Unique and Comprehensive Database Security Services
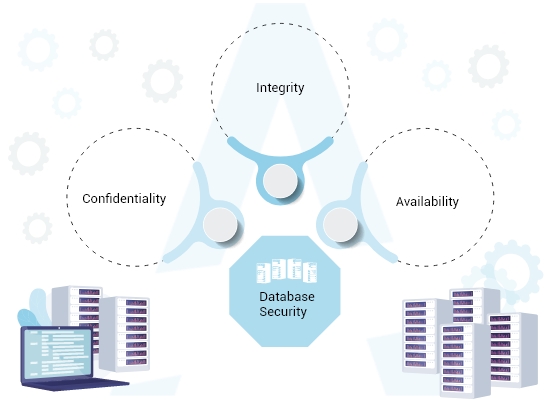
We’re a powerful company in offering database monitoring and scanning solution with activity monitoring, cyber blocking, privileged user access, multi-factor control, data classification, transparent data encryption, consolidated auditing, reporting, secure configuration management, and data masking.
Avoid data breaches and simplify compliance with database security solutions for encryption, key management, data masking, privileged user access controls, activity monitoring, and auditing.
With our automated database security, you can defend against threats and save time and minimize human error. Mitigate risks from users, data, and configurations with our enhanced security approaches while reducing the risk of human error by including features like always-on encryption, automated patching, and preconfigured separation of duties.
SERVICE OFFERINGS
Welcome Only Legitimate Users
Atrity’s database security empower clients to leverage a wide range of solutions, protect sensitive data from internal and external threats and accelerate compliance efforts.
We can build a multi-layered architecture for database security with a self-securing autonomous database. Patches are applied automatically and encryption is always enabled with Atrity’s data centre. Our engineers provide a unified and comprehensive database security console that blocks unwanted malware from accessing your system.

Some of the Networking solutions we provide are:
Build a strong networking infrastructure with Atrity and establish a hassle-free communicative space between your endpoints and users.
- Design & Implementation of LAN/WAN (Structured/Semi-Structured/Normal)
- Network Auditing along with assessment of current setup
- Site Planning via operation research techniques & scheduled cable blueprinting
- Structured Cabling
- Optimization of network resources
- Network Management
- Network Security Planning & Implementation
- Networking Switches
- Switching Rack & Server Rack
- Firewall






INDUSTRIES WE WORK WITH
Breakthrough Cyber Security Technologies
Our cyber security experts at Atrity understand the complexity in any industry and maintain a lasting relationship with each client. We have a dedicated cybersecurity team that helps to manage cyber-related threats and challenges with unified solutions, advanced detection, strong domain knowledge, holistic approaches, and advanced technology capabilities.
Technology Demands Innovation.

- Cost-efficient operations, troubleshooting, comprehensive service assurance, and analytics
- Have gone through Technical Assurance Process (TAP) to ensure that our services meet our client’s standards
- Experienced team that can foresee various eventualities and take proactive action
- Full traceability, collaborative working, built-in flexibility approaches, best-in-breed processes, and feedback-driven models
FAQ
Your Questions Answered.
What are the most important data centre security standards?
Layered security measures, access lists, video surveillance, secure access points, RFID asset management, multi-factor authentication, and biometric technology are the most important data centre security standards.
What are the security devices used in data centres?
Some of the devices used in data centre security include canning personal identity verification (PIV) cards, employee badge readers, biometric systems, fingerprint readers, iris scanners, and facial recognition devices.
What are the data centre tiers?
Data centre tiers are classified as tier 1, tier 2, tier 3, and tier 4. It is used to quickly identify the complexity and redundancy of the data centre infrastructure and describe specific kinds of data centre infrastructure consistently.
What is the highest tier data centre?
Tier 4 data centre security is counted to be the highest tier data centre. Businesses with constant availability take advantage of this tier. They have an uptime of 99.995% that is equal to an annual downtime of no more than 26 minutes.
What are the forces impacting data centre security?
Hacking, malware, spyware, unauthorized access, data thefts, etc are the various cyber-attacks impacting data centre security.
How much do you cost for data centre security services?
We cannot give a blank pricing statement. Based on your requirements, price ranges may vary. To know more about our pricing structures, feel free to drop us a message at any time.
 Read More
Read More