Introduction
In today’s rapidly evolving cyber threat landscape, organizations face constant risks from hackers, malware, ransomware, insider threats, and advanced persistent attacks. Traditional security tools alone are no longer enough to protect sensitive data and critical systems. This is where a Security Operations Center (SOC) plays a vital role.
A SOC acts as the central command hub for cybersecurity, combining skilled professionals, structured processes, and advanced technologies to monitor, detect, investigate, and respond to threats in real time. For modern enterprises, building or outsourcing a SOC is no longer optional — it’s a strategic necessity.

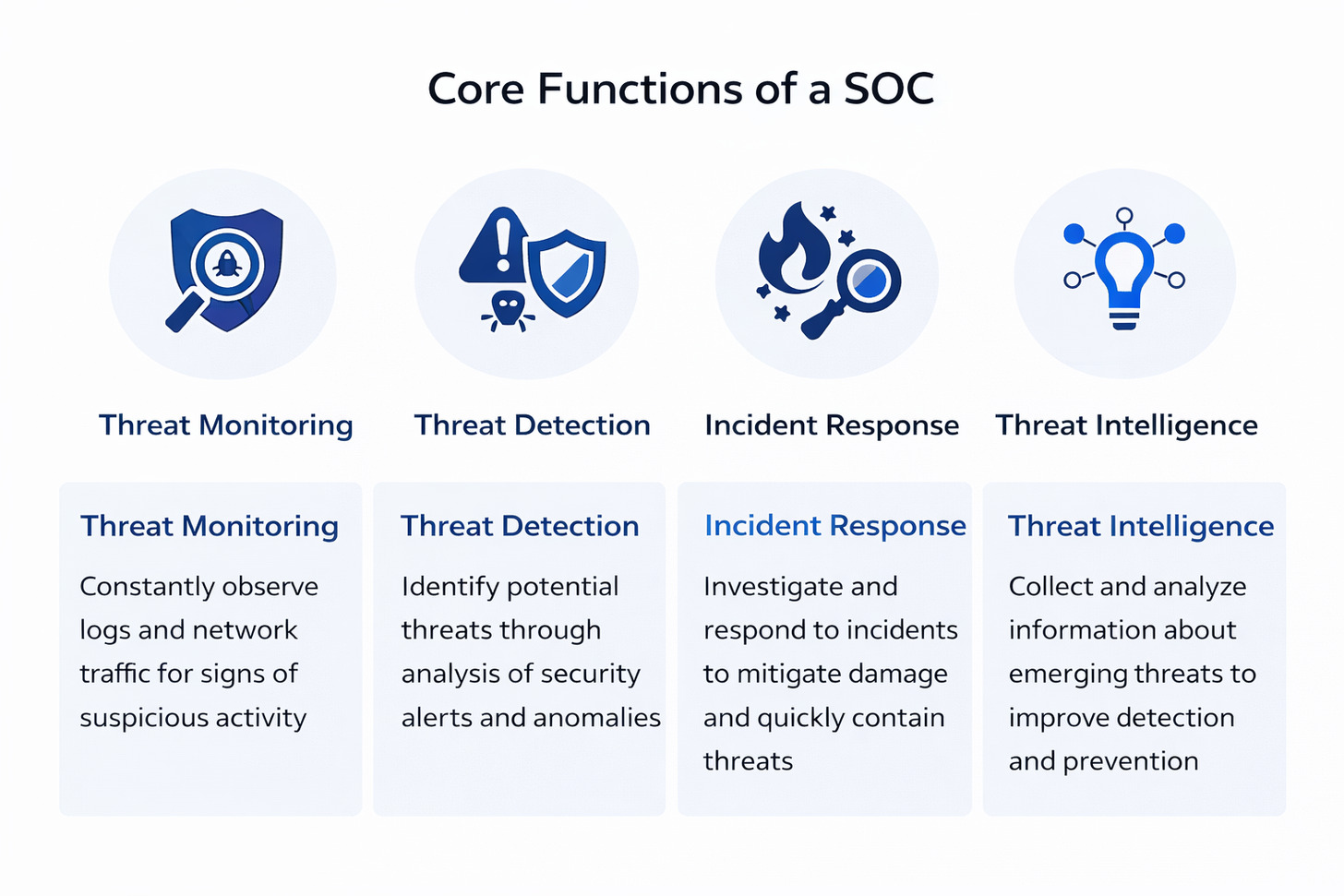
What is a Security Operations Center (SOC)?
