In today’s digital world, organizations generate and store massive amounts of sensitive data. Protecting this information is critical to prevent cyberattacks, data breaches, and regulatory violations. A strong data protection strategy helps businesses secure their data while maintaining smooth operations.
IT teams play a vital role by implementing secure infrastructure, backups, encryption, and access controls to protect data systems. Cybersecurity professionals focus on identifying threats, monitoring networks, and responding to potential attacks. Compliance teams ensure the organization follows legal and regulatory standards such as data privacy laws. Meanwhile, business leaders must align data protection policies with organizational goals and risk management strategies.
Understanding Data Protection Strategy: Core Concepts

The three fundamental pillars of an effective data protection strategy
A data protection strategy is a comprehensive plan that outlines the measures, processes, and technologies an organization implements to secure its mission-critical and regulated data while ensuring it remains accessible for legitimate business purposes. Unlike narrower approaches that focus solely on specific aspects like backup or encryption, a robust data protection strategy addresses the entire data lifecycle and integrates with broader business objectives.
The Three Pillars of Data Protection
Data Security
Protects data from unauthorized access, malicious attacks, and accidental damage through encryption, access controls, and monitoring systems.
Data Availability
Ensures critical data remains accessible during disruptions through backup systems, disaster recovery planning, and business continuity measures.
Access Control
Manages who can access specific data assets through authentication, authorization, and privilege management systems.
These three pillars work in concert to create a defense-in-depth approach that addresses the complex challenges of modern data environments. When properly implemented, they ensure that data is protected from threats while remaining available to authorized users who need it for legitimate business purposes.
The Business Case for a Data Protection Strategy
The financial and reputational impact of inadequate data protection can be severe. The average cost of a data breach has risen significantly in recent years, reaching millions of dollars per incident. Beyond these direct costs, organizations also face regulatory penalties, lost business opportunities, and a decline in customer trust.
