In an increasingly connected world, the line between digital systems and physical infrastructure continues to blur. Operational Technology (OT) systems that control critical infrastructure like power grids, water treatment facilities, and manufacturing plants are now prime targets for sophisticated cyber attacks. Understanding the importance of OT security has become essential for organizations that operate these vital systems, as the consequences of a breach extend far beyond data loss to potentially catastrophic physical impacts.
What is Operational Technology (OT)?
Operational Technology refers to the hardware and software systems that monitor and control physical devices, processes, and events in industrial environments. Unlike Information Technology (IT), which focuses on data management and processing, OT directly interfaces with the physical world, controlling equipment and processes that form the backbone of critical infrastructure.

Key Components of OT Systems
Hardware Components
- Programmable Logic Controllers (PLCs) that automate industrial processes
- Remote Terminal Units (RTUs) that interface with physical equipment
- Human-Machine Interfaces (HMIs) for operator control
- Distributed Control Systems (DCS) for process management
- Sensors and actuators that interact with physical processes
Software Components
- Supervisory Control and Data Acquisition (SCADA) systems
- Industrial control software for process automation
- Firmware embedded in industrial devices
- Specialized analytics and management applications
- Communication protocols (Modbus, DNP3, OPC-UA)
OT systems are prevalent across numerous critical sectors including energy production and distribution, water treatment, manufacturing, transportation, and healthcare. These systems were traditionally isolated from external networks, operating in what security professionals call an “air-gapped” environment. However, the rise of digital transformation and the Industrial Internet of Things (IIoT) has increasingly connected these once-isolated systems to corporate networks and even the internet.
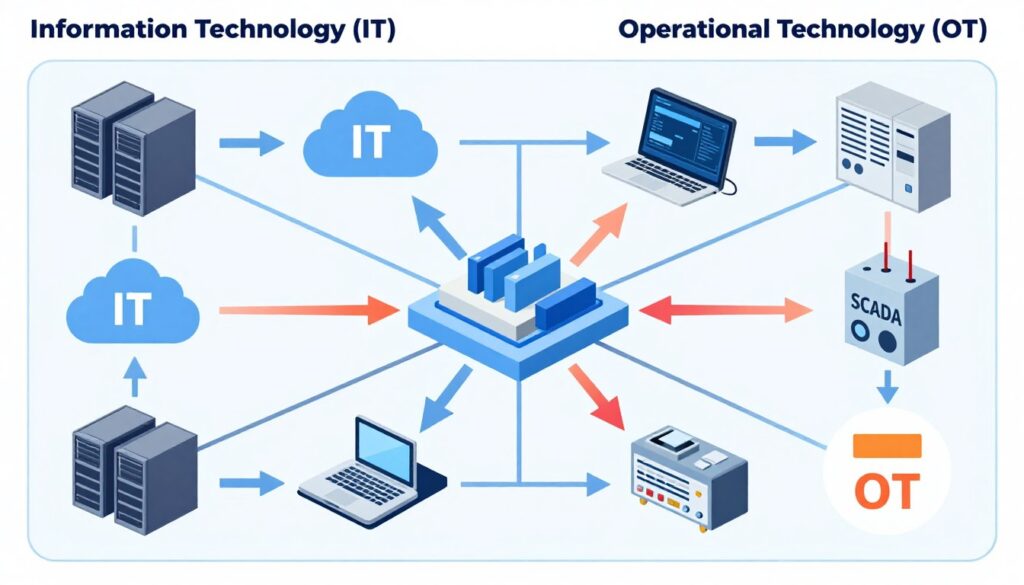
The Critical Differences Between IT and OT Security
While IT and OT systems both require cybersecurity protection, the approaches and priorities differ significantly. Understanding these differences is crucial for implementing effective OT security measures.