A Security Operations Center is a dedicated team and infrastructure responsible for continuously monitoring an organization’s IT environment to identify suspicious activities and respond to security incidents.
Think of a SOC as:
The control room of cybersecurity, where analysts watch dashboards, investigate alerts, and act immediately when threats appear.
 Architecture of an Effective SOC
Architecture of an Effective SOC
People
Skilled security analysts, engineers, and managers with specialized expertise in threat detection, incident response, and security management.
Processes
Standardized workflows and procedures for monitoring, incident classification, escalation protocols, and remediation steps.
Technology
Advanced security tools including SIEM, EDR, SOAR, threat intelligence platforms, and network monitoring solutions.
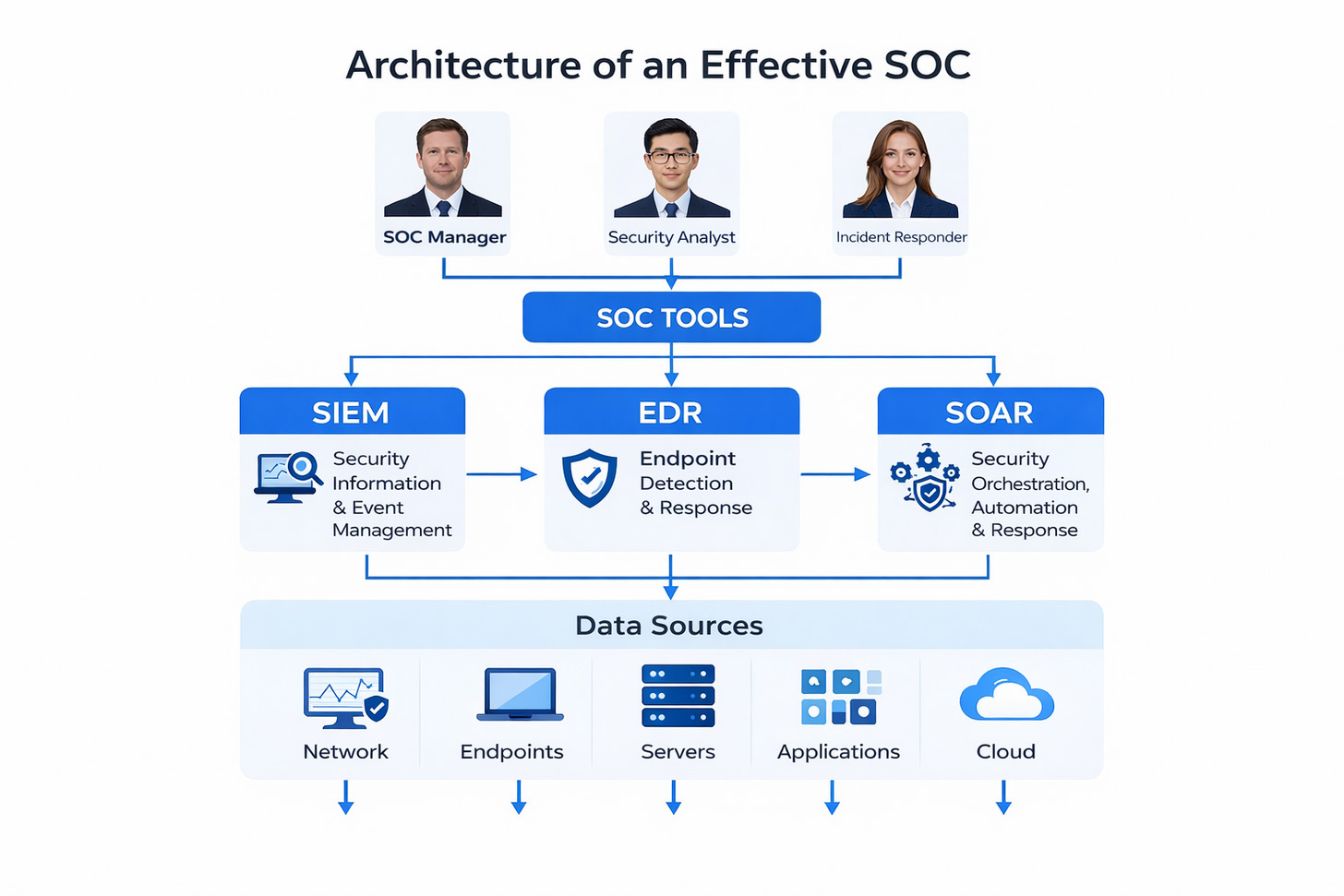
Technology Stack in Modern SOCs
A SOC technology stack is the collection of security platforms, tools, and systems that work together to provide complete visibility across an organization’s IT environment. These tools collect and analyze data from networks, endpoints, applications, and cloud systems to identify suspicious activity and stop attacks before they cause damage.
Rather than operating independently, these tools must be integrated and automated so that security analysts can respond faster and more effectively.
Core Technologies in a Modern SOC
1. Security Information and Event Management (SIEM)
SIEM is the central platform that aggregates logs and security data from across the organization. It correlates events, detects anomalies, and generates alerts for suspicious behavior.
Purpose: Centralized monitoring and threat detection.
2. Endpoint Detection and Response (EDR)
EDR tools monitor endpoint devices such as laptops, servers, and workstations to detect malicious activity.
Key capabilities:
Behavioral monitoring
Malware detection
Attack containment
Forensic investigation
3. Extended Detection and Response (XDR)