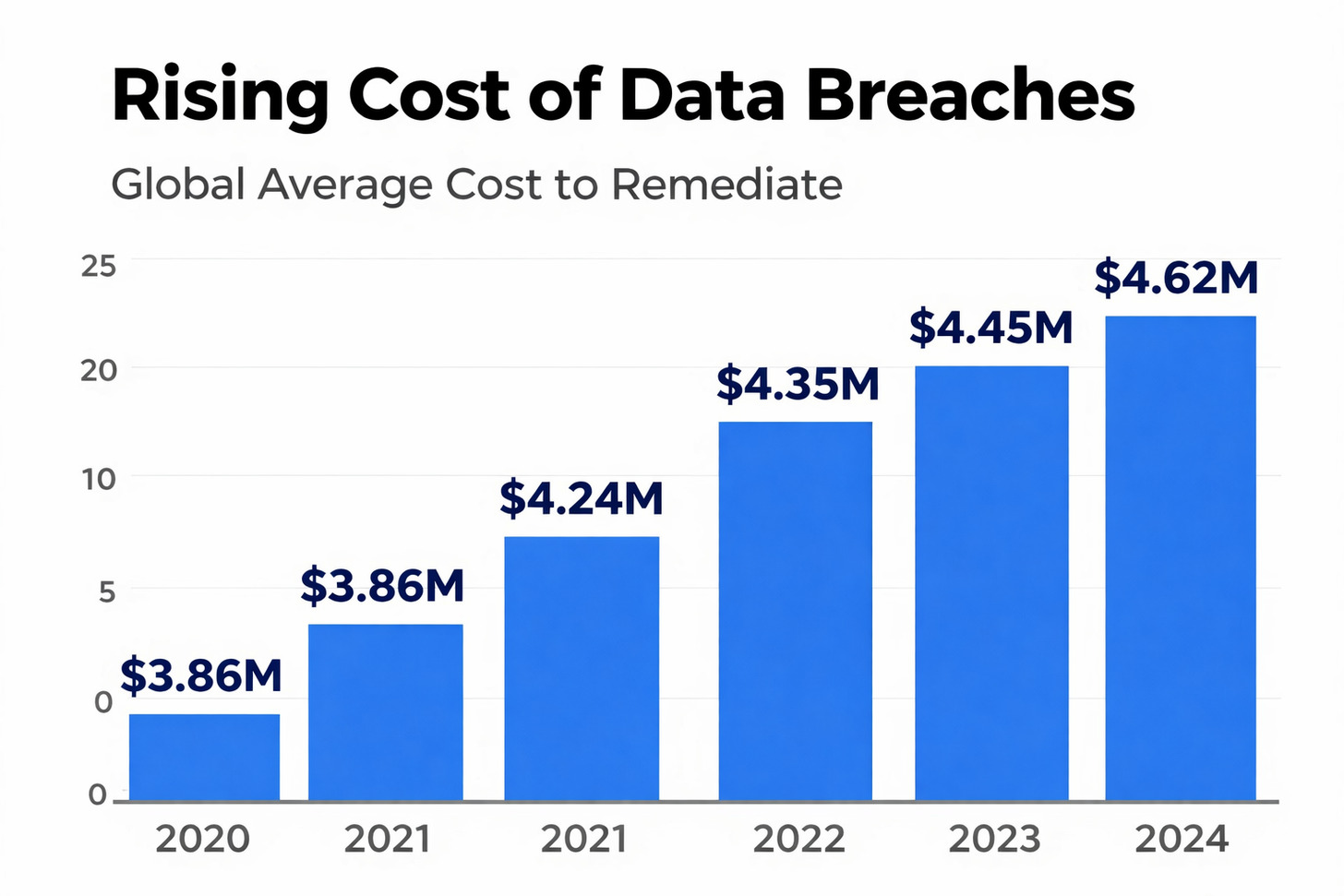
The rising cost of data breaches highlights the financial imperative for robust protection
Key Business Drivers for Data Protection
- Regulatory Compliance: Meeting requirements of GDPR, HIPAA, CCPA, and industry-specific regulations to avoid penalties and legal consequences.
- Customer Trust: Maintaining the confidence of customers and partners who entrust their sensitive information to your organization.
- Intellectual Property Protection: Safeguarding proprietary information and trade secrets that provide competitive advantage.
- Business Continuity: Ensuring operations can continue even in the face of data breaches, ransomware attacks, or system failures.
- Competitive Advantage: Leveraging strong data protection as a market differentiator in industries where security is a key concern.
“Organizations with high levels of incident response countermeasures in place incurred $1.49 million lower data breach costs compared to organizations with low levels or none, and they resolved incidents 54 days faster.”
Essential Components of a Comprehensive Data Protection Strategy
Building an effective data protection strategy requires integrating multiple components that address different aspects of data security, availability, and governance. While specific implementations will vary based on organizational needs, the following components form the foundation of a robust approach:

The interconnected components of a comprehensive data protection strategy
Data Classification and Discovery
Before you can protect data effectively, you must understand what data you have, where it resides, and its sensitivity level. Data classification creates a foundation for applying appropriate protection measures based on data value and risk.
Classification Categories
- Public: Information that can be freely shared
- Internal: For use within the organization only
- Confidential: Sensitive information requiring protection
- Restricted: Highly sensitive data with strict access limitations
Discovery Methods
- Automated scanning tools to locate sensitive data
- Data flow mapping to track information movement
- Asset inventories to document data repositories
- Regular audits to verify classification accuracy
Data Access Management Controls
Controlling who can access specific data assets is fundamental to data protection. Effective access management implements the principle of least privilege, ensuring users have only the access they need to perform their roles.
