What Is Cyber Security?
Just as physical security protects people and property from theft or damage, cyber security protects computer
systems, back-end infrastructure, and end-user applications — along with the users of those systems and the
sensitive data they hold. Cyber security covers the policies, processes, and technologies that prevent unauthorized
access, data loss, and service disruption across an organization’s networks and systems.
Why cyber security matters for every organization
As society becomes increasingly digital, networks, computers, mobile devices, and software applications power
essential services across healthcare, finance, government, manufacturing, and more. The majority of these systems
are connected to the Internet, which increases exposure: attackers can probe networks, compromise devices, and
exploit software to reach sensitive data and critical systems. Protecting those systems is central to maintaining
business continuity, protecting customer data, and preserving public trust.
Threat actors have stronger incentives than ever to infiltrate systems for financial gain, extortion, political
motives (hacktivism), or simple vandalism. Over the past two decades, cyber attacks have targeted critical
infrastructure and businesses worldwide, causing operational outages, reputational damage, and costly data breaches.
For organizations that handle sensitive information, the consequences can include regulatory fines, customer churn,
and long-term brand harm.
Example: a mid-size healthcare provider that lost access to patient records during a ransomware attack experienced
multi-day downtime, lost revenue, and significant remediation costs — a reminder that threats to data and systems
can directly affect operations and users.
Security breaches and threats can affect nearly any system including:
- Communication — phone calls, emails, text messages, and messaging apps can be vectors for
phishing and social engineering attacks that open access to networks. - Finance — financial institutions and any organization processing credit card or banking
information are high-value targets for attackers seeking monetary gain. - Governments — public-sector systems hold citizen data and confidential records that attackers
and nation-state actors often try to access. - Transportation — connected cars, traffic control systems, and smart road infrastructure are
increasingly targeted by cyber threats that can disrupt services and safety systems. - Healthcare — electronic health records and clinical systems hold sensitive patient information;
breaches can endanger privacy and care delivery. - Education — universities and schools store research data and personal records that are
attractive to attackers seeking intellectual property or personal information.
Across these sectors, websites and web applications are commonly used as entry points by attackers
because they are exposed to the public Internet and often connected to sensitive back-end systems. Hardening
applications and the systems they access is a key line of defense in any organization’s security posture.
Whether you are a small business, a high-traffic website owner, or a large institution, preparing for and defending
against cyber security threats should be a top priority. Learn how Atrity protects your systems, data, and users by
reviewing our security solutions and services.
Principles of Cyber Security
The primary objective of cyber security is to protect data across an organization’s systems and networks. Security
professionals commonly rely on the CIA triad — Confidentiality, Integrity, and Availability — as a foundational
model to ensure data remains private, accurate, and accessible to authorized users when needed.
- Confidentiality — ensure sensitive data is accessible only to authorized people and systems by
enforcing access controls, encryption, and strict policies that limit unnecessary exposure. - Integrity — protect data and systems from unauthorized modification or corruption by attackers
or accidental changes; implement checksums, versioning, and change controls so you can detect tampering and
restore trusted states quickly. - Availability — keep systems and data available and useful for legitimate users, ensuring that
network outages, software failures, or cyber attacks do not deny service to your organization’s users and
customers.