XDR expands visibility beyond endpoints to include network traffic, cloud environments, and identity systems. It provides a unified detection and response platform across multiple security layers.
4. Security Orchestration, Automation, and Response (SOAR)
SOAR platforms automate repetitive tasks and coordinate actions across multiple tools.
Benefits:
Automated incident response
Reduced analyst workload
Faster threat containment
Standardized workflows
5. Threat Intelligence Platforms (TIP)
These platforms provide real-time information about emerging threats, attacker tactics, malicious domains, and vulnerabilities. They help SOC teams proactively defend against known threats.
6. Network Detection and Response (NDR)
NDR systems analyze network traffic patterns to identify hidden threats, lateral movement, and command-and-control communications.
7. Vulnerability Management Tools
These tools scan systems for weaknesses such as outdated software, missing patches, or misconfigurations. They help prioritize remediation based on risk level.
8. User and Entity Behavior Analytics (UEBA)
UEBA uses analytics and machine learning to detect abnormal behavior patterns that could indicate insider threats or compromised accounts.
9. Case Management Systems
These platforms track security incidents from detection to resolution and enable collaboration between SOC analysts, incident responders, and management teams.
Supporting Security Tools
In addition to core SOC platforms, several supporting technologies enhance detection and defense capabilities:
Intrusion Detection & Prevention Systems (IDS/IPS)
Identity and Access Management (IAM)
Data Loss Prevention (DLP)
Email Security Gateways
Cloud Security Platforms
These tools provide additional layers of visibility and protection.
Key Benefits of Implementing a SOC
1. Real-Time Threat Detection
One of the biggest advantages of a SOC is its ability to detect threats as they happen. Instead of discovering attacks days or weeks later, SOC monitoring tools analyze logs, network traffic, and user activity instantly.