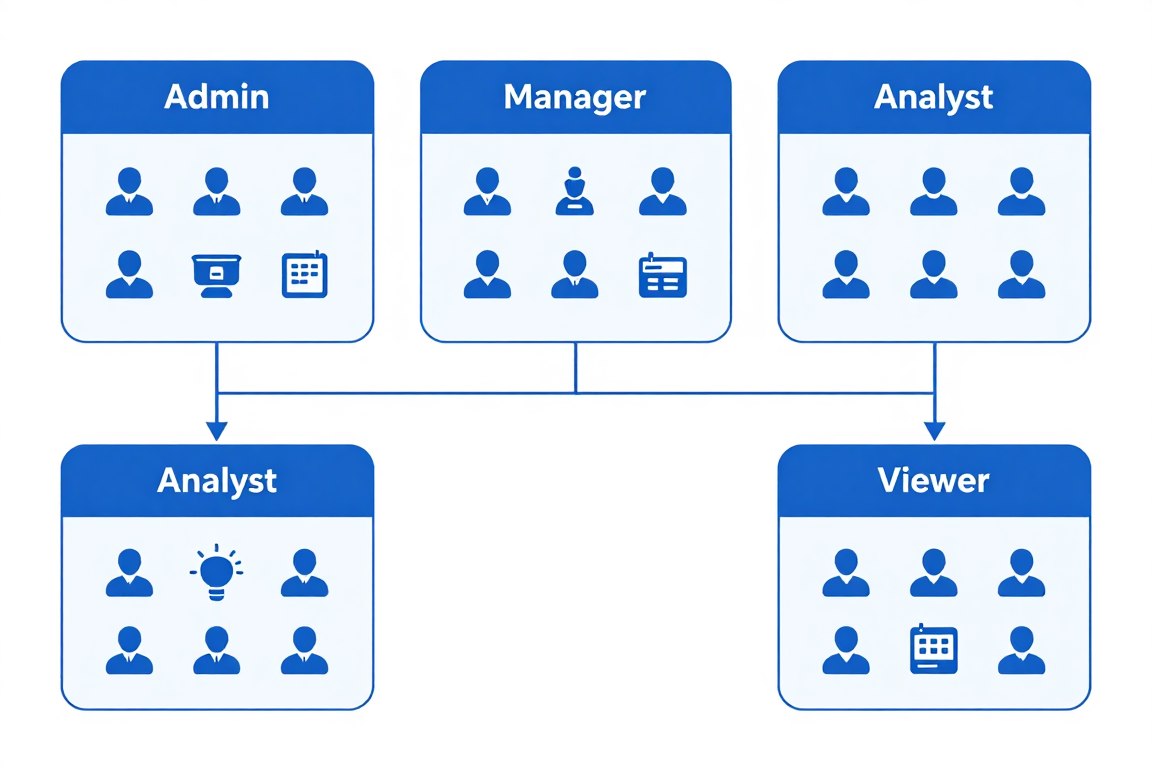
Role-based access control model for protecting sensitive data
- Identity and Access Management (IAM): Frameworks that manage digital identities and their access privileges
- Role-Based Access Control (RBAC): Assigning access permissions based on job functions
- Multi-Factor Authentication (MFA): Requiring multiple verification methods to prove user identity
- Privileged Access Management (PAM): Special controls for accounts with elevated permissions
- Zero Trust Architecture: Verifying every access request regardless of source or location
Data Encryption and Protection
Encryption transforms readable data into an encoded format that can only be accessed with the proper decryption keys. It provides a critical layer of protection for data both at rest (stored) and in transit (being transmitted).
Encryption Types
- Data at Rest: Protecting stored information on servers, databases, and endpoints
- Data in Transit: Securing information as it moves across networks
- End-to-End Encryption: Protecting data throughout its entire journey
- Tokenization: Replacing sensitive data with non-sensitive equivalents
Key Management
- Secure generation and storage of encryption keys
- Key rotation and lifecycle management
- Hardware Security Modules (HSMs) for key protection
- Recovery procedures for lost keys
Encryption Best Practice: Implement a centralized key management system that enforces separation of duties and maintains detailed audit logs of all key operations. This prevents any single administrator from having complete control over both encrypted data and the keys needed to decrypt it.
Data Backup and Recovery
Even with strong preventive controls, organizations must prepare for potential data loss scenarios. A robust backup and recovery strategy ensures business continuity in the face of ransomware attacks, system failures, or natural disasters.
