Bring Your Email Security Vision into Reality
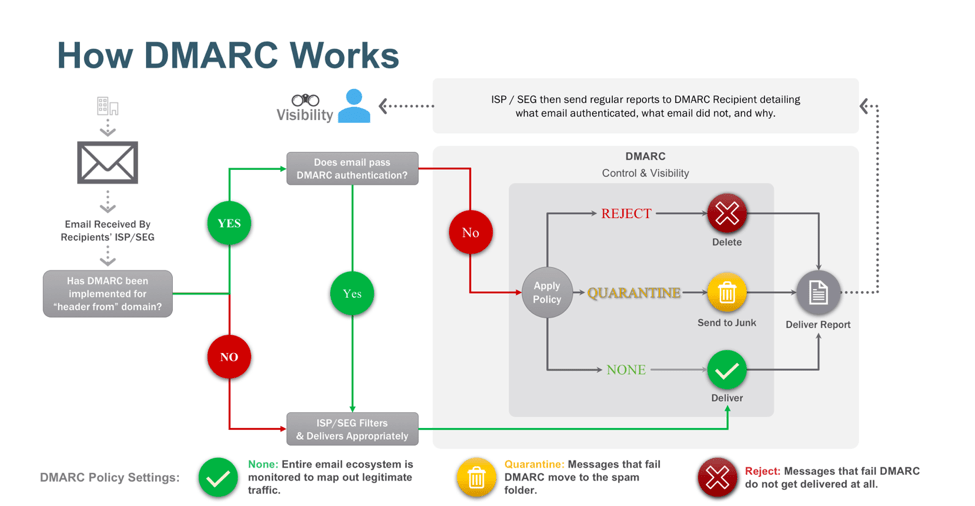
Atrity helps organizations safeguard their brand reputation by implementing DMARC (Domain-based Message Authentication, Reporting & Conformance), a globally trusted standard for preventing domain spoofing and fraudulent email delivery.
With extensive experience in SPF, DKIM, DMARC, DNS, and third-party mail service integrations, our team ensures a smooth and risk-free transition from monitoring to full protection. We enable complete visibility across email channels and enforce policies that prevent attackers from misusing your domain.
By choosing Atrity’s DMARC services, you gain powerful protection against phishing, malware campaigns, brand impersonation, and email-based fraud—all without installing any hardware or software.
SERVICE OFFERINGS
Comprehensive Email Authentication & DMARC Implementation
We thoroughly assess your entire email ecosystem—covering transactional platforms, marketing tools, applications, portals, and all third-party senders—before deploying DMARC in a structured, secure, and phased approach.
After understanding your current setup and communication flow, we guide you through each stage of DMARC adoption to ensure maximum protection with zero disruption to legitimate emails.

World-Class Email Authentication for All Sectors
From BFSI and healthcare to retail, manufacturing, IT, and government agencies, organizations across industries rely on Atrity’s DMARC solutions to maintain trust and secure their communication channels.
We help you ensure your emails reach the inbox while blocking attackers who attempt to impersonate your brand.
SPF, DKIM & DMARC Setup and Configuration
Alignment Validation and Policy Optimization
Progressive Policy Deployment (Monitoring → Quarantine → Reject)
Detailed Analysis of Forensic & Aggregate Reports
Identification & Management of Unrecognized or Unauthorized Senders
Ongoing Fine-Tuning to Prevent Legitimate Email Interruption
Fully Managed Support from Email Authentication Specialists
 Read More
Read More