Protect Your Networks with Our Cyber Perimeter Services
With our amazing milestone in perimeter security solutions, from entry-level services to fully-featured security solutions, we can meet your threat protection requirements at the best.
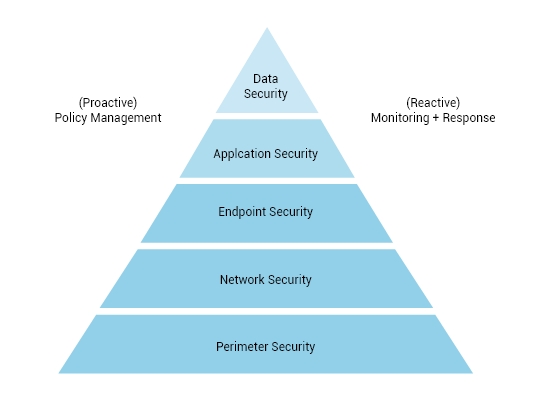
We aim at offering the most effective perimeter defence that includes advanced multi-layered complementary solutions all of which work together for the ultimate protection of your network.
As you choose a perimeter solution at Atrity, you equip your business with a robust security solution that lowers operational costs and eliminates complex management. Our multiple layers of security solutions include threat management, intrusion prevention, web filtering and application control to deny any potential intruder from accessing your network.
We are a team of dedicated perimeter security consultants and engineers passionate about delivering completely bespoke perimeter security solutions to your security-sensitive assets.
Perimeter Security
With our firewall services, browser isolation systems, threat recognition, surveillance detection, pattern analysis, and many other approaches, we strive hard to kick out threats as they enter your network.
SERVICE OFFERINGS
Fenced with Firewall Protection
Before embarking on services implementation, we consider all these accountable factors including the level of protection needed, risk exposure, resources, existing infrastructure, and others.
Starting from design, supply, project management to integration, we travel along with you in every phase, so you can rest assured that you’ve handed over your security concerns to the right partner.

Some of the Networking solutions we provide are:
Build a strong networking infrastructure with Atrity and establish a hassle-free communicative space between your endpoints and users.
- Design & Implementation of LAN/WAN (Structured/Semi-Structured/Normal)
- Network Auditing along with assessment of current setup
- Site Planning via operation research techniques & scheduled cable blueprinting
- Structured Cabling
- Optimization of network resources
- Network Management
- Network Security Planning & Implementation
- Networking Switches
- Switching Rack & Server Rack
- Firewall






INDUSTRIES WE WORK WITH
Breakthrough Cyber Security Technologies
Our cyber security experts at Atrity understand the complexity in any industry and maintain a lasting relationship with each client. We have a dedicated cybersecurity team that helps to manage cyber-related threats and challenges with unified solutions, advanced detection, strong domain knowledge, holistic approaches, and advanced technology capabilities.
Technology Demands Innovation.

- Meaningful insights and forward-thinking solutions based on diligent analysis at every step
- Cost-efficient operations, troubleshooting, comprehensive service assurance, and analytics
- Have gone through Technical Assurance Process (TAP) to ensure that our services meet our client’s standards
- Proven capabilities to undertake strategic projects, as well as operational assignments
FAQ
Your Questions Answered.
What is a software-defined perimeter solution?
The software-defined perimeter is comprehensive that incorporates enterprise network security. It provides access only to authorized users and offers cybersecurity and access management solutions designed for modern enterprises.
How do you implement perimeter security?
Planning, assessing the threats, regularly maintaining the site, getting guidelines from the government and respected third parties, and integrating with other security measures, by doing so, we can successfully implement perimeter security.
What is perimeter access control?
Perimeter access control protects external perimeters of a facility, control access to restricted areas, and detect and monitor anomalies. Some of the perimeter access control include fences and walls, pedestrian barriers, vehicle barriers, and so on.
What does perimeter security consist of?
Perimeter security is comprised of systems like firewalls and browser isolation systems. It involves safeguarding a company’s network limits from hackers, intruders, and other unwanted individuals.
How does software-defined perimeter work?
A software-defined perimeter is a framework designed specifically for micro-segment networks that enables encrypted traffic tunnels creating one-to-one network connections between users and resources.
What are the capabilities of a software-defined perimeter solution?
The software allows you to shift workloads as needed from cloud to cloud inorder to avoid the threat of cloud vendor lock-in. Also, it eliminates chaos by allowing for installation on any host without network reconfiguration or appliance hassles.
 Read More
Read More