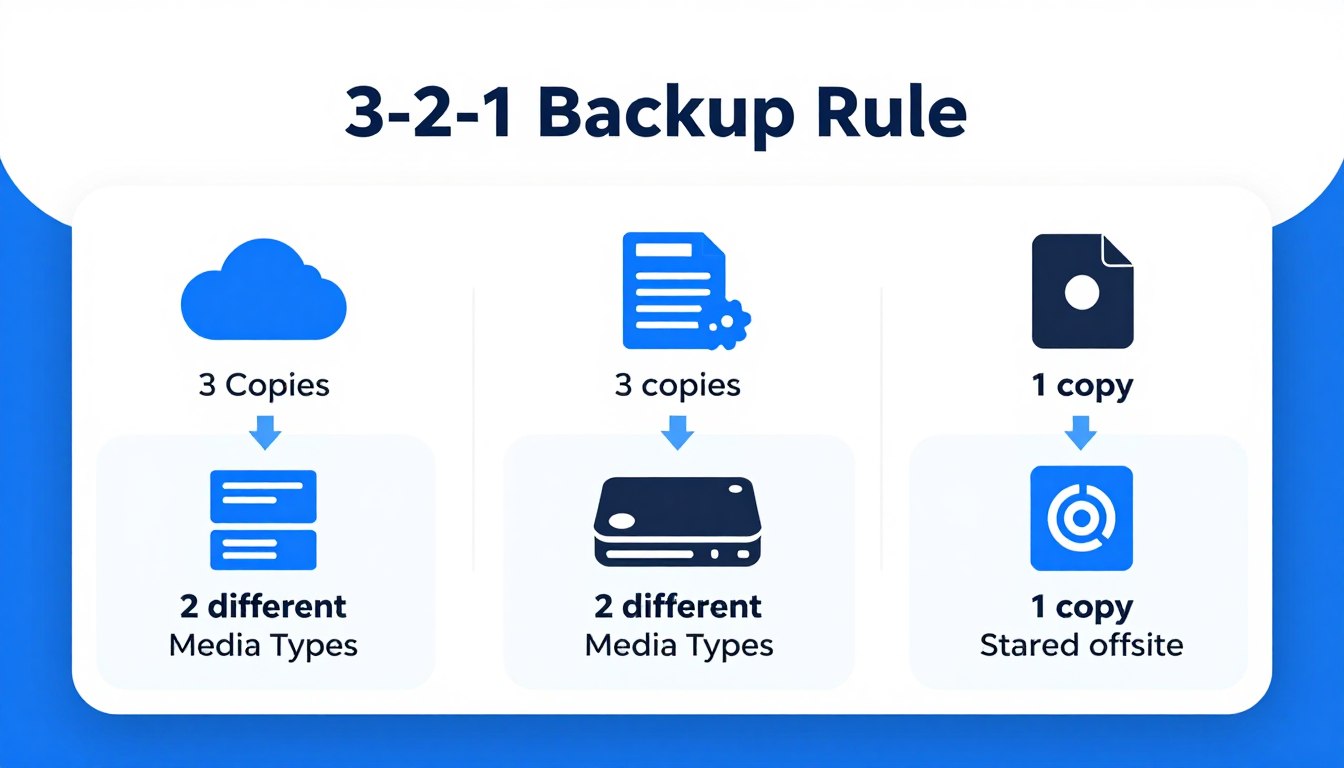
The 3-2-1 backup rule: A fundamental principle for data protection
- 3-2-1 Backup Rule: Maintain at least three copies of data on two different media types with one copy stored offsite
- Recovery Point Objective (RPO): Maximum acceptable data loss measured in time
- Recovery Time Objective (RTO): Maximum acceptable downtime for system restoration
- Immutable Backups: Backups that cannot be altered or deleted, even by administrators
- Testing and Validation: Regular verification that backups can be successfully restored
“The ability to recover quickly from a ransomware attack depends not just on having backups, but on having the right kind of backups—those that are isolated, immutable, and regularly tested.”
Incident Response Planning
Despite preventive measures, security incidents can still occur. An incident response plan provides a structured approach for detecting, containing, and recovering from data breaches and other security events.

The incident response lifecycle for effective data breach management
- Preparation: Developing response procedures and training team members
- Detection and Analysis: Identifying and assessing security incidents
- Containment: Limiting the scope and impact of the incident
- Eradication: Removing the threat from the environment
- Recovery: Restoring systems and data to normal operations
- Lessons Learned: Analyzing the incident to improve future responses
Critical Reminder: Incident response plans should include clear procedures for meeting breach notification requirements under applicable regulations like GDPR, HIPAA, and state data breach laws. These often have strict timelines for reporting incidents to authorities and affected individuals.
Regulatory Compliance Management
Organizations must navigate an increasingly complex landscape of data protection regulations. A compliance management framework helps track requirements, implement necessary controls, and demonstrate adherence to regulators.
| Regulation | Scope | Key Requirements | Penalties for Non-Compliance |
| GDPR | EU resident data | Consent, data minimization, breach notification | Up to 4% of global revenue or €20M |
| HIPAA | US healthcare data | Privacy safeguards, security controls, business associate agreements | Up to $1.5M per violation category annually |
| CCPA/CPRA | California resident data | Disclosure, opt-out rights, data deletion | $2,500-$7,500 per violation |
| PCI DSS | Payment card data | Secure networks, encryption, access controls | $5,000-$100,000 monthly fines |
Effective compliance management requires a cross-functional approach involving legal, IT, security, and business units. Organizations should implement a governance framework that clearly defines roles and responsibilities for maintaining compliance with relevant regulations.
