and related topics:
Cybersecurity Compliance Frameworks: A Complete Guide
Explore how major compliance frameworks like ISO 27001, NIST, and GDPR approach asset management requirements and how to align your program with these standards.
Cloud Asset Management: Securing Your Digital Transformation
Learn specific strategies for managing and securing cloud-based assets across multi-cloud environments, including IaaS, PaaS, and SaaS resources.
How AI is Transforming Cybersecurity Asset Management
Discover how artificial intelligence and machine learning are revolutionizing asset discovery, vulnerability detection, and risk prioritization in modern security programs.
Taking the Next Step in Your Cybersecurity Journey
Cybersecurity asset management is no longer optional for modern IT businesses — it is a strategic necessity. Without complete visibility into your digital environment, organizations remain vulnerable to hidden risks, compliance gaps, and operational disruptions.
At Atrity, we help businesses move beyond reactive security and adopt a proactive, intelligence-driven approach to asset management. By implementing a comprehensive cybersecurity asset management framework, you can:
- Gain complete visibility across cloud, on-premise, and hybrid environments
- Reduce security risks by identifying unmanaged and misconfigured assets
- Strengthen regulatory compliance and audit readiness
- Improve operational efficiency through automation and centralized control
- Make data-driven strategic security decisions
- The key to success lies in defining clear objectives, enabling continuous asset discovery, prioritizing remediation based on real risk impact, and leveraging automation to scale securely.
With the right strategy and expert guidance, cybersecurity asset management becomes a competitive advantage — not just a security control.
Ready to strengthen your security posture? The experts at Atrity are here to design and implement a tailored cybersecurity asset management strategy that aligns with your business goals and industry requirements.
 Read More
Read More