Result: Faster detection reduces the damage caused by cyberattacks.
2. Rapid Incident Response
When a threat is detected, the SOC team immediately investigates and takes action. This includes isolating affected systems, blocking malicious IPs, removing malware, and restoring services.
Impact: Quick response minimizes downtime, financial losses, and data breaches.
3. Continuous Monitoring (24/7 Security)
Cybercriminals don’t follow business hours. A SOC provides round-the-clock monitoring, ensuring threats are identified even outside working hours.
Benefit: Organizations remain protected at all times, including nights, weekends, and holidays.
4. Centralized Visibility
A SOC consolidates data from multiple security tools and systems into one unified dashboard. This gives security teams complete visibility into:
Network traffic
User activity
System logs
Application behavior
Advantage: Better visibility leads to faster investigations and more accurate threat analysis.
5. Improved Compliance and Audit Readiness
Many industries must meet regulatory standards such as ISO 27001, PCI-DSS, HIPAA, or GDPR. A SOC helps organizations maintain detailed logs, reports, and incident records needed for compliance audits.
Outcome: Reduced risk of penalties and easier audit preparation.
6. Proactive Threat Hunting
SOC teams don’t just wait for alerts — they actively search for hidden threats within the environment. Using threat intelligence and behavioral analytics, analysts can detect advanced attacks that bypass traditional security tools.
Value: Threats are eliminated before they escalate.
7. Reduced False Positives
Modern SOC tools use correlation engines, AI, and behavioral analytics to filter out unnecessary alerts.
Benefit: Analysts focus only on genuine threats instead of wasting time on harmless events.
8. Stronger Incident Documentation & Forensics
A SOC maintains detailed records of security incidents, including timelines, attack methods, and response actions. This data is valuable for:
Root cause analysis
Legal investigations
Future prevention strategies
9. Enhanced Business Continuity
Cyberattacks can disrupt operations, damage reputation, and cause financial losses. With a SOC in place, organizations can detect and contain threats quickly, ensuring minimal disruption.
Result: Stable operations and customer trust.
10. Cost Efficiency in the Long Run
While implementing a SOC requires investment, it ultimately saves money by preventing breaches, reducing downtime, and avoiding regulatory fines.
Reality: The cost of a breach is often far higher than the cost of prevention.
Types of Security Operations Centers
Organizations can implement different SOC models based on their specific needs, resources, and security requirements. Each type offers distinct advantages and considerations.
Internal SOC
A dedicated facility with full-time security staff employed by the organization. Provides complete control over security operations but requires significant investment in personnel, technology, and infrastructure.
Full Control
Virtual SOC
A distributed team of security professionals who may work remotely or part-time. Offers flexibility and reduced infrastructure costs but may have coordination challenges.
Cost-Effective
Outsourced SOC
Security operations handled by a third-party managed security service provider (MSSP). Provides access to specialized expertise without maintaining an in-house team but may have less organizational integration.
Specialized Expertise
Co-Managed SOC
A hybrid approach where internal security staff works alongside external security providers. Combines internal knowledge with external expertise and resources.
Hybrid Approach
Command SOC
Oversees and coordinates multiple SOCs across different locations or business units. Provides centralized management for large, distributed organizations.
Centralized Management
Global SOC
A 24/7 operation with teams in different time zones to provide continuous coverage. Ideal for multinational organizations requiring round-the-clock security monitoring.
24/7 Coverage
Building an Effective SOC Team
The human element is critical to SOC success. A well-structured team with clearly defined roles and responsibilities forms the foundation of effective security operations.

1. SOC Manager
The SOC Manager oversees the entire security operations function. This role focuses on strategy, coordination, and team management.
Responsibilities:
Managing SOC team members
Defining security processes and workflows
Reporting security status to leadership
Ensuring compliance with policies and standards
Coordinating incident response efforts
Skillset: Leadership, risk management, cybersecurity expertise, communication skills.