Security Awareness and Training
Human error remains one of the leading causes of data breaches. A comprehensive security awareness program educates employees about their role in protecting sensitive information and builds a security-conscious culture.

Regular security awareness training is essential for maintaining a strong data protection posture
- Phishing Simulations: Testing employees ability to recognize and report suspicious emails
- Role-Based Training: Tailoring security education to specific job functions
- Security Champions: Designating advocates within business units to promote security practices
- Continuous Education: Providing regular updates on emerging threats and protection techniques
- Measurable Outcomes: Tracking improvements in security behaviors over time
Implementing Your Data Protection Strategy: A Practical Approach
Developing a data protection strategy is one thing; implementing it effectively across an organization is another challenge entirely. The following framework provides a structured approach to turning strategic plans into operational reality.
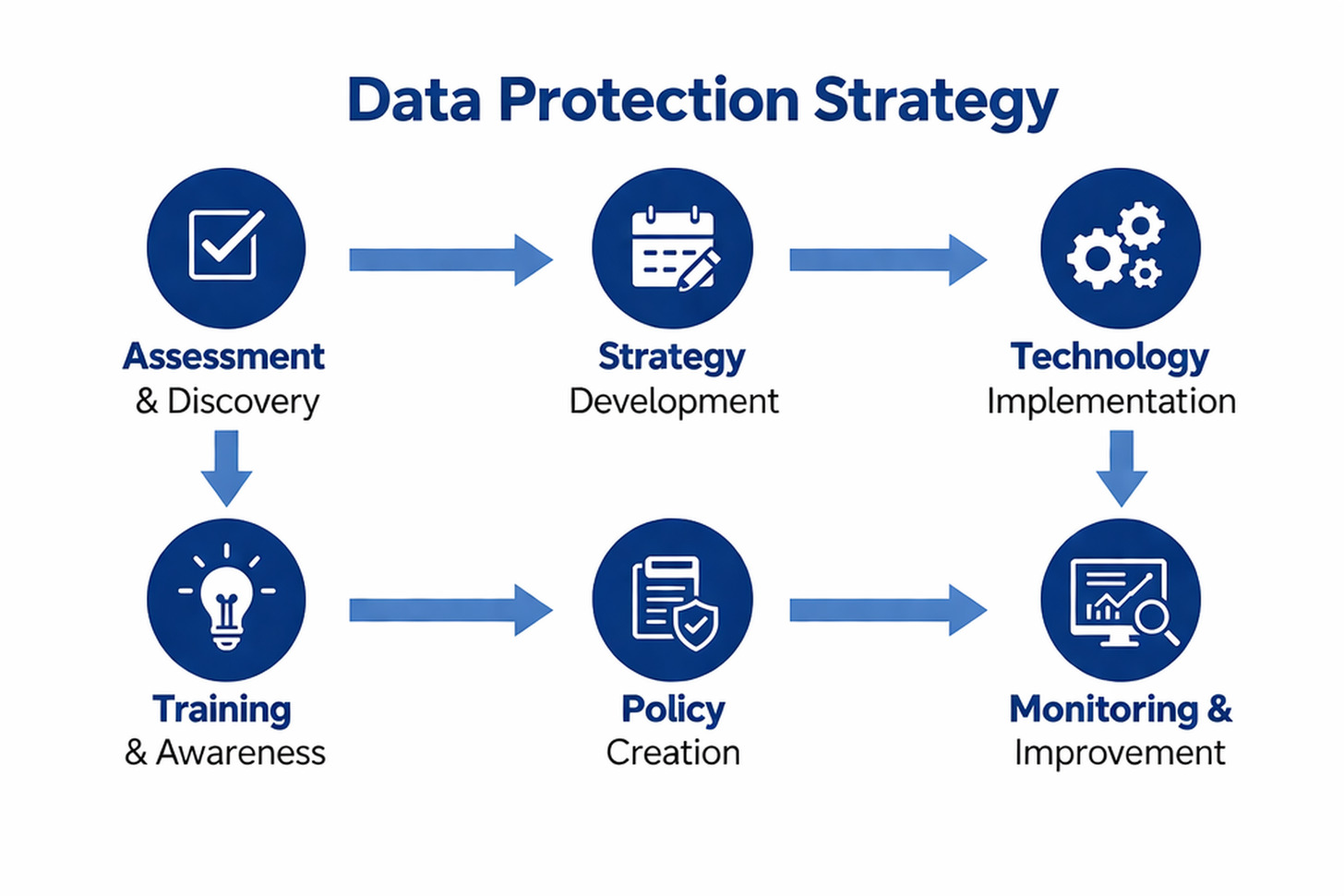
A phased approach to implementing a comprehensive data protection strategy
Phase 1: Assessment and Planning
- Data Inventory: Catalog all data assets, their sensitivity, and their locations
- Risk Assessment: Identify and prioritize data protection risks
- Gap Analysis: Compare current controls against requirements and best practices
- Stakeholder Engagement: Secure buy-in from executives and department leaders
- Resource Planning: Determine budget, personnel, and technology needs
Phase 2: Policy and Governance Development
- Policy Framework: Create or update data protection policies
- Roles and Responsibilities: Define accountability for data protection
- Metrics and KPIs: Establish measures to track implementation progress
- Compliance Mapping: Align controls with regulatory requirements
- Governance Committees: Form oversight groups to guide implementation
Phase 3: Technical Implementation
- Access Control Systems: Deploy IAM solutions and enforce least privilege
- Encryption Technologies: Implement data encryption for sensitive information
- Backup Infrastructure: Establish resilient backup and recovery capabilities
- Monitoring Tools: Deploy solutions to detect unauthorized access or data leakage
- Security Testing: Validate controls through penetration testing and assessments
Phase 4: Training and Awareness
- General Awareness: Educate all employees on basic data protection principles
- Specialized Training: Provide in-depth education for IT and security teams
- Executive Briefings: Keep leadership informed about program status
- Communication Plan: Develop ongoing messaging to reinforce security culture
- Feedback Mechanisms: Create channels for employees to report concerns
Phase 5: Monitoring and Improvement