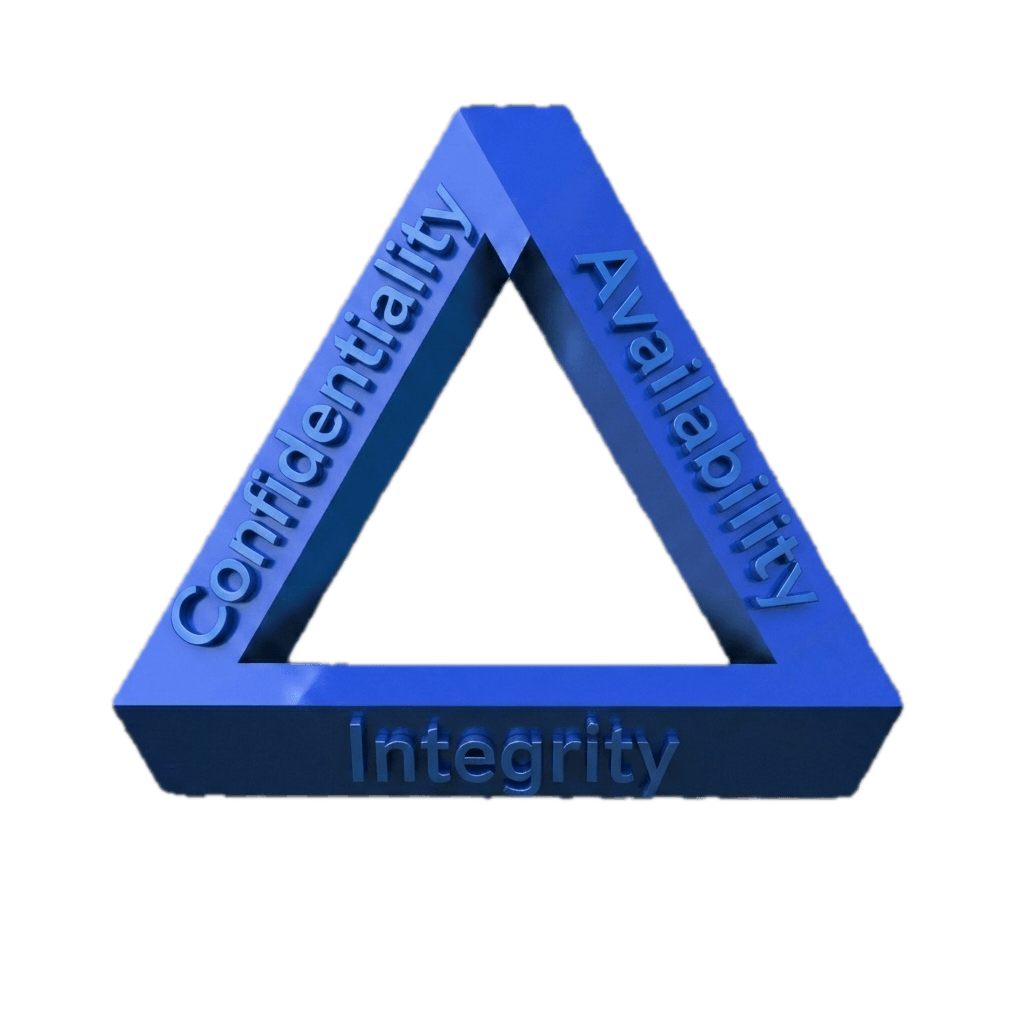
The CIA Triad defines three key principles of data security
To meet CIA objectives, organizations must secure two interdependent areas of the IT environment: application security and data security. Protecting both the software layer
and the underlying data is essential to reduce risk from cyber threats and to maintain business continuity.
Common Application Security Strategies
Application security protects user-facing applications from penetration, disruption, and abuse—whether attacks target the application
itself, the endpoints that use it, or malicious insiders. Below are high-impact strategies to strengthen application
defenses.
DDoS attacks overwhelm websites and services with fake traffic, denying access to legitimate users. A cloud-based
DDoS mitigation service diverts and scrubs malicious traffic—using DNS or BGP routing—so
your network and applications remain available. Quick checklist: enable cloud scrubbing for critical endpoints, set
rate limits, and test failover plans.
A Web Application Firewall (WAF) sits at the network edge as a reverse proxy, inspecting
HTTP/S traffic to detect and block malicious requests. A WAF leverages security policies and threat intelligence—such as IP reputation and known attack patterns—to prevent exploits
against your applications. Quick checklist: deploy WAF rules for common injection attacks, enable real-time
monitoring, and tune policies to reduce false positives.
Bots range from helpful crawlers to malicious automated agents that scan for vulnerabilities or scrape data. Bot
management combines reputation databases, device fingerprinting, behavioral analysis, and challenge mechanisms to
distinguish legitimate bots and users from malicious automation. Quick checklist: maintain a known-bot whitelist,
log unusual behavior, and use non-intrusive challenges to block bad bots while preserving user experience.
Common Data Security Strategies
Data security focuses on preventing unauthorized access to sensitive data, detecting suspicious activity, and
ensuring you can recover from incidents. The following approaches are commonly used to protect sensitive customer
data and organizational information.
Data Masking
Test and DevOps environments often contain live or realistic data and can be a source of breaches. Data masking
replaces or obfuscates sensitive fields so teams can test with realistic data while protecting customer data. Quick
checklist: mask PII in non-production environments, enforce least-privilege access, and audit masked data usage.