| Aspect | IT Security | OT Security |
| Primary Focus | Data protection and information management | Physical process control and operational safety |
| Priority Order | Confidentiality, Integrity, Availability (CIA) | Safety, Availability, Integrity, Confidentiality (SAIC) |
| System Lifecycle | 3-5 years with regular updates | 15-20 years with minimal changes |
| Patching Approach | Regular and automated | Carefully scheduled during maintenance windows |
| Downtime Impact | Business inconvenience | Safety risks, production losses, regulatory violations |
| Attack Consequences | Data breach, financial loss | Physical damage, environmental harm, human safety risks |
The fundamental difference lies in the consequences of security failures. While an IT breach might lead to data theft or service disruption, an OT security incident could result in equipment damage, environmental disasters, or even loss of human life. This reality necessitates a specialized approach to OT security that balances cybersecurity requirements with operational continuity and safety considerations.
IT-OT Convergence: New Opportunities and Security Challenges
The growing integration of IT and OT systems, known as IT-OT convergence, offers significant operational benefits but also introduces new security challenges. This convergence is driven by the need for real-time data analytics, remote monitoring capabilities, and improved operational efficiency.
Benefits of IT-OT Convergence
- Enhanced operational visibility through real-time data analytics
- Improved decision-making based on comprehensive operational insights
- Remote monitoring and management capabilities
- Increased efficiency and reduced operational costs
- Predictive maintenance to prevent equipment failures
Security Challenges of Convergence
Security Challenges
- Expanded attack surface as previously isolated systems become connected
- Legacy OT systems with known vulnerabilities exposed to new threats
- Conflicting security priorities between IT and OT teams
- Increased complexity in managing security across integrated environments
- Traditional IT security tools may disrupt critical OT operations
The Colonial Pipeline incident of 2021 exemplifies the risks of IT-OT convergence. What began as a ransomware attack on IT systems ultimately led to the shutdown of pipeline operations, causing fuel shortages across the eastern United States. This case demonstrates how security breaches can cross the IT-OT boundary with significant real-world consequences.
Unique Risks and Consequences of OT Security Breaches
The stakes of OT security are exceptionally high due to the direct connection between digital systems and physical processes. Understanding these unique risks is essential for appreciating the importance of robust OT security measures.

Physical Safety Risks
Unlike IT security breaches that primarily affect data, OT security incidents can directly impact physical safety. Attackers who gain control of industrial systems can potentially:
- Manipulate safety-critical equipment leading to dangerous conditions
- Disable safety mechanisms designed to prevent accidents
- Alter chemical mixtures or process parameters to unsafe levels
- Cause equipment malfunctions that endanger workers and nearby communities
“The 2017 TRITON/TRISIS attack on a petrochemical facility in Saudi Arabia specifically targeted Safety Instrumented Systems (SIS) designed to prevent catastrophic failures. This represented a concerning evolution in attacks specifically designed to compromise safety systems.”
Environmental Consequences
OT security breaches can lead to significant environmental damage through:
- Release of toxic chemicals or pollutants into air or water systems
- Disruption of environmental control systems at industrial facilities
- Interference with waste treatment processes
- Damage to natural resources through equipment failures
Operational and Economic Impact
Beyond safety and environmental concerns, OT security breaches can have severe operational and economic consequences:
Immediate Impacts
- Production downtime and lost revenue
- Equipment damage requiring costly repairs
- Product quality issues and potential recalls
- Emergency response costs
Long-term Consequences
- Regulatory fines and legal liabilities
- Increased insurance premiums
- Reputational damage affecting customer trust
- Market share loss to competitors
The 2021 Colonial Pipeline ransomware attack demonstrated these impacts clearly. Beyond the immediate $4.4 million ransom payment, the company faced significant operational disruption, emergency response costs, and reputational damage that will have lasting effects on its business.
Notable OT Security Attacks and Their Lessons
Examining past OT security incidents provides valuable insights into the evolving threat landscape and the importance of robust security measures.

Stuxnet (2010)
Targeted Iran’s nuclear program by manipulating centrifuge controls while displaying normal readings to operators. This sophisticated malware specifically targeted Siemens PLCs and demonstrated that even air-gapped systems are vulnerable.
Key Lesson: Physical isolation (“air-gapping”) alone is insufficient protection for critical OT systems.
Ukraine Power Grid (2015)
Attackers compromised power distribution companies, gained control of SCADA systems, and manually switched off substations, causing power outages affecting 230,000 people. They also disabled backup power to control centers.