- Continuous Monitoring: Track data access and usage patterns
- Regular Audits: Verify compliance with policies and regulations
- Incident Response Drills: Test and refine breach response procedures
- Metrics Review: Analyze performance against established KPIs
- Program Updates: Evolve the strategy to address emerging threats and requirements
Data Protection Strategy Best Practices
Based on industry experience and lessons learned from organizations with mature data protection programs, the following best practices can help maximize the effectiveness of your strategy:

Key best practices for an effective data protection strategy
Strategic Approaches
- Risk-Based Prioritization: Focus resources on protecting the most sensitive data first
- Defense in Depth: Implement multiple layers of protection
- Privacy by Design: Build data protection into processes from the start
- Continuous Improvement: Regularly review and enhance controls
- Cross-Functional Collaboration: Involve all relevant departments
Technical Considerations
- Automation: Use technology to reduce manual security tasks
- Data Minimization: Collect and retain only necessary information
- Segmentation: Isolate sensitive data in protected environments
- Regular Testing: Validate controls through security assessments
- Vendor Management: Ensure third parties meet your security standards
“The most effective data protection strategies balance security with usability. If security measures are too cumbersome, users will find ways to work around them, potentially creating greater risks.”
Common Challenges and How to Overcome Them
Implementing a data protection strategy inevitably comes with obstacles. Understanding these challenges in advance can help organizations prepare effective responses.

Common data protection challenges and strategic approaches to address them
Challenges
- Resource Constraints: Limited budget and personnel for implementation
- Shadow IT: Unauthorized applications and data repositories
- Legacy Systems: Outdated technology lacking modern security features
- Cloud Complexity: Managing data across multiple cloud environments
- Compliance Burden: Keeping up with evolving regulatory requirements
Solutions
- Risk-Based Prioritization: Focus resources on highest-risk areas first
- Discovery Tools: Implement solutions to identify unauthorized applications
- Compensating Controls: Add protection layers around legacy systems
- Cloud Security Platforms: Use tools designed for multi-cloud management
- Automated Compliance: Leverage technology to streamline compliance tasks
Measuring the Success of Your Data Protection Strategy
Effective data protection requires ongoing measurement to validate that controls are working as intended and to identify areas for improvement. A balanced set of metrics helps organizations track both leading indicators (preventive measures) and lagging indicators (incident outcomes).