2. Security Analyst (Tier 1, Tier 2, Tier 3)
Security Analysts are the frontline defenders of the SOC. They monitor alerts, analyze threats, and escalate incidents when needed.
Tier 1 – Monitoring Analysts
Monitor dashboards and alerts
Perform initial triage
Identify false positives
Escalate real threats
Tier 2 – Incident Investigators
Analyze suspicious activities
Conduct deeper investigations
Determine attack scope and impact
Tier 3 – Threat Hunters
Perform advanced threat analysis
Investigate complex attacks
Develop detection strategies
3. Incident Responder
Incident Responders take action once a threat is confirmed. Their goal is to contain and eliminate the threat while minimizing damage.
Responsibilities:
Isolating compromised systems
Blocking malicious traffic
Removing malware
Restoring affected services
Documenting response actions
Key trait: Ability to work under pressure during active attacks.
4. Threat Hunter
Threat Hunters proactively search for hidden threats that automated systems may miss. Instead of waiting for alerts, they investigate suspicious patterns and anomalies.
Responsibilities:
Identifying stealthy attacks
Detecting advanced persistent threats (APTs)
Using threat intelligence for investigations
Creating detection rules
5. Digital Forensics Specialist
Forensics experts investigate security incidents to understand how attacks happened and what data was affected.
Responsibilities:
Collecting digital evidence
Analyzing attack techniques
Determining attack timelines
Supporting legal or compliance investigations
6. SOC Engineer
SOC Engineers maintain and optimize the tools that support security operations.
Responsibilities:
Deploying security tools (SIEM, EDR, SOAR)
Integrating systems
Tuning detection rules
Reducing false positives
Maintaining monitoring infrastructure
7. Threat Intelligence Analyst
These specialists analyze external threat data to help organizations prepare for upcoming threats.
Responsibilities:
Tracking emerging threats
Studying attacker tactics and techniques
Updating threat databases
Providing intelligence reports to analysts
8. Compliance and Reporting Specialist
Some SOC teams include professionals focused on compliance, reporting, and documentation.
Responsibilities:
Generating audit reports
Ensuring regulatory compliance
Maintaining incident logs
Supporting risk assessments
SOC Team Structure and Hierarchy
Most SOCs operate with a tiered structure that allows for efficient incident handling and escalation. This approach ensures that security events are addressed at the appropriate level of expertise.
| Tier Level | Primary Responsibilities | Required Skills |
| Tier 1 | Alert monitoring, initial triage, basic incident handling, ticket creation | Basic security knowledge, familiarity with SIEM tools, good communication skills |
| Tier 2 | Incident investigation, threat correlation, containment actions, remediation planning | Advanced security knowledge, incident response experience, malware analysis |
| Tier 3 | Advanced threat handling, forensic analysis, threat hunting, security tool optimization | Expert-level security knowledge, forensics expertise, programming skills |
| Management | Team leadership, resource allocation, strategy development, executive reporting | Leadership experience, security management background, business acumen |
Implementing a SOC: Best Practices
Establishing an effective Security Operations Center requires careful planning and execution. Following industry best practices can help organizations avoid common pitfalls and maximize their security investment.
Key Steps for SOC Implementation
1. Define Objectives and Security Goals
Before building a SOC, organizations must clearly define:
What assets need protection
What threats are most relevant
Compliance requirements
Risk tolerance level
Clear objectives ensure the SOC is aligned with business priorities and security needs.
2. Assess Current Security Posture
A detailed assessment helps identify gaps in existing security controls, tools, and processes.
This includes:
Infrastructure analysis
Vulnerability assessment
Risk evaluation
Existing monitoring capabilities
This step establishes a baseline for SOC design.