Vulnerability discovery identifies software and configuration weaknesses that attackers can exploit. Use
vulnerability databases and automated scans to find affected systems, assess severity, and remediate critical
issues. Quick checklist: schedule regular scans, prioritize high-risk findings, and integrate remediation into your
release pipeline.
Endpoint Security
The number of endpoints—laptops, mobile devices, and Internet of Things (IoT) devices—continues to grow, increasing
the attack surface. Endpoint security deploys agents that provide Next-Generation Antivirus (NGAV), Endpoint
Detection and Response (EDR), and real-time threat prevention to identify and block attacks on devices. Quick
checklist: enroll all endpoints in management, update agents automatically, and monitor endpoint telemetry for
suspicious behavior.
Common Cyber Threats
The cyber security landscape is complex and constantly evolving. Millions of known threat actors use documented
Tactics, Techniques, and Procedures (TTPs), and new types of attacks appear regularly. Below are some of the most
common cyber threats your organization may face, how they work, and the risk they pose to your systems and data.
| Threat | How it Works | Risk to Your Organization |
| Phishing | Attackers send deceptive emails or messages designed to trick recipients into revealing credentials, clicking malicious links, or installing malware. Phishing often uses social engineering and spoofed sender addresses to appear legitimate. | Phishing frequently serves as the initial vector for broader attacks: it can expose credentials, enable attacker access to internal systems, and lead to data breaches that compromise customer data and business information. |
| Advanced Persistent Threats (APT) | APT groups are organized attacker teams—often with significant resources—conducting long-term, targeted campaigns against a specific organization. They use reconnaissance, credential theft, lateral movement, and stealthy persistence to maintain access. | APTs can exfiltrate sensitive information, disrupt critical services, and cause sustained operational and reputational damage. They often target high-value systems and customer data over months or years. |
| Malware | Malicious software (malware) includes viruses, trojans, worms, and spyware designed to damage systems, steal data, or create backdoors. Malware can spread automatically, be delivered via email attachments, or be installed through exploited vulnerabilities. | Malware can corrupt data, disrupt operations, and provide attackers with persistent access to systems—escalating into broader incidents such as data breaches or ransomware attacks. |
| Ransomware | A form of malware that encrypts files and systems, preventing legitimate access until a ransom is paid. Ransomware often spreads via phishing, unpatched vulnerabilities, or exposed remote-access services. | Ransomware threatens availability of critical systems and data. Without reliable backups and recovery plans, organizations may face prolonged downtime, data loss, regulatory penalties, and high remediation costs. |
| Zero-day exploit | An attack exploiting a previously unknown vulnerability for which no vendor patch exists. Zero-day exploits are valuable to attackers because defenders have no prior signatures or fixes to rely on. | Zero-day exploits can allow attackers to access critical systems, bypass protections, and cause rapid, hard-to-detect breaches that compromise sensitive data and infrastructure. |
| Code injection | Attackers submit malicious code or queries (e.g., SQL Injection, Cross-Site Scripting) to an application, causing the system to execute unintended commands or expose data from back-end databases. | Code injection can lead to unauthorized data access, manipulation of databases, or full system compromise—putting customer data, intellectual property, and operational systems at risk. |
| Denial of Service (DDoS) | Attackers flood a target with massive volumes of traffic or resource requests—often via botnets—overwhelming servers and network links so legitimate users cannot access the service. | DDoS attacks cause service outages, reputational harm, and lost revenue. They can also be used as a diversion to mask other malicious activities during an incident. |
| Bots and automated attacks | Automated bots scan the Internet for vulnerabilities, brute-force credentials, scrape content, or deliver malware at scale. Bots operate continuously and can adapt to defenses to maximize impact. | Bots amplify the scale of attacks, increasing the speed and volume of attempts against applications and systems. Unchecked bot traffic can lead to brute-force compromises, data scraping, and increased load on networks and systems. |
What to look for (top 3 immediate concerns):
- Phishing — sudden credential use from new locations, unexpected emails with attachments, or
reports of suspicious messages. Immediate steps: enforce MFA, run targeted email training, and block known
malicious senders. - Ransomware — unexplained file encryption, unusual file rename patterns, or large outbound data
transfers. Immediate steps: isolate affected systems, restore from clean backups, and activate incident response
playbooks. - DDoS — sudden spikes in traffic, repeated requests from many IPs, or degraded service
performance. Immediate steps: enable DDoS mitigation, apply traffic filtering, and activate failover/VPN
protections.