Key Lesson: Critical infrastructure is a high-value target for nation-state actors with significant resources and capabilities.
Oldsmar Water Treatment (2021)
An attacker accessed the SCADA system of a Florida water treatment plant and attempted to increase sodium hydroxide (lye) levels to dangerous concentrations. An alert operator noticed and reversed the changes before harm occurred.
Key Lesson: Remote access to critical OT systems requires strict security controls and continuous monitoring.
Common Attack Vectors in OT Security Breaches:
- Exploitation of remote access connections
- Compromised credentials and weak authentication
- Phishing attacks targeting operational staff
- Supply chain compromises affecting OT components
- Exploitation of unpatched vulnerabilities in legacy systems
These incidents highlight the evolving sophistication of attacks against OT systems and the critical importance of comprehensive security measures that address both technical vulnerabilities and human factors.
OT Security as a National Security Concern
The security of operational technology has evolved from an organizational issue to a matter of national security. Governments worldwide now recognize critical infrastructure protection as essential to national resilience and security.

Critical Infrastructure Protection
Nations designate certain sectors as critical infrastructure due to their essential role in society. These typically include:
- Energy production and distribution systems
- Water and wastewater treatment facilities
- Transportation networks and control systems
- Healthcare and public health infrastructure
- Defense industrial base facilities
- Food and agriculture production systems
- Financial services infrastructure
- Communications networks
The disruption of these sectors through cyber attacks on their OT systems could have cascading effects across society, potentially affecting public safety, economic stability, and national security.
Nation-State Threats to OT Systems
Government security agencies have identified increasing activity from nation-state actors specifically targeting industrial control systems and other OT environments. These sophisticated threat actors often have:
- Extensive resources and technical capabilities
- Strategic patience for long-term operations
- Intelligence on specific industrial targets
- Custom-developed tools for OT environments
- Geopolitical motivations beyond financial gain
“The targeting of critical infrastructure to hold it at risk or to manipulate operations represents a significant escalation in ability and willingness to act aggressively against civilian systems in peacetime.”
This recognition of OT security as a national security concern has led to increased government involvement through regulations, information sharing initiatives, and public-private partnerships aimed at strengthening the security posture of critical infrastructure.
OT Security and Business Continuity
Beyond national security implications, OT security is fundamental to business continuity and organizational resilience. For companies operating industrial systems, the ability to maintain operations in the face of cyber threats is directly tied to business success.
The Business Case for OT Security Investment
Organizations must understand the business value of OT security investments. Key considerations include:
Direct Costs of OT Security Incidents
- Production downtime (often $100,000+ per hour in manufacturing)
- Equipment repair or replacement costs
- Incident response and forensic investigation expenses
- Regulatory fines and legal liabilities
- Potential ransom payments
Indirect Costs and Long-term Impacts
- Customer confidence and market share loss
- Increased insurance premiums
- Supply chain disruptions affecting partners
- Intellectual property theft
- Damage to brand reputation and shareholder value
The Colonial Pipeline incident demonstrated these business impacts clearly. Beyond the $4.4 million ransom payment, the company faced significant operational disruption, emergency response costs, and reputational damage with lasting effects on its business.
OT Security as Competitive Advantage
Forward-thinking organizations are recognizing that robust OT security can provide competitive advantages:
- Enhanced reliability and uptime compared to competitors
- Ability to meet stringent customer and partner security requirements
- Lower insurance premiums through demonstrated security controls
- Faster recovery from incidents when they do occur
- Protection of intellectual property and proprietary processes
As industrial organizations increasingly compete on operational excellence, the ability to maintain secure and resilient OT environments becomes a key differentiator in the marketplace.