3. Choose the Right SOC Model
Organizations must decide which SOC type fits their environment:
In-house SOC
Managed SOC
Hybrid SOC
Virtual SOC
The decision depends on budget, expertise, infrastructure size, and compliance requirements.
4. Design SOC Architecture
SOC architecture defines how systems, tools, and data sources will integrate.
Key components include:
SIEM platform
EDR/XDR solutions
Threat intelligence feeds
Log management systems
Network monitoring tools
A well-designed architecture ensures scalability and visibility.
5. Build the Right Team
A SOC is only as effective as the people running it. Essential roles include:
SOC Manager
Tier 1, 2, 3 Analysts
Incident Responders
Threat Hunters
SOC Engineers
Organizations must also provide continuous training to keep teams updated on emerging threats.
6. Define Processes and Workflows
Standardized procedures ensure consistent and efficient response to incidents.
Important processes include:
Incident detection and triage
Escalation procedures
Threat investigation
Response and remediation
Reporting and documentation
Well-defined workflows reduce response time and improve accuracy.
7. Implement Security Tools and Integrations
Deploy and configure the selected tools, ensuring they integrate properly to share data automatically.
Integration enables:
Centralized visibility
Automated alert correlation
Faster investigations
Reduced manual effort
Without integration, even advanced tools lose effectiveness.
8. Establish Monitoring and Alerting
Set up real-time monitoring dashboards and alert thresholds to detect suspicious activity.
Best practices:
Prioritize high-risk alerts
Filter false positives
Use behavioral analytics
Implement automated responses where possible
9. Develop Incident Response Plan
An incident response plan ensures the SOC team knows exactly what to do during a security incident.
It should define:
Roles and responsibilities
Communication procedures
Containment steps
Recovery actions
Post-incident analysis
10. Test and Optimize the SOC
Before full deployment, organizations must test SOC operations using:
Simulated attacks
Penetration testing
Red team vs blue team exercises
Testing helps identify gaps and refine detection and response capabilities.
11. Continuous Improvement and Monitoring
Cybersecurity is not a one-time setup. SOCs must continuously evolve by:
Updating threat intelligence
Refining detection rules
Training analysts
Reviewing incidents
Adapting to new threats
Continuous improvement ensures long-term effectiveness.
SOC vs. NOC: Understanding the Differences
Security Operations Centers (SOCs) and Network Operations Centers (NOCs) serve different but complementary functions within an organization’s IT infrastructure. While they share some similarities, their focus, objectives, and expertise differ significantly.
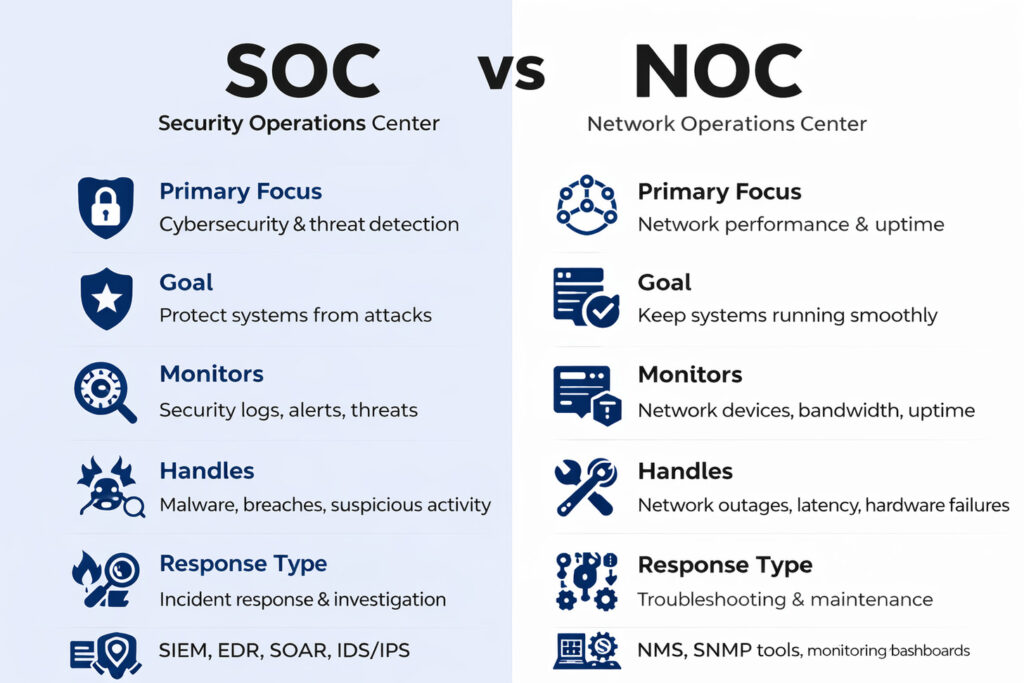
| Aspect | Security Operations Center (SOC) | Network Operations Center (NOC) |
| Primary Focus | Security threats, vulnerabilities, and incidents | Network performance, availability, and reliability |
| Key Objectives | Protect against cyber threats and data breaches | Ensure network uptime and performance |
| Primary Tools | SIEM, EDR, threat intelligence, vulnerability scanners | Network monitoring, performance management, ticketing systems |