These threats can lead to data breaches and loss of customer data if not detected and remediated quickly. For a
fast response, consider Atrity’s incident response and security services to contain attacks and recover systems.
Building a Cyber Security Strategy
Addressing cyber security in your organization begins with a clear, actionable strategy endorsed by senior
management and communicated across teams. A strong strategy aligns security controls to business priorities,
protects critical systems and data, and reduces the risk from cyber threats.
Use the following process as a practical roadmap to build or improve your cybersecurity program:
- Perform an inventory of computing assets — catalog applications, servers, databases, networks,
and devices; classify data by sensitivity (including customer data and financial information); and document the
business impact if each asset is compromised. This inventory is the foundation for all subsequent security
decisions. - Map compliance requirements — identify regulatory or industry standards that apply to your
organization (for example, data protection and sector-specific rules). Incorporate compliance obligations into
your asset inventory so you can prioritize systems that require additional controls or reporting. - Identify threats and assess risks — analyze the threats most relevant to your industry and
organization, evaluate vulnerabilities in your systems, and estimate likely impact. For web-facing businesses,
focus on application-level threats such as code injection and malicious bots; for organizations with large device
fleets, prioritize endpoint and IoT risk. - Prioritize risks — rank assets and risks by business value and attack likelihood, then target
high-impact, high-likelihood risks first. Use a risk matrix to guide investment in prevention, detection, and
response controls. - Assess security maturity and existing tooling — evaluate your organization’s current cyber
security capabilities and tools (firewalls, WAF, EDR, SIEM, IAM). Identify gaps in people, processes, and
technology, and determine whether to augment in-house staff with external services. - Establish a security team and governance — define roles and responsibilities, appoint executive
sponsors, and build a cross-functional team that includes IT, security, legal, and business owners. Ensure regular
reporting to leadership and integrate security into change and release processes. - Create a multi-year roadmap with milestones — plan quick wins (e.g., MFA rollout, patching
critical systems), medium-term initiatives (WAF deployment, endpoint protection), and long-term projects
(SIEM/SOAR integration, secure SDLC). Set quarterly milestones and measurable KPIs to track progress.
Quick project-plan sample (12 months):
- Months 1–2: Complete asset inventory, classification, and gap analysis.
- Months 3–4: Patch management and MFA rollout for high-risk systems; implement emergency incident response
playbook. - Months 5–8: Deploy WAF and DDoS protection for public-facing applications; enroll endpoints in EDR with
centralized monitoring. - Months 9–12: Integrate log collection into SIEM, begin threat-hunting processes, and conduct a tabletop incident
response exercise.
Technical checklist (must-haves): firewall and network segmentation, Web Application Firewall for public apps,
endpoint security (NGAV/EDR) on devices, regular vulnerability scans and remediation, IAM with least-privilege
access controls, and reliable backup and disaster recovery for critical data.
Finally, measure progress with practical KPIs — number of critical vulnerabilities remediated, mean time to detect
and respond, percentage of endpoints enrolled in protection, and results from simulated phishing tests — and iterate
your plan based on threat intelligence and business changes.
Ready to accelerate your security program? Book a security assessment with Atrity to map risks, prioritize
controls, and build a tailored timeline that protects your systems, data, and users.
7 Cyber Security Trends
The following trends are shaping cyber security strategy and technology choices today. Understanding them will help
your organization select the right security solutions, protect applications and data, and reduce exposure to
evolving cyber threats.
1. Cyber Security and Machine Learning
Legacy security relied heavily on manually written rules and human triage. Modern cybersecurity leverages machine
learning to automate detection, reduce false positives, and surface high-priority incidents faster. ML-driven
solutions help security teams scale their defenses while improving prevention and response across networks and
systems.
Examples of ML in practice:
- Next-generation antivirus (NGAV) — uses behavioral and ML models to identify malware that does
not match known signatures. - Data loss prevention (DLP) — applies ML to classify documents and
detect sensitive data exfiltration attempts. - Email protection — ML models trained on large datasets detect phishing patterns in emails and
flag suspicious messages before users interact with them.
What it means for you: prioritize ML-capable platforms for alert reduction and prioritized triage
to combat alert overload and improve behavior-based detection.
How Atrity Helps
Machine Learning
security solutions apply contextual comparative analysis to identify anomalous behavior, prioritize alerts, and
reduce noise for security teams.
