Comprehensive Privileged Identity Management (PIM) Solutions
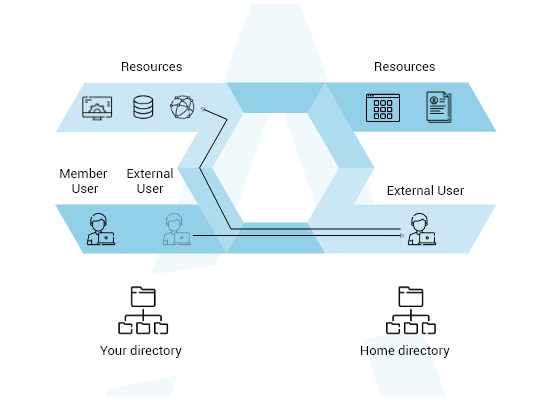
Our PIM solutions provide time-based and approval-based role activation to mitigate the risks of excessive, unnecessary, or misused access permissions on resources that you care about. It can be anything either to comply with security regulations or to take back control of unconstrained admin access rights, our PIM solutions can help in meeting compliance requirements and reduce security risks without affecting operations.
Also, PIM can help enforce role-based controls across on-premise, cloud, and hybrid infrastructures. We build futuristic infrastructure to encounter any sophisticated threats.
SERVICE OFFERINGS
Security is the Immune System
As you partner with us, you can experience automate tracking and provisioning of access, reduction in manual interventions, and quick delivery of compliance standards.
In some cases, leadership teams and members of senior management may have administrative privileges and access to the organization’s sensitive information. Such rights and access need close monitoring and adequate controls to avoid any compromise.
Whether on-site or remote, we ensure specific users access so that they can only access information within their privilege limits including the type of action.

Some of the Networking solutions we provide are:
Build a strong networking infrastructure with Atrity and establish a hassle-free communicative space between your endpoints and users.
- Design & Implementation of LAN/WAN (Structured/Semi-Structured/Normal)
- Network Auditing along with assessment of current setup
- Site Planning via operation research techniques & scheduled cable blueprinting
- Structured Cabling
- Optimization of network resources
- Network Management
- Network Security Planning & Implementation
- Networking Switches
- Switching Rack & Server Rack
- Firewall
 Read More
Read More