Migrate Everything to the Clouds
At Atrity, we provide higher visibility and control across our cloud cybersecurity infrastructure enabling secure applications and connectivity from the data centre to the cloud.
To monitor the activity and configuration of multiple cloud security products and resources, we exploit the public cloud management API that provides consistent compliance reports in multi-cloud environments and streamlined incident investigation.
Our advanced application layer cloud security controls offer organizations the confidence to choose the best cloud platforms and technology systems based on their business priorities and security requirements.
If you’re using cloud infrastructure and shifting toward multi-cloud environments, then you will definitely require secure network connectivity across different locations to abstract physical boundaries while protecting the confidentiality of communications.
Cloud Security
Our security experts provide global cloud security with compute capabilities at the edge and enforce zero trust principles across data protection and threat prevention.
SERVICE OFFERINGS
Hidden Inside the Clouds
We enforce consistent cloud security across all environments controlled with single-pane-of-glass management to protect connectivity across public, private clouds, multi, and hybrid clouds.
As you collaborate with us, you can experience a centralized, shared, and consistent security enforcement with a cloud security software hub that helps ensure the secure connection of networks, locations, clouds, and data centres that build organizational agility without any compromises in security.

Some of the Networking solutions we provide are:
Build a strong networking infrastructure with Atrity and establish a hassle-free communicative space between your endpoints and users.
- Design & Implementation of LAN/WAN (Structured/Semi-Structured/Normal)
- Network Auditing along with assessment of current setup
- Site Planning via operation research techniques & scheduled cable blueprinting
- Structured Cabling
- Optimization of network resources
- Network Management
- Network Security Planning & Implementation
- Networking Switches
- Switching Rack & Server Rack
- Firewall






INDUSTRIES WE WORK WITH
Breakthrough Cyber Security Technologies
Our cyber security experts at Atrity understand the complexity in any industry and maintain a lasting relationship with each client. We have a dedicated cybersecurity team that helps to manage cyber-related threats and challenges with unified solutions, advanced detection, strong domain knowledge, holistic approaches, and advanced technology capabilities.
Technology Demands Innovation.

- Ability to relate monitoring, intelligence, management, and reputation with the final goal at every step
- Proven capabilities to undertake strategic projects, as well as operational assignments
- Cost-efficient operations, troubleshooting, comprehensive service assurance, and analytics
- Have gone through Technical Assurance Process (TAP) to ensure that our services meet our client’s standards
FAQ
Your Questions Answered.
What is the process of your cloud security?
This is the step-by-step process we follow to secure any information in the cloud – we use a cloud service that encrypts your data both in the cloud and computer, setup the privacy settings, implement two-factor authentication, install the strong anti-malware program, and ultimately upgrade your OS consistently.
What are the steps for managing and securing cloud services?
Here are some steps that we follow to manage data in the clouds – ensure effective governance and compliance, audit operation & business process, enforce privacy policies, assess security considerations for cloud applications, secure cloud networks & connections, and evaluate security controls and physical infrastructure.
What are the four areas of cloud security?
The four areas/pillars of cloud security include – visibility and compliance, compute-based security, network protection, and identity security.
How do you address cloud security?
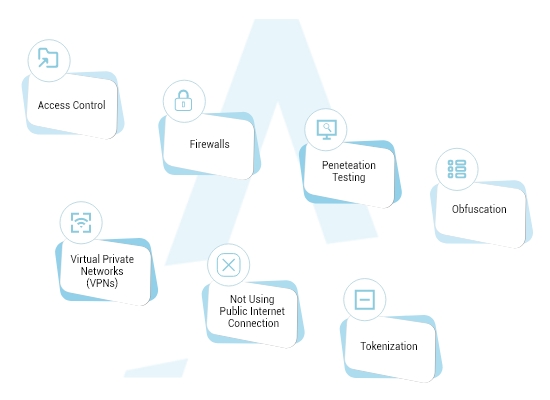
Cloud security is the protection of data from theft, leakage, and deletion. Methods of providing cloud security include firewalls, penetration testing, obfuscation, tokenization, virtual private networks (VPN), and avoiding public internet connections.
How can I secure my cloud application?
Discover and access cloud apps, employ data loss prevention (DLP) with cloud access security brokers (CASB), restrict downloading sensitive data to insecure devices, by all these you can secure the cloud application.
How much do you cost for cloud security?
We cannot give a blank pricing statement. Based on your requirements, price ranges may vary. To know more about our pricing structures, feel free to drop us a message at any time.
 Read More
Read More