| Incident Types | Malware infections, unauthorized access, data exfiltration | Outages, bandwidth issues, hardware failures |
| Team Expertise | Cybersecurity, threat analysis, incident response | Network engineering, systems administration, IT operations |
Integration of SOC and NOC Functions
While SOCs and NOCs have distinct responsibilities, many organizations are finding value in closer integration between these functions. This collaboration can lead to more efficient operations and improved security posture.
Benefits of SOC-NOC Integration
- Faster identification of security incidents that impact network performance
- Improved coordination during incident response
- Shared visibility into both security and operational events
- More efficient use of resources and technologies
- Comprehensive protection of critical business services
Integration Approaches
- Co-located teams with shared workspace
- Integrated toolsets with common dashboards
- Unified incident management processes
- Cross-training of personnel
- Joint planning and strategy development
Evolving Trends in Modern SOCs
The Security Operations Center landscape continues to evolve in response to changing threats, technologies, and business requirements. Understanding these trends can help organizations future-proof their security operations.

AI and Machine Learning
Advanced analytics capabilities are transforming SOCs by improving threat detection, reducing false positives, and enabling more efficient incident triage. AI-powered systems can identify patterns and anomalies that might be missed by traditional rule-based approaches.
Automation and Orchestration
SOAR platforms are automating routine security tasks and orchestrating complex response workflows. This allows SOC teams to handle more incidents with the same resources and respond more quickly to emerging threats.
Cloud-Native Security
As organizations migrate to cloud environments, SOCs are adapting to monitor and protect cloud resources. This includes implementing cloud security posture management and developing expertise in cloud-specific threats.
Extended Detection and Response (XDR)
XDR solutions are providing unified visibility across endpoints, networks, cloud workloads, and applications. This comprehensive approach helps SOCs detect and respond to threats more effectively.
Zero Trust Architecture
SOCs are increasingly implementing zero trust principles, which assume no user or system should be trusted by default. This approach requires continuous verification and least-privilege access controls.
Threat Intelligence Integration
Modern SOCs are leveraging threat intelligence to enhance detection capabilities and provide context for security events. This includes both commercial feeds and information sharing within industry groups.
Conclusion: The Future of Security Operations Centers
As cyber threats grow more sophisticated, organizations need intelligent, adaptive Security Operations Centers to stay protected. Atrity supports this need by delivering integrated cybersecurity, cloud, and IT infrastructure solutions that enable proactive threat detection, real-time monitoring, and resilient defense strategies. By combining advanced technology with expert support, Atrity helps businesses build future-ready SOC environments that enhance security, ensure business continuity, and drive digital confidence.
 Read More
Read More