A comprehensive dashboard for tracking data protection performance metrics
Key Performance Indicators
| Metric Category | Example Metrics | Target | Measurement Frequency |
| Risk Reduction | Number of high-risk findings remediated | 90% within SLA | Monthly |
| Security Incidents | Data breach frequency and impact | Year-over-year reduction | Quarterly |
| Compliance | Audit findings and regulatory violations | Zero critical findings | Per audit cycle |
| Operational | Mean time to detect and respond to incidents | Per incident | |
| User Awareness | Phishing simulation success rate | Per campaign |
Regular reporting on these metrics to executive leadership helps maintain visibility and support for the data protection program. Dashboards and scorecards can provide at-a-glance views of current status, while detailed reports enable deeper analysis of trends and patterns.
Future Trends in Data Protection
The data protection landscape continues to evolve rapidly in response to emerging technologies, changing threat patterns, and new regulatory requirements. Organizations should monitor these trends to ensure their strategies remain effective.

Emerging technologies shaping the future of data protection
AI and Machine Learning
Artificial intelligence is transforming data protection through anomaly detection, automated threat response, and predictive risk analysis. These technologies enable more proactive and adaptive security measures.
Privacy-Enhancing Technologies
Innovations like homomorphic encryption, federated learning, and differential privacy allow organizations to derive value from data while preserving confidentiality and meeting privacy requirements.
Zero Trust Architecture
The shift from perimeter-based security to zero trust models—where nothing is trusted by default—is reshaping how organizations approach data access and protection in distributed environments.
As these technologies mature, organizations should evaluate how they can be incorporated into existing data protection frameworks. Early adoption of promising approaches can provide competitive advantages while enhancing security posture.
Conclusion: Building a Resilient Data Protection Strategy
At Atrity, data protection is more than security—it’s a strategic foundation for business success. By combining advanced technologies, Zero Trust principles, and continuous monitoring, Atrity helps organizations protect sensitive data, ensure compliance, and stay resilient against evolving threats. With the right strategy in place, businesses can confidently innovate and grow in a secure environment.
What is the difference between data security and data protection?
Data security focuses specifically on protecting data from unauthorized access and cyber threats through measures like encryption and access controls. Data protection is a broader concept that encompasses security but also includes data availability, integrity, privacy compliance, and lifecycle management. A comprehensive data protection strategy addresses both securing data from threats and ensuring it remains available and usable for legitimate business purposes.
How often should we review and update our data protection strategy?
At minimum, organizations should conduct a formal review of their data protection strategy annually. However, more frequent updates may be necessary in response to significant changes such as:
- New regulatory requirements
- Major changes to IT infrastructure or business operations
- Emerging threat patterns or security incidents
- Adoption of new technologies or data processing activities
The most effective approach is to treat the strategy as a living document that evolves continuously through regular assessment and improvement cycles.
Who should be responsible for implementing a data protection strategy?
While the specific roles may vary by organization size and structure, data protection typically requires collaboration across multiple functions:
- Executive Leadership: Providing sponsorship and resources
- Chief Information Security Officer (CISO): Overall security strategy and implementation
- Data Protection Officer (DPO): Privacy compliance and data subject rights
- IT Department: Technical implementation and operations
- Legal and Compliance: Regulatory requirements and policy development
- Business Unit Leaders: Ensuring adoption within their departments
Effective governance requires clear definition of roles, responsibilities, and accountability at each level of the organization.
How do we balance data protection with business needs for data access and utilization?
Finding the right balance between protection and utility requires a risk-based approach:
- Classify data based on sensitivity and apply controls proportionate to risk
- Involve business stakeholders in security decisions to understand operational impacts
- Implement technologies that protect data while enabling legitimate use (e.g., encryption that preserves functionality)
- Focus on user experience in security implementations to minimize friction
- Regularly review controls to identify and address unnecessary obstacles to productivity
The goal should be to implement “just enough” security—providing adequate protection without imposing unnecessary barriers to legitimate business activities.
What are the most common pitfalls in implementing a data protection strategy?
Organizations often encounter these challenges when implementing data protection:
- Focusing on technology alone without addressing people and processes
- Treating compliance as the end goal rather than as a baseline requirement
- Implementing controls uniformly across all data without risk-based prioritization
- Neglecting user experience, leading to workarounds that undermine security
- Failing to measure effectiveness through meaningful metrics and assessments
- Overlooking third-party risks from vendors and service providers
Successful implementation requires a holistic approach that addresses technology, people, and processes while maintaining alignment with business objectives.
 Read More
Read More