2. API Security
APIs connect applications and systems and power modern services, but unsecured endpoints create a direct path to
sensitive data and backend systems. API security focuses on protecting exposed endpoints, enforcing access controls,
and preventing abuse or data leakage.
Quick mitigation: adopt schema-driven controls (OpenAPI), enforce strong authentication and rate
limiting, and monitor API traffic for anomalous patterns.
How Atrity Helps
API Security helps ensure
only legitimate traffic reaches API endpoints and detects exploits, adapting automatically to API changes.
3. Advanced Bot Protection
Bots account for a large share of web traffic and range from benign crawlers to malicious automation that scrapes
data, attempts credential stuffing, or forms the basis of DDoS botnets. Advanced bot protection uses reputation,
device fingerprinting, and behavioral analysis to distinguish good bots and users from bad bots.
Quick mitigation: maintain bot reputation lists, apply device fingerprinting, and deploy
non-intrusive challenges to block malicious automation while preserving user experience.
How Atrity Helps
Atrity’s Advanced Bot Protection analyzes traffic to identify anomalies, validate suspicious
behavior via challenges, and filter unwanted sources by IP, geography, or pattern.
4. File Security
File security and monitoring are essential for preventing data exfiltration, detecting insider misuse, and meeting
compliance requirements. Systems that log and analyze file access give security teams visibility into privileged
user behavior and suspicious transfers of sensitive information.
Quick mitigation: enable detailed file-audit logs, alert on anomalous file access or mass
downloads, and enforce encryption and access controls on sensitive repositories.
How Atrity Helps
Atrity’s File Security
continuously monitors user access to enterprise file systems and records detailed activity for auditing and
investigation.
5. Runtime Application Self-Protection (RASP)
RASP instruments applications in production to detect and block attacks in real time by understanding application
logic and monitoring runtime behavior. RASP complements static testing by protecting against runtime exploits,
including zero-day attacks and injection attempts that bypass pre-production checks.
Quick mitigation: deploy RASP alongside WAF and runtime monitoring to block suspicious requests
and gain immediate feedback for remediation.
How Atrity Helps
Atrity’s RASP integrates without code changes, monitors runtime behavior, and blocks attacks while
providing actionable insights for developers.
6. Cloud Security
As organizations move workloads to public and private clouds, securing cloud infrastructure and maintaining
consistent controls across hybrid and multi-cloud environments is critical. Cloud security includes correct
configuration, strong IAM, network isolation, and protecting APIs and services that handle sensitive data.
Quick mitigation: implement least-privilege IAM, use VPC/network isolation, continuously scan for
misconfigurations, and centralize visibility across cloud accounts.
How Atrity Helps
Atrity’s Cloud Security offers a
unified control plane for protecting applications, APIs, and databases across public, private, and multi-cloud
deployments.
7. Alert Fatigue and Prioritization
Security teams face huge volumes of alerts from SIEMs, endpoint agents, and network monitors. Without effective
prioritization, teams experience alert fatigue, leading to missed incidents and slower response times. Combining
threat intelligence, ML (UEBA), and automation (SOAR) helps reduce noise and focus attention on high-risk incidents.
Quick mitigation: tune alerts to reduce false positives, implement behavioral analytics to surface
anomalies, and automate common response playbooks to speed containment.
How Atrity Helps
Atrity’s Attack Analytics
uses AI and ML to correlate events, prioritize alerts, and integrate with SIEM platforms so security teams can focus
on real threats rather than volume.
Across these trends, the right mix of solutions—machine-learning detection, API protections, bot management, file
and endpoint protection, RASP, and cloud controls—helps organizations reduce successful attacks, lower risk to
critical infrastructure, and protect sensitive information and users. If you’d like help mapping these trends to a
practical security roadmap, Atrity’s solutions and professional services can assist with implementation and
operations.
See Additional Guides on Key Data Security Topics
Together with our content partners, we have authored in-depth guides on several topics that will help you
strengthen your security posture, protect sensitive data, and reduce exposure to cyber threats. Explore practical
resources on data protection, cloud security best practices, incident response planning, and application security
risk reduction.
Recommended reading:
- Data Security: Principles and Best Practices
- Cybersecurity: Protecting Patient Information
- Web Application & API Protection (WAAP)
- Common Cyber Security Threats and How to Respond
For hands-on help aligning these guides to your business, Atrity offers security services and assessments to
protect your systems, users, and customer data — book an assessment to get a customized plan.
 Read More
Read More