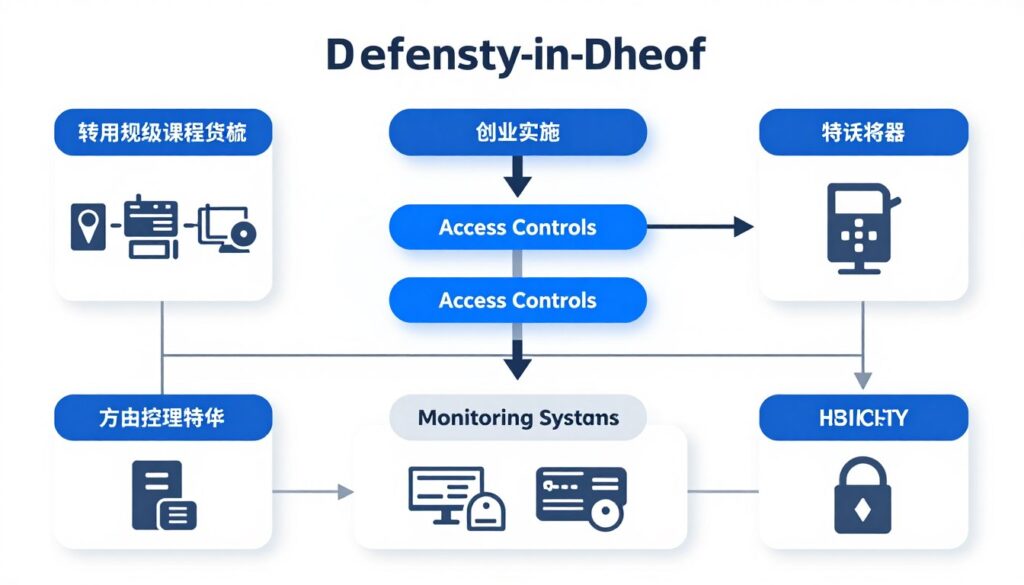
OT Security Best Practices
Implementing effective OT security requires a specialized approach that balances security requirements with operational priorities. The following best practices provide a foundation for robust OT security programs.
Asset Inventory and Visibility
You can’t protect what you don’t know exists. A comprehensive inventory of all OT assets is the foundation of effective security.
- Identify and document all OT devices, systems, and communication paths
- Maintain information on firmware versions, configurations, and patch levels
- Understand the criticality and risk profile of each asset
- Implement tools for continuous asset discovery and monitoring
- Document system interdependencies and communication flows
Network Segmentation and Access Control
Properly segmenting OT networks from IT networks and implementing strict access controls is essential for limiting attack surfaces.
- Implement industrial demilitarized zones (IDMZs) between IT and OT networks
- Use firewalls and data diodes to control traffic between network segments
- Apply the principle of least privilege for all user and system access
- Implement multi-factor authentication for remote access to OT systems
- Regularly review and validate access control configurations
Vulnerability Management for OT
Managing vulnerabilities in OT environments requires specialized approaches that respect operational constraints.
- Establish a risk-based approach to vulnerability prioritization
- Implement compensating controls when patching is not immediately possible
- Coordinate patching activities with planned maintenance windows
- Test patches in non-production environments before deployment
- Maintain secure backup configurations for all critical systems
Monitoring and Threat Detection
Continuous monitoring of OT networks and systems is crucial for detecting and responding to security incidents.
- Implement OT-specific monitoring tools that understand industrial protocols
- Establish baselines of normal operational behavior
- Monitor for unauthorized changes to control system configurations
- Develop alerts for anomalous activity that could indicate compromise
- Integrate OT security monitoring with broader security operations
OT Security Frameworks and Standards
Several frameworks provide structured approaches to OT security:
- NIST Cybersecurity Framework (CSF) – Flexible framework applicable to OT environments
- IEC 62443 – Comprehensive standards specifically for industrial automation and control systems
- MITRE ATT&CK for ICS – Tactics and techniques used by adversaries targeting industrial control systems
Emerging Trends in OT Security
The OT security landscape continues to evolve as technologies advance and threat actors develop new capabilities. Understanding emerging trends is essential for forward-looking security planning.

AI and Machine Learning for OT Security
Artificial intelligence and machine learning are increasingly being applied to OT security challenges:
- Anomaly detection based on learned patterns of normal operation
- Predictive analytics to identify potential security issues before they manifest
- Automated response capabilities for known threat patterns
- Enhanced visibility into complex industrial environments
- Reduction of false positives in security monitoring
Zero Trust Architecture for OT
The zero trust security model is being adapted for OT environments:
- Verification of all access requests regardless of source
- Micro-segmentation of OT networks for granular control
- Continuous monitoring and validation of security posture
- Least privilege access for all users and systems
- Integration of OT identity and access management with enterprise systems
Cloud Integration and OT Security
As OT systems increasingly leverage cloud capabilities, new security considerations emerge:
- Secure cloud-based monitoring and analytics for industrial systems
- Edge computing security for industrial applications
- Hybrid security models spanning on-premises and cloud environments
- Secure remote access through cloud-based services
- Data protection for OT information stored or processed in the cloud
These emerging trends highlight the dynamic nature of OT security and the need for organizations to continuously evolve their security strategies to address new technologies and threats.
Conclusion: The Imperative of OT Security
The importance of OT security cannot be overstated in today’s interconnected industrial landscape. As digital transformation continues to blur the lines between IT and OT environments, the security of operational technology has become fundamental to organizational resilience, public safety, and national security.

The unique characteristics of OT environments—including legacy systems, extended lifecycles, and direct physical impacts—require specialized security approaches that balance cybersecurity requirements with operational priorities. Organizations must recognize that traditional IT security tools and processes, while valuable, are insufficient for protecting industrial control systems and other OT assets.
As threat actors continue to demonstrate both the capability and intent to target critical infrastructure, proactive OT security has become an essential business function rather than an optional technical consideration. The potential consequences of OT security failures—from safety incidents and environmental damage to business disruption and reputational harm—make this a C-suite and board-level concern.
By implementing comprehensive OT security programs based on industry best practices and frameworks, organizations can protect their critical operations, ensure business continuity, and contribute to the broader security of national infrastructure. The investment in OT security today will pay dividends in operational resilience and risk reduction for years to come.
Secure Your Critical OT Infrastructure
Our team of OT security experts can help you assess your current security posture and develop a tailored strategy to protect your industrial control systems from evolving threats. Contact us today for a complimentary consultation.
Frequently Asked Questions About OT Security
What are the main differences between IT and OT security?
The main differences lie in their priorities and operational contexts. IT security focuses primarily on data protection with the CIA triad (Confidentiality, Integrity, Availability) as its guiding principle. OT security, however, prioritizes safety and availability first, following the SAIC model (Safety, Availability, Integrity, Confidentiality). OT systems often have extended lifecycles (15-20 years vs. 3-5 years for IT), cannot tolerate downtime, and have direct physical impacts when compromised. These differences necessitate specialized security approaches for OT environments.
What industries are most affected by OT security concerns?
Industries with significant physical infrastructure and industrial control systems face the greatest OT security challenges. These include energy (power generation and distribution, oil and gas), manufacturing, water and wastewater treatment, transportation (railways, airports, maritime), healthcare (medical devices and building systems), and chemical processing. Any sector that relies on operational technology to control physical processes needs to prioritize OT security.
How does IT-OT convergence affect security?
IT-OT convergence creates both opportunities and challenges for security. While it enables valuable capabilities like remote monitoring, predictive maintenance, and operational analytics, it also expands the attack surface by connecting previously isolated systems to networks. This convergence requires organizations to implement security controls that protect the integrated environment while respecting the unique requirements of OT systems. Successful security in converged environments requires collaboration between IT and OT teams with a shared understanding of risks and priorities.
What are the most common attack vectors for OT systems?
Common attack vectors include remote access connections, compromised credentials, phishing attacks targeting operational staff, supply chain compromises affecting OT components, and exploitation of unpatched vulnerabilities in legacy systems. Attackers often gain initial access through IT networks and then pivot to OT environments, highlighting the importance of network segmentation and access controls between these domains.
What standards and frameworks guide OT security implementation?
Several frameworks provide structured approaches to OT security. The NIST Cybersecurity Framework (CSF) offers a flexible approach applicable to OT environments. IEC 62443 provides comprehensive standards specifically for industrial automation and control systems. The MITRE ATT&CK for ICS framework documents tactics and techniques used by adversaries targeting industrial control systems. Organizations often use these frameworks as foundations for developing their OT security programs.
 Read